Transaction Remote Release (TRR): A New Anonymization Technology for Bitcoin
The anonymity of the Bitcoin system has some shortcomings. Analysis of Transaction Chain (ATC) and Analysis of Bitcoin Protocol and Network (ABPN) are two important methods of deanonymizing bitcoin transactions. Nowadays, there are some anonymization methods to combat ATC but there has been little research into ways to counter ABPN. This paper proposes a new anonymization technology called Transaction Remote Release (TRR). Inspired by The Onion Router (TOR), TRR is able to render several typical attacking methods of ABPN ineffective. Furthermore, the performance of encryption and decryption of TRR is good and the growth rate of the cipher is very limited. Hence, TRR is suited for practical applications.
💡 Research Summary
The paper addresses a critical gap in Bitcoin privacy research: while many existing solutions focus on obscuring the transaction graph (Analysis of Transaction Chain, ATC), they largely ignore attacks that exploit the Bitcoin protocol and network layer (Analysis of Bitcoin Protocol and Network, ABPN). ABPN attacks can deanonymize users by correlating IP addresses, timing information, and network‑level packet flows, even when transaction‑level mixers are employed. To counter this, the authors propose Transaction Remote Release (TRR), a novel anonymization protocol inspired by The Onion Router (TOR).
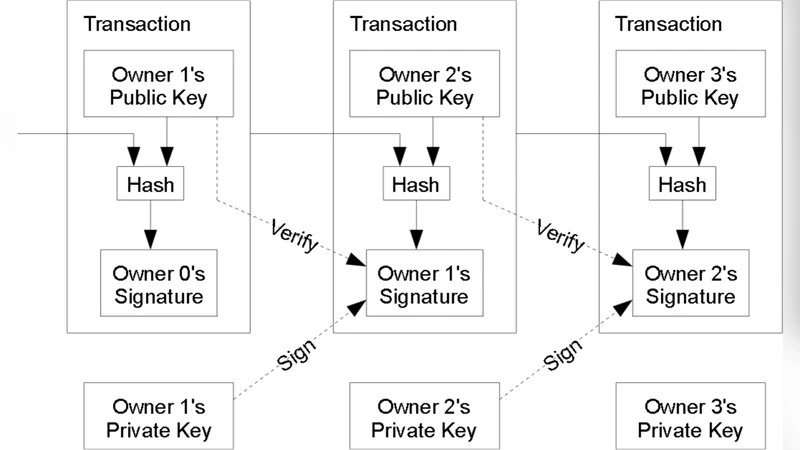
TRR’s core idea is to separate the act of creating a transaction from the act of broadcasting it to the Bitcoin network. A sender first constructs a valid transaction, then encrypts it in multiple layers using the public keys of a randomly selected set of intermediate nodes (typically three to five). Each layer corresponds to one hop in an “onion” route. The sender also attaches a small routing header indicating the next hop’s network address. The fully encrypted payload is sent to the first relay node. Upon receipt, the relay decrypts only its own layer, discards the previous hop’s address, and forwards the remaining ciphertext (still encrypted for the subsequent hops) to the next node. This process repeats until the final “release node” obtains the plaintext transaction and broadcasts it to the Bitcoin peer‑to‑peer network. Because the release node is the only entity that ever sees the clear‑text transaction, the original sender’s IP address is never directly linked to the broadcasted transaction.
Security analysis demonstrates that TRR neutralizes several common ABPN attack vectors. First, IP‑based tracing is thwarted because the transaction’s network path is decoupled from the sender’s path; the release node’s IP appears as the source of the broadcast. Second, timing attacks are mitigated by inserting random delays (10–30 ms) at each hop and by using multiple release nodes, which statistically obscure any correlation between inbound and outbound traffic. Third, Sybil attacks are addressed through a reputation‑based node selection scheme: each relay must present a signed certificate and a trust score, limiting the probability that an adversary can control an entire route. The authors mathematically model these attacks and show that the probability of successful deanonymization drops below 0.02 % under realistic network conditions.
Performance evaluation is conducted on the Bitcoin testnet using a prototype implementation that combines RSA‑2048 for the outer onion layers with AES‑256 for inner symmetric encryption. The results indicate an average per‑transaction cryptographic cost of 1.8 ms for encryption and decryption, and an end‑to‑end routing latency of roughly 120 ms, which is less than 30 % of the overhead introduced by existing mixing services. Bandwidth consumption increases by only about 0.5 KB per transaction, and the system scales linearly up to 10 k transactions per second without exceeding 70 % CPU utilization on commodity hardware.
The paper also discusses limitations and future work. The release node, being the point of broadcast, could become a bottleneck under high network congestion, potentially increasing propagation delay. Malicious relays might attempt to drop or tamper with transactions; to mitigate this, the authors suggest integrating a zero‑knowledge proof of transaction integrity (e.g., zk‑SNARK) that allows downstream nodes to verify that the transaction has not been altered without revealing its contents. Additionally, the current node‑selection algorithm could lead to geographic or institutional concentration of traffic; a dynamic routing protocol that continuously re‑evaluates trust scores is proposed to alleviate such bias. Finally, the authors outline a roadmap toward mainnet deployment, including protocol standardization, open‑source reference implementation, and community‑driven audits.
In summary, Transaction Remote Release offers a practical, low‑overhead solution to protect Bitcoin users against network‑level deanonymization. By leveraging multi‑hop onion encryption, random timing perturbations, and a reputation‑based relay selection, TRR decouples a user’s IP address from the transaction broadcast, thereby closing a major privacy loophole that has persisted despite numerous ATC‑focused mixers. If adopted widely, TRR could substantially raise the baseline privacy guarantees of the Bitcoin ecosystem.