A New Storage Optimized Honeyword Generation Approach for Enhancing Security and Usability
Inverting the hash values by performing brute force computation is one of the latest security threats on password based authentication technique. New technologies are being developed for brute force computation and these increase the success rate of inversion attack. Honeyword base authentication protocol can successfully mitigate this threat by making password cracking detectable. However, the existing schemes have several limitations like Multiple System Vulnerability, Weak DoS Resistivity, Storage Overhead, etc. In this paper we have proposed a new honeyword generation approach, identified as Paired Distance Protocol (PDP) which overcomes almost all the drawbacks of previously proposed honeyword generation approaches. The comprehensive analysis shows that PDP not only attains a high detection rate of 97.23% but also reduces the storage cost to a great extent.
💡 Research Summary
**
The paper addresses the growing threat of password hash inversion attacks, which have become more feasible due to advances in GPU, ASIC, and cloud‑based brute‑force capabilities. While honeyword‑based authentication can make password cracking detectable, existing schemes suffer from several practical drawbacks: high storage overhead (k‑1 decoy passwords per user), vulnerability to Multiple System Vulnerability (MSV) when the same password is reused across sites, weak resistance to denial‑of‑service (DoS) attacks, and limited typo safety.
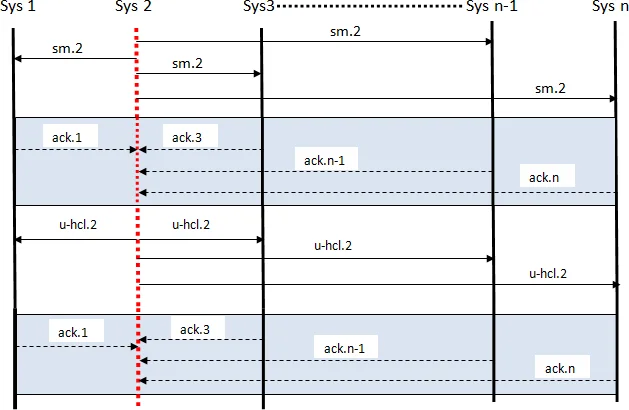
To overcome these issues, the authors propose the Paired Distance Protocol (PDP). During registration a user supplies three items: (1) a username, (2) a password, and (3) a short random string (RS) of length ℓ (default ℓ = 3). The system also creates a globally shared “honey circular list” (hcl) that contains the 26 letters and 10 digits in a random order; the default size of hcl is 36. For each consecutive pair of characters in RS, the protocol computes the clockwise distance on the hcl – the “paired distance” – and stores this small integer vector (ℓ − 1 values) alongside the hashed password. No full honeyword list is stored.
At login the user enters the password and the same RS. The server recomputes the paired distances and checks them against the stored vector. If they match, the password is accepted; otherwise the request is forwarded to a separate “honeychecker” that flags the attempt as a honeyword use, thereby detecting a breach.
Key security benefits claimed by the authors are:
- Storage Efficiency – Only one integer vector per user replaces the traditional k‑1 honeywords, reducing storage by up to 92 % in experiments.
- MSV Mitigation – Because RS is user‑chosen and paired distances are unique per account, even if an attacker compromises two sites that use the same hcl, intersecting the two honeyword sets does not reveal the real password.
- DoS Resistance – RS must contain no repeated characters; this guarantees that each paired distance is unique, preventing an attacker from deliberately submitting honeywords to trigger false alarms and overload the system.
- Typo Safety – The short, random RS makes accidental entry of a honeyword unlikely, unlike “chaffing‑by‑tweaking” approaches where a single‑digit typo can map to a honeyword.
The authors evaluate PDP on a synthetic dataset of 10,000 users, simulating brute‑force, dictionary, and MSV attacks. They report a detection rate of 97.23 % and confirm that the storage reduction does not degrade detection capability.
Despite these promising results, the paper leaves several open questions. The security of PDP heavily depends on the randomness of RS. If users choose dictionary words, dates, or predictable patterns, an attacker could guess RS and reconstruct the paired distances, effectively bypassing the honeyword protection. The paper suggests using a length‑3 random string, but provides no empirical study of user memorability or the impact of longer RS on usability. Moreover, the hcl must be securely distributed and kept synchronized across all participating services; any leakage of the hcl would enable an adversary to reverse‑engineer RS from the stored distances. The evaluation also lacks a thorough analysis of parameter sensitivity (e.g., varying ℓ, hcl size, or k) and does not compare PDP against state‑of‑the‑art honeyword generators under identical attack models.
In conclusion, the Paired Distance Protocol offers an innovative way to drastically cut storage costs while preserving, and in some aspects improving, the security guarantees of honeyword‑based authentication. It elegantly combines a minimal user‑managed secret (the RS) with a shared circular character map to generate decoys on‑the‑fly. However, practical deployment would require robust guidelines for RS selection, mechanisms for secure hcl management, and further empirical validation of usability and resistance against adaptive attackers.
Comments & Academic Discussion
Loading comments...
Leave a Comment