Fast Sequence Component Analysis for Attack Detection in Synchrophasor Networks
Modern power systems have begun integrating synchrophasor technologies into part of daily operations. Given the amount of solutions offered and the maturity rate of application development it is not a matter of “if” but a matter of “when” in regards to these technologies becoming ubiquitous in control centers around the world. While the benefits are numerous, the functionality of operator-level applications can easily be nullified by injection of deceptive data signals disguised as genuine measurements. Such deceptive action is a common precursor to nefarious, often malicious activity. A correlation coefficient characterization and machine learning methodology are proposed to detect and identify injection of spoofed data signals. The proposed method utilizes statistical relationships intrinsic to power system parameters, which are quantified and presented. Several spoofing schemes have been developed to qualitatively and quantitatively demonstrate detection capabilities.
💡 Research Summary
The paper addresses the growing security concerns associated with the integration of synchrophasor (PMU) technology into modern power grids. Recognizing that deceptive data injection—commonly referred to as spoofing—can undermine operator‑level applications, the authors propose a detection framework that leverages intrinsic statistical relationships among PMU measurements. First, they compute Pearson correlation coefficients both within a single PMU (intra‑PMU) and between electrically adjacent PMUs (inter‑PMU). Intra‑PMU analysis reveals that most parameter pairs (e.g., voltage magnitude vs. ROCOF) exhibit near‑zero correlation, while phase angles of sequence components show moderate to strong correlation. Inter‑PMU analysis identifies three correlation streams—positive‑sequence voltage magnitude (|V⁺|), its phase angle (φ⁺), and system frequency (f)—as consistently high under normal operation (r≈0.7–1.0).
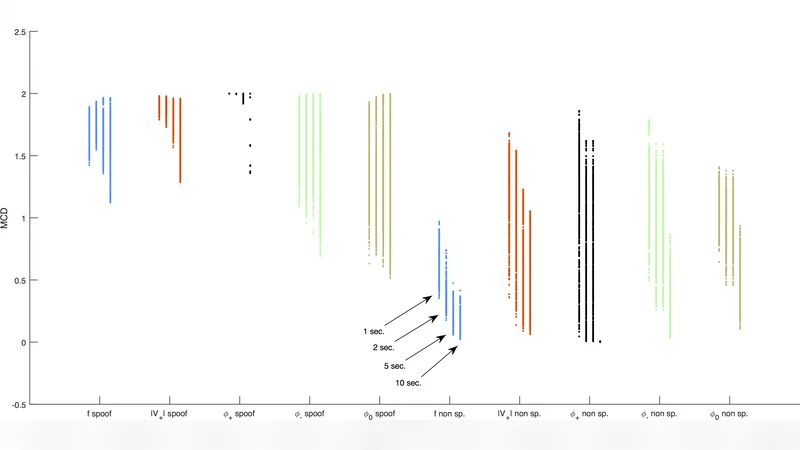
To emulate realistic attacks, three spoofing schemes are constructed: (S1) mirroring the first 30 s of data in reverse, (S2) fitting a third‑order polynomial plus noise, and (S3) time‑dilation of a 60 s record to produce a stretched 30 s segment. Each scheme preserves signal continuity at the injection point but quickly degrades the correlation with the nine neighboring PMUs. Two quantitative metrics are introduced: Maximum Correlation Deviation (MCD) and Maximum Correlation Out‑Of‑Bounds time (MCOOB), which capture the magnitude and duration of decorrelation, respectively. Experiments on a real BPA dataset—10 closely spaced PMUs sampled at 60 fps, generating roughly 1.2 TB per month—show that both MCD and MCOOB separate spoofed from normal data across multiple window lengths (1–10 s).
For automated detection, the authors train binary Support Vector Machines (SVMs) using correlation vectors as features. Two feature sets are evaluated: a three‑feature set (|V⁺|, φ⁺, f) and a five‑feature set (adding φ⁻ and φ⁰). Individual SVMs achieve high detection rates for the specific spoof type they are trained on but struggle with unseen attack patterns. To improve robustness, an ensemble of SVMs is constructed, allowing collective voting across models. The ensemble demonstrates superior performance on a held‑out test set, achieving lower false‑positive rates and higher true‑positive rates for novel spoofing scenarios.
The study concludes that monitoring inter‑PMU correlation—particularly frequency correlation—provides a rapid and reliable indicator of spoofing, and that a machine‑learning‑based ensemble can scale to the massive data volumes typical of wide‑area PMU deployments. The proposed methodology offers a practical pathway toward real‑time integrity verification in future smart‑grid control centers.
Comments & Academic Discussion
Loading comments...
Leave a Comment