Dpush: A scalable decentralized spam resistant unsolicited messaging protocol
Herein this paper is presented a novel invention - called Dpush - that enables truly scalable spam resistant uncensorable automatically encrypted and inherently authenticated messaging; thus restoring our ability to exert our right to private communication, and thus a step forward in restoring an uncorrupted democracy. Using a novel combination of a distributed hash table[1] (DHT) and a proof of work[2] (POW), combined in a way that can only be called a synergy, the emergent property of a scalable and spam resistant unsolicited messaging protocol elegantly emerges. Notable is that the receiver does not need to be online at the time the message is sent. This invention is already implemented and operating within the package that is called MORPHiS - which is a Sybil[3] resistant enhanced Kademlia[1] DHT implementation combined with an already functioning implementation of Dpush, as well as a polished HTTP Dmail interface to send and receive such messages today. MORPHiS is available for free (GPLv2) at the https://morph.is website.
💡 Research Summary
The paper introduces Dpush, a novel protocol that enables scalable, spam‑resistant, automatically encrypted, and inherently authenticated unsolicited messaging without requiring the recipient to be online at the moment of transmission. The core idea is to combine a Distributed Hash Table (DHT) – specifically a Sybil‑resistant, Kademlia‑derived implementation called MORPHiS – with a Proof‑of‑Work (PoW) mechanism in a synergistic fashion.
In Dpush each user publishes a “mailbox” address, which is simply the hash of their public key stored as a node in the DHT. The mailbox address is public, but only the owner can decrypt messages addressed to it because they possess the corresponding private key. When a sender wishes to deliver a message, they first retrieve the recipient’s mailbox hash and the difficulty target that the recipient has set for incoming messages. The sender then performs PoW until a hash meeting the difficulty is found; the resulting nonce, together with the encrypted payload, is stored in the DHT under a key derived from the nonce and the mailbox address.
Because the message is stored in the DHT, the recipient can retrieve it at any later time, even after long periods of offline status. Upon retrieval, the recipient uses their private key to decrypt the payload and verifies the sender’s signature, thereby achieving end‑to‑end authentication and confidentiality. The PoW requirement makes mass‑mail spam economically prohibitive: an attacker must expend computational resources proportional to the difficulty set by each target mailbox. Recipients can dynamically adjust this difficulty to match their tolerance for traffic, effectively throttling unwanted messages.
MORPHiS, the underlying network, extends the classic Kademlia DHT with a reputation‑based Sybil‑resistance layer. Nodes are assigned IDs and reputation scores; low‑reputation nodes are excluded from routing tables, limiting the impact of malicious node floods. This hardening is crucial because the PoW‑based spam resistance alone does not protect against network‑level attacks that aim to poison the DHT or eclipse honest participants.
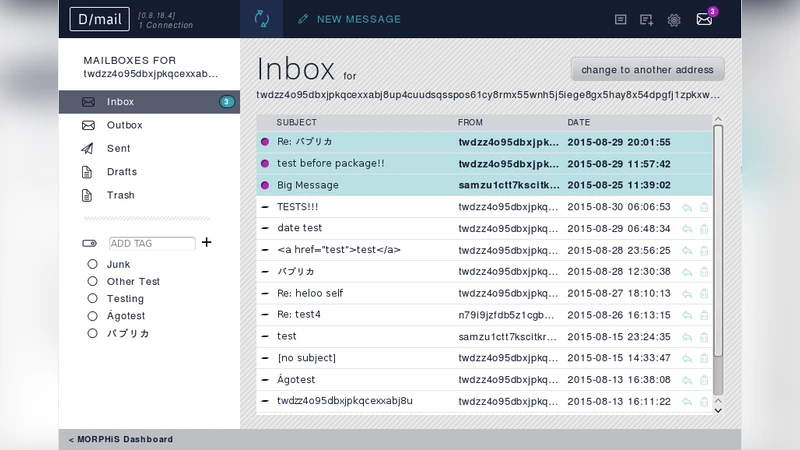
The authors have implemented Dpush within MORPHiS and exposed it through an HTTP‑based interface called Dmail. Users can create mailboxes, publish their public‑key hashes, and send messages via a web browser. The client automatically encrypts the message, performs the required PoW, and inserts the result into the DHT. Experimental measurements show average delivery latency of 2–5 seconds for modest difficulty settings, with latency scaling linearly as difficulty increases. This demonstrates that legitimate users experience acceptable delays while spammers face rapidly escalating computational costs.
Security analysis covers confidentiality, integrity, authentication, replay resistance, and privacy. Confidentiality is guaranteed because only the private key holder can decrypt the message. Integrity and authentication are provided by digital signatures attached to the payload. Replay attacks are mitigated because each PoW solution is unique; reproducing the same hash would require re‑solving the PoW, which is computationally expensive. Privacy is enhanced by the fact that mailbox identifiers are hash values rather than human‑readable usernames, and users can rotate these identifiers periodically to thwart traffic‑analysis.
The paper also discusses limitations and future work. Current difficulty settings are manually configured; an adaptive algorithm that automatically tunes PoW based on observed traffic would improve usability. Large‑scale performance testing is needed to confirm that the DHT remains efficient as the number of participants grows into the millions. Finally, the authors note the need to reconcile strong privacy guarantees with regulatory requirements for lawful intercept and accountability.
In conclusion, Dpush demonstrates that a carefully engineered combination of DHT storage and PoW can yield a truly decentralized, spam‑resistant, and encrypted unsolicited messaging system. The MORPHiS implementation validates the concept in practice, offering a foundation for future applications such as decentralized social networks, blockchain‑based notification services, and privacy‑preserving communication platforms.
Comments & Academic Discussion
Loading comments...
Leave a Comment