Flip the Cloud: Cyber-Physical Signaling Games in the Presence of Advanced Persistent Threats
Access to the cloud has the potential to provide scalable and cost effective enhancements of physical devices through the use of advanced computational processes run on apparently limitless cyber infrastructure. On the other hand, cyber-physical systems and cloud-controlled devices are subject to numerous design challenges; among them is that of security. In particular, recent advances in adversary technology pose Advanced Persistent Threats (APTs) which may stealthily and completely compromise a cyber system. In this paper, we design a framework for the security of cloud-based systems that specifies when a device should trust commands from the cloud which may be compromised. This interaction can be considered as a game between three players: a cloud defender/administrator, an attacker, and a device. We use traditional signaling games to model the interaction between the cloud and the device, and we use the recently proposed FlipIt game to model the struggle between the defender and attacker for control of the cloud. Because attacks upon the cloud can occur without knowledge of the defender, we assume that strategies in both games are picked according to prior commitment. This framework requires a new equilibrium concept, which we call Gestalt Equilibrium, a fixed-point that expresses the interdependence of the signaling and FlipIt games. We present the solution to this fixed-point problem under certain parameter cases, and illustrate an example application of cloud control of an unmanned vehicle. Our results contribute to the growing understanding of cloud-controlled systems.
💡 Research Summary
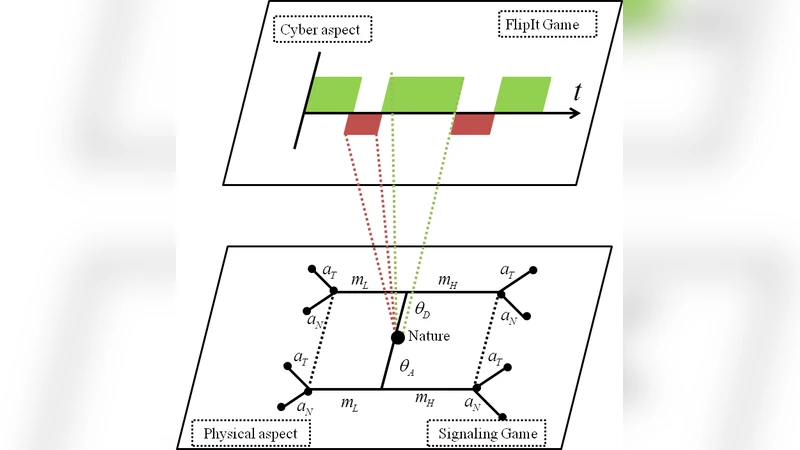
The paper addresses the security challenges of cloud‑enabled cyber‑physical systems (CPS) under Advanced Persistent Threats (APTs). It proposes a unified game‑theoretic framework that couples two well‑studied models: a signaling game describing the interaction between a cloud (which may be benign or compromised) and a device, and a FlipIt game modeling the ongoing contest for control of the cloud between a defender (administrator) and an attacker. In the signaling game, the cloud’s type θ∈{θ_D (defender‑controlled), θ_A (attacker‑controlled)} determines the distribution over two possible messages, high‑risk (m_H) and low‑risk (m_L). The device observes the message and chooses either to trust the cloud (a_T) or to ignore it and rely on its own local controller (a_N). Its decision is based on a prior probability p that the cloud is compromised and a posterior belief µ(θ|m) updated via Bayes’ rule. Expected utilities for the sender (defender or attacker) and the receiver are defined in equations (1) and (2).
The FlipIt game runs in continuous time with periodic strategies: the defender and attacker each choose a move frequency f_D and f_A, respectively. Moves instantly flip control of the cloud; each move incurs a cost α_D or α_A. The long‑run proportion of time each player controls the cloud is w_X, and the average payoff u_FX combines the proportion of control, the payoff from the signaling game (¯u_SD, ¯u_SA), and the move cost. Closed‑form expressions for u_FX are given for the cases f_D ≥ f_A, f_A > f_D, and f_A = 0 (equations (5)–(9)).
The novel contribution is the “Gestalt equilibrium,” a fixed‑point that simultaneously satisfies: (i) the signaling game’s Perfect Bayesian equilibrium utilities as a function of the prior p (mapping T_S), and (ii) the FlipIt game’s Nash equilibrium frequencies as a function of the signaling utilities (mapping T_F). Formally, (¯u_SD, ¯u_SA) ∈ T_S(p) and p = T_F(¯u_SD, ¯u_SA). Solving this fixed‑point yields consistent strategies for all three players despite the fact that strategies are chosen with prior commitment (the signaling game does not observe the outcome of the FlipIt game).
The authors analyze several parameter regimes. When the attacker’s frequency exceeds the defender’s (f_A > f_D), the proportion p of time the cloud is compromised approaches 1, driving the device to always select a_N (ignore the cloud). Conversely, when the defender can move more frequently, p is reduced, and the device may trust the cloud for high‑utility messages. The equilibrium also reveals trade‑offs: higher move costs α_D or α_A discourage frequent flips, potentially allowing the attacker to dominate for longer periods.
A concrete case study examines an unmanned aerial vehicle (UAV) that receives navigation commands from the cloud. If the cloud is compromised, malicious commands could cause a crash. Using realistic parameters for message utilities, move costs, and control‑time fractions, the Gestalt equilibrium predicts that the UAV will switch to its onboard autonomous controller once the attacker’s flip frequency surpasses a threshold. The defender’s optimal response is to increase its flip frequency just enough to keep p below that threshold while minimizing α_D·f_D. Simulations show a marked improvement in safety metrics compared to naïve policies that either always trust the cloud or always ignore it.
In summary, the paper introduces a rigorous, two‑layer game‑theoretic model for cloud‑controlled CPS under APTs, defines a new equilibrium concept to capture the interdependence of signaling and control‑capture dynamics, provides analytical solutions for key regimes, and validates the approach with a UAV control example. The framework offers system designers a principled method to balance the benefits of cloud intelligence against the risks of stealthy, persistent compromise, and could be extended to other domains such as smart grids, autonomous vehicles, and industrial IoT.
Comments & Academic Discussion
Loading comments...
Leave a Comment