A Satisfiability Modulo Theory Approach to Secure State Reconstruction in Differentially Flat Systems Under Sensor Attacks
We address the problem of estimating the state of a differentially flat system from measurements that may be corrupted by an adversarial attack. In cyber-physical systems, malicious attacks can directly compromise the system’s sensors or manipulate the communication between sensors and controllers. We consider attacks that only corrupt a subset of sensor measurements. We show that the possibility of reconstructing the state under such attacks is characterized by a suitable generalization of the notion of s-sparse observability, previously introduced by some of the authors in the linear case. We also extend our previous work on the use of Satisfiability Modulo Theory solvers to estimate the state under sensor attacks to the context of differentially flat systems. The effectiveness of our approach is illustrated on the problem of controlling a quadrotor under sensor attacks.
💡 Research Summary
The paper tackles the problem of reconstructing the state of a differentially flat nonlinear system when a subset of its sensors is compromised by an adversarial attack. While prior work on secure state reconstruction has focused on linear dynamics, this work extends the theory and algorithms to a broad class of nonlinear systems that admit a flat output representation.
The authors first generalize the notion of s‑sparse observability, originally defined for linear systems, to nonlinear dynamics. A system is said to be s‑sparse τ‑observable if it remains observable over a window of length τ when any set of up to s sensors is removed. They prove that 2s‑sparse τ‑observability is both necessary and sufficient for the existence of a solution to the secure state reconstruction problem: if the system satisfies this property, any state estimate that matches the measurements on the presumed attack‑free sensors must coincide with the true state, and the estimated attack support will contain the true attacked sensors. The proof hinges on indistinguishability arguments and a careful counting of the sensors involved.
Next, the paper leverages differential flatness. By definition, a flat system allows the full state and input to be expressed as algebraic functions of a finite number of consecutive output samples. The authors introduce the concept of s‑sparse flatness, which requires that any choice of p‑s sensors (where p is the total number of sensors) constitutes a flat output. They show that s‑sparse flatness automatically implies s‑sparse τ‑observability, thus providing a concrete class of systems for which the theoretical condition holds.
On the algorithmic side, the secure state reconstruction problem is formulated as a mixed Boolean‑continuous constraint satisfaction problem. Boolean variables indicate whether each sensor is under attack, while continuous variables represent the system state. The authors adopt a lazy SMT (Satisfiability Modulo Theory) approach, extending their previous IMHOTEP‑SMT framework. The solver iteratively proposes candidate attack‑free sensor sets (Boolean assignments) and checks feasibility of the corresponding nonlinear equations using a numerical solver. This “guess‑and‑check” strategy avoids exhaustive enumeration of all (\binom{p}{s}) sensor subsets, dramatically reducing computational complexity.
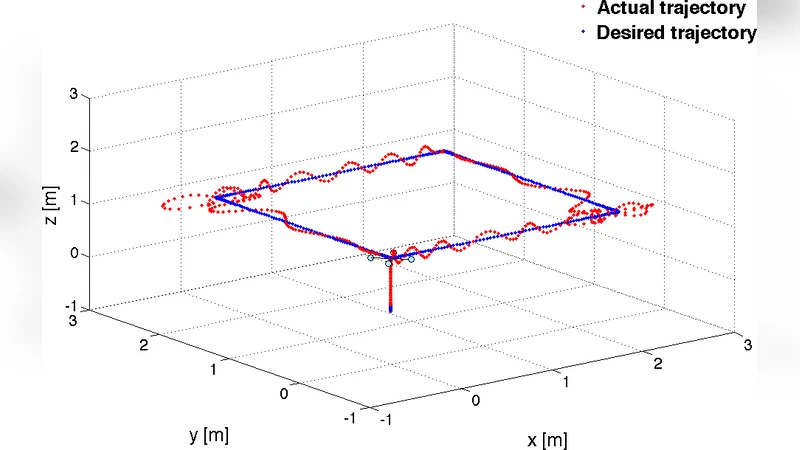
The methodology is validated on a quadrotor model equipped with six sensors (position, orientation, velocities, etc.). Up to two sensors are arbitrarily corrupted with time‑varying, non‑statistical attack signals. The SMT‑based algorithm correctly identifies the compromised sensors and reconstructs the true state within a small error bound, even when the attacks are persistent and unbounded. The experiments demonstrate robustness to attack dynamics, measurement noise, and model uncertainties.
Overall, the paper makes three major contributions: (1) a rigorous extension of s‑sparse observability to nonlinear, differentially flat systems; (2) a proof that 2s‑sparse observability is the exact condition for secure state reconstruction under s‑sparse attacks; and (3) a practical, scalable SMT‑based algorithm that exploits flatness to achieve real‑time attack detection and state estimation. These results broaden the applicability of secure estimation techniques to a wide range of cyber‑physical systems, such as aerial vehicles, ground robots, and other platforms whose dynamics admit a flat representation.
Comments & Academic Discussion
Loading comments...
Leave a Comment