A Typology of Authentication Systems
Authentication systems are designed to give the right person access to an organization’s information system and to restrict it from the wrong person. Such systems are designed by IT professionals to protect an organization’s assets (e.g., the organization’s network, database, or other information). Too often, such systems are designed around technical specifications without regard for the end user. We argue that doing so may actually compromise a system’s security. This paper examines authentication systems from both the point of view of the organization and that of the user.
💡 Research Summary
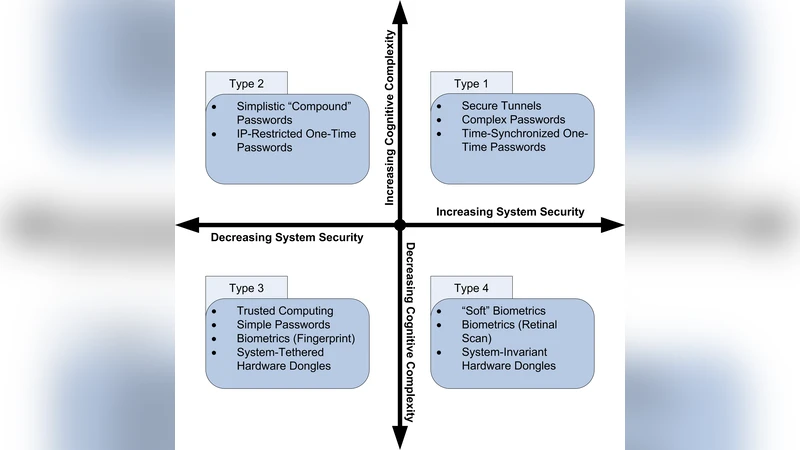
The paper presents a two‑dimensional typology for classifying authentication mechanisms based on (1) the level of security they provide to protect an asset and (2) the cognitive complexity they impose on legitimate users. By plotting these dimensions against each other, the authors define four distinct types.
Type 1 – High Security, High Cognitive Complexity includes mechanisms such as VPN tunnels, highly complex passwords, and time‑synchronized one‑time passwords (OTPs). While these solutions offer strong protection against attackers, they demand substantial memory and procedural effort from users. The resulting cognitive load often leads users to adopt shortcuts—writing passwords on sticky notes, using scripts, or otherwise compromising the very security the system is meant to enforce.
Type 2 – Low Security, High Cognitive Complexity describes systems that provide little resistance to determined attackers yet still burden users with difficult authentication tasks. Examples are simplistic “compound” passwords (two words concatenated to meet length requirements), IP‑restricted OTPs, and any scheme that relies more on obscurity than on genuine cryptographic strength. Because the security payoff is minimal, the high cognitive cost is especially unjustified, making these mechanisms the most dangerous of the four.
Type 3 – Low Security, Low Cognitive Complexity covers solutions that are extremely user‑friendly but offer weak protection. Trusted computing (granting access based on network or physical location), simple passwords (e.g., “1234”), low‑resolution biometrics such as basic fingerprint readers, and hardware dongles that authenticate merely by presence fall into this category. These are appropriate only when ease of access outweighs the need to safeguard valuable assets.
Type 4 – High Security, Low Cognitive Complexity represents the ideal balance: mechanisms that maintain strong security while keeping the user’s mental workload low. The authors cite “soft” biometrics (keystroke dynamics, rhythm, tempo), retinal scanning, and challenge‑response hardware tokens such as RSA SecureID. In these schemes, the secret component is either inherent to the user (retina) or generated dynamically by a token, so the user only needs to remember a short PIN or provide a brief biometric sample.
After defining the typology, the paper evaluates each class with concrete examples, discussing cost, training requirements, and potential failure modes. The authors argue that most real‑world deployments fall short of the ideal Type 4 configuration because of implementation expense, legacy infrastructure, or lack of awareness about cognitive factors.
To operationalize the model, the authors propose empirical methods for measuring cognitive complexity: password recall tests across sessions, observation of password‑writing behavior, and willingness to disclose credentials to third parties. Security can be assessed through standard metrics such as false‑acceptance and false‑rejection rates, but the added human‑centric measurements allow organizations to detect when a technically strong system is being undermined by user behavior.
In the conclusion, the paper stresses that authentication design must balance technical security with human usability. When security is not a primary concern, Type 3 solutions may suffice; when high security is mandatory, organizations should aim for Type 4 or, if resources allow, invest in user training to make Type 1 viable. The authors call for greater integration of Human‑Computer Interaction (HCI) research into security engineering, arguing that ignoring the psychology of users leads to fragile defenses. Overall, the typology provides a practical framework for IT professionals to select, evaluate, and improve authentication mechanisms in line with both asset value and user capabilities.
Comments & Academic Discussion
Loading comments...
Leave a Comment