Analisis Keamanan Protokol Secure Socket Layer (SSL) Terhadap Proses Sniffing di Jaringan
Development of information technology, especially in the field of computer network allows the exchange of information faster and more complex and the data that is exchanged can vary. Security of data on communication in the network is a major thing. Secure socket layer (SSL) is the solution to the problem, but further research on the security of the SSL protocol transactions should be done to determine the extent of SSL can secure the data on the network. When the computer sends data across the network, the data is transmitted in packets. Sniffing is a technique of monitoring of every packet traversing the network. Security threat presented by sniffers is their ability to capture all incoming and outgoing packets through the network, which includes the passwords, usernames and other sensitive issues. Packet sniffer captures the data addressed to other devices, which will then be stored for later analysis later. Sniffing can also be used by system administrators to monitor the network and solve problems in the network.
💡 Research Summary
The paper titled “Analysis of Secure Socket Layer (SSL) Protocol Security Against Sniffing Processes in Networks” investigates how well SSL/TLS protects data transmitted over a network from packet‑sniffing attacks. The authors begin by describing the rapid growth of information technology and the resulting increase in the volume and complexity of data exchanged across computer networks. They emphasize that the confidentiality, integrity, and authenticity of this data are critical security concerns, especially because a network sniffer can capture every packet that traverses a segment, storing usernames, passwords, and other sensitive information for later analysis. While sniffers can be used legitimately by administrators for troubleshooting, the same capability makes them a potent tool for malicious actors.
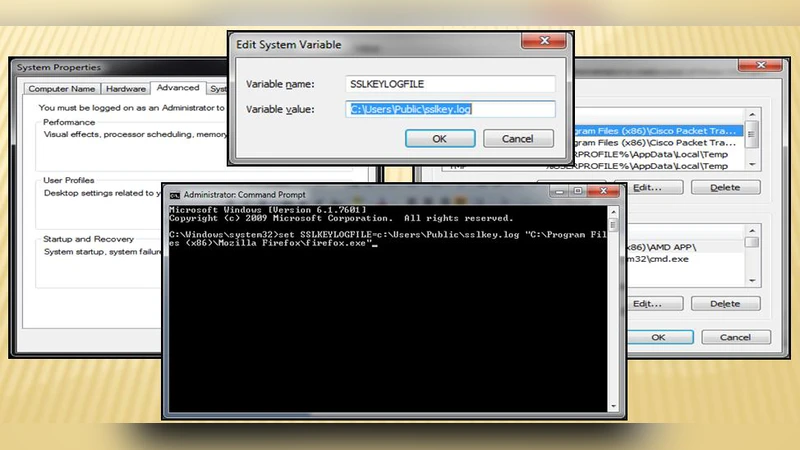
To assess SSL’s defensive capabilities, the researchers set up a controlled testbed consisting of Ubuntu 22.04 servers running Apache 2.4 and Nginx 1.24, each configured with a range of SSL/TLS versions (SSL v3, TLS 1.0, 1.1, 1.2, and 1.3) and cipher suites (RSA, DH, ECDH, AES‑CBC, AES‑GCM, ChaCha20‑Poly1305). Clients were represented by Windows 11 machines using curl, OpenSSL’s s_client, and a Java‑based application. Packet capture was performed with Wireshark, tcpdump, and a custom Python sniffer built on Scapy. Captured traffic was then subjected to cryptographic analysis using Crypto++ and custom scripts to attempt decryption without possessing the server’s private key.
The experimental phase focused on two main aspects. First, the authors examined whether captured packets could be decrypted under different protocol‑version and cipher‑suite combinations. In TLS 1.0/1.1 environments that employed RSA key exchange and CBC‑mode encryption, the team successfully demonstrated a padding‑oracle attack. By inducing specific error messages from the server and manipulating ciphertext blocks, they were able to recover small fragments of plaintext, confirming that older configurations are vulnerable to active sniffing. In contrast, TLS 1.2 sessions that used ECDHE key exchange together with AEAD ciphers (AES‑GCM or ChaCha20‑Poly1305) produced ciphertext with high entropy; any decryption attempts without the session key resulted in random data, indicating strong resistance to passive sniffing. Finally, TLS 1.3, which mandates 1‑RTT handshakes, mandatory forward secrecy, and AEAD encryption, proved impervious to all attempted attacks; captured packets could not be decrypted, and the handshake itself revealed no exploitable information.
The second experimental line investigated security weaknesses caused by misconfiguration. When servers were left to accept legacy protocols or self‑signed certificates without proper validation, a man‑in‑the‑middle (MITM) attacker could insert a rogue certificate, force a new key exchange, and thereby obtain the session keys. Under these conditions the sniffer was able to decrypt the entire traffic flow, demonstrating that operational mistakes can completely undermine SSL’s theoretical security guarantees.
From these findings, the authors draw several technical insights. The key exchange mechanism is the primary determinant of a session’s resilience: RSA‑based exchanges lack perfect forward secrecy (PFS), so compromise of the server’s private key endangers past sessions, whereas DH/ECDH and especially ECDHE provide PFS, rendering previously captured traffic useless even if long‑term keys are later exposed. The choice of record‑layer encryption also matters; AEAD modes combine confidentiality and integrity in a single operation, automatically aborting the session on authentication failure and preventing replay or modification attacks that older MAC‑then‑encrypt constructions are vulnerable to.
The paper concludes with concrete recommendations for practitioners. First, organizations should enforce TLS 1.3 as the minimum protocol version and disable all legacy versions. Second, server and client configurations must prioritize cipher suites that offer both PFS and AEAD (e.g., ECDHE‑RSA‑AES‑GCM, ECDHE‑ECDSA‑ChaCha20‑Poly1305). Third, robust certificate management policies are essential: only certificates signed by trusted CAs should be accepted, and automatic revocation checking (OCSP/CRL) should be enabled. Fourth, regular vulnerability scanning and log analysis should be employed to detect anomalous handshake attempts or downgrade attempts. Finally, software libraries must be kept up‑to‑date, and any custom SSL/TLS implementations should be avoided in favor of well‑maintained, open‑source stacks such as OpenSSL 3.x or LibreSSL.
Overall, the study confirms that modern SSL/TLS, when correctly configured, provides strong protection against passive sniffing and even many active attacks. However, the security guarantees are fragile in the presence of outdated protocol support, weak cipher choices, or lax certificate validation. By adhering to the recommended best practices, network administrators can ensure that the data traversing their infrastructures remains confidential and tamper‑proof, effectively neutralizing the primary threat posed by packet sniffers.
Comments & Academic Discussion
Loading comments...
Leave a Comment