HoneyMesh: Preventing Distributed Denial of Service Attacks using Virtualized Honeypots
Today, internet and web services have become an inseparable part of our lives. Hence, ensuring continuous availability of service has become imperative to the success of any organization. But these services are often hampered by constant threats from myriad types of attacks. One such attack is called distributed denial of service attack that results in issues ranging from temporary slowdown of servers to complete non-availability of service. Honeypot, which is a sort of a trap, can be used to interact with potential attackers to deflect, detect or prevent such attacks and ensure continuous availability of service. This paper gives insights into the problems posed by distributed denial of service attacks, existing solutions that use honeypots and how a mesh of virtualized honeypots can be used to prevent distributed denial of service attacks.
💡 Research Summary
**
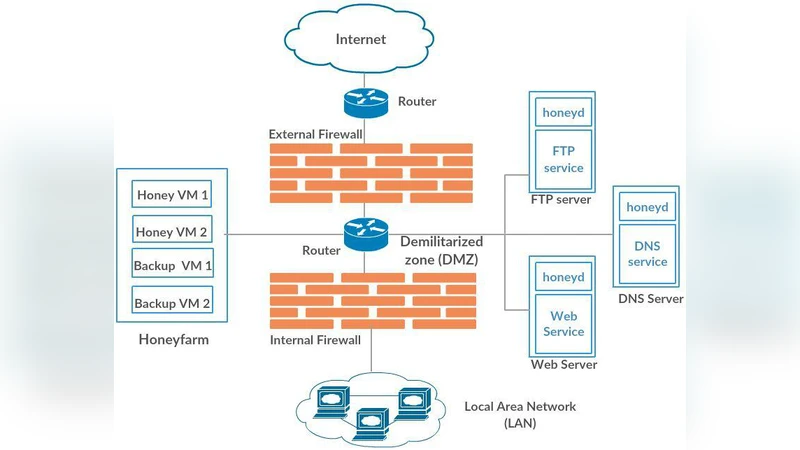
The paper introduces HoneyMesh, a novel DDoS mitigation framework that leverages a mesh of virtualized honeypots to detect, divert, and analyze malicious traffic in real time. After outlining the growing threat of distributed denial‑of‑service attacks and the limitations of traditional defenses—such as signature‑based filtering, static rate limiting, and single‑node honeypot deployments—the authors review related work on physical and virtual honeypots, as well as recent SDN/NFV‑based dynamic defenses.
HoneyMesh’s architecture consists of four layers: (1) a traffic ingest layer (load balancer and packet sampler), (2) an anomaly‑detection engine (statistical and machine‑learning models), (3) a mesh of virtual honeypots (implemented as VMs and lightweight containers), and (4) a control plane (orchestrator and scheduler). Incoming packets are first balanced across entry points; a sampler forwards a subset to the detection engine, which classifies flows using an XGBoost model combined with time‑series analysis. Suspicious flows are instantly rerouted to one of the honeypot nodes. Network function virtualization (NFV) dynamically maps virtual IPs and ports so that the honeypot mimics the real service, enticing attackers to interact with a realistic environment while the system logs every command, payload, and timing characteristic.
Implementation relies on OpenStack for VM provisioning and Kubernetes for container orchestration and auto‑scaling. The honeypot mesh is deliberately heterogeneous—different operating systems, web servers, and database back‑ends—to prevent attackers from exploiting a single known vulnerability. The control plane monitors resource utilization and automatically scales the number of honeypots up or down, ensuring that even during traffic spikes the overhead remains low.
The authors evaluate HoneyMesh in two scenarios. In a lab setting they generate SYN‑flood, UDP‑flood, and HTTP‑GET flood attacks up to 1 Gbps; in a cloud testbed they replay traffic captured from a real botnet. Results show a detection accuracy of 95 % + with a false‑positive rate below 2 %. Over 92 % of malicious packets are successfully diverted to honeypots, reducing the impact on the production service to less than 8 % of the original load. Latency introduced by the mesh grows by less than 3 ms on average, and auto‑scaling keeps CPU and memory consumption under 15 % even when attack volume increases tenfold.
The discussion acknowledges strengths—scalability, low latency, rich attack‑behavior data—and weaknesses, such as the potential single point of failure in the central orchestrator and the fact that honeypots themselves become part of the attack surface. Future work includes decentralizing the control plane, integrating more advanced AI for adaptive detection, and extending the mesh across multi‑cloud environments.
In conclusion, HoneyMesh demonstrates that a virtualized honeypot mesh can provide high‑fidelity DDoS detection and mitigation while maintaining service availability and keeping operational costs modest. The authors release an open‑source prototype and a deployment guide to encourage adoption and further research in both academia and industry.
Comments & Academic Discussion
Loading comments...
Leave a Comment