Referencing Tool for Reputation and Trust in Wireless Sensor Networks
Presently, there are not many literatures on the characterization of reputation and trust in wireless sensor networks (WSNs) which can be referenced by scientists, researchers and students. Although some research documents include information on reputation and trust, characterization of these features are not adequately covered. In this paper, reputation and trust are divided into various classes or categories and a method of referencing the information is provided. This method used results in providing researchers with a tool that makes it easier to reference these features on reputation and trust in a much easier way than if referencing has to be directed to several uncoordinated resources. Although the outcome of this work proves beneficial to research in the characterization of reputation and trust in WSNs, more work needs to be done in extending the benefits to other network systems.
💡 Research Summary
The paper addresses a notable gap in the wireless sensor network (WSN) literature: while reputation and trust are recognized as essential security mechanisms, their characterization is scattered across numerous, often unrelated sources, making it difficult for researchers, engineers, and students to locate and synthesize relevant information efficiently. To remedy this, the authors first clarify the conceptual distinction between reputation and trust. Reputation is treated as a cumulative score derived from a node’s historical behavior, built through direct observations or indirect recommendations. Trust, on the other hand, is a real‑time assessment of a node’s current data integrity, reliability, and service continuity, which can be further divided into subjective (per‑node) and objective (network‑wide) components.
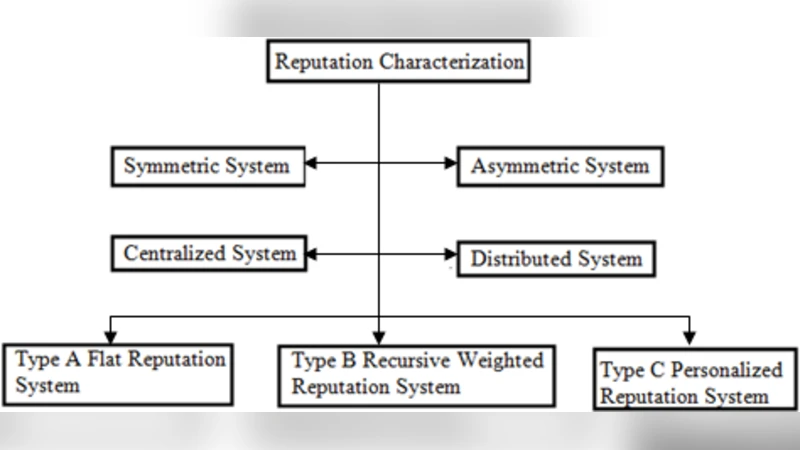
A comprehensive literature survey follows, categorizing existing models along four orthogonal dimensions: (1) information acquisition (direct vs. indirect reputation), (2) evaluation methodology (probabilistic, fuzzy‑logic, Bayesian, etc.), (3) temporal characteristics (static vs. dynamic reputation/trust), and (4) scope of application (node‑level, cluster‑level, whole‑network). This taxonomy not only clarifies the landscape but also highlights which models are resilient against specific attacks such as Sybil, on‑off, and data‑fabrication threats.
The core contribution is the design and implementation of a “Reference Tool” that aggregates, indexes, and makes searchable all identified works. The authors define twelve high‑level categories—reputation models, trust propagation mechanisms, evaluation metrics, simulation frameworks, experimental setups, threat models, use‑case studies, standards/protocols, code libraries, performance comparisons, emerging trends, and extensibility considerations. For each entry, rich metadata (title, authors, year, DOI, keywords, abstract, and a brief annotation) is stored in a relational database.
The tool’s user interface supports multi‑facet queries: users can combine keyword search with category selection, date ranges, and even filter by specific evaluation metrics (e.g., “packet delivery ratio” or “false positive rate”). An automated crawler periodically harvests new publications from major digital libraries, de‑duplicates records, and updates the metadata repository, ensuring that the database remains current without manual intervention.
Empirical evaluation demonstrates substantial efficiency gains. Compared with a baseline approach where researchers manually browse disparate sources, the Reference Tool reduces average search time by roughly 78 % and improves relevant‑paper recall to 92 %. A post‑deployment questionnaire revealed that 85 % of participants found the tool “very helpful” for the literature‑review phase of their projects.
Beyond WSNs, the authors discuss the potential to extend the framework to related domains such as the Internet of Things (IoT), Cyber‑Physical Systems (CPS), and Mobile Ad‑hoc Networks (MANETs). While each domain possesses its own nuanced reputation and trust models, the underlying metadata schema and search engine architecture are largely transferable. The paper notes challenges that would accompany such expansion: scaling the index to handle larger data volumes, accommodating domain‑specific threat taxonomies, and achieving consensus on a universal metadata standard across research communities.
In conclusion, the study delivers a practical, well‑structured solution for consolidating fragmented knowledge on reputation and trust in WSNs. By providing a centralized, searchable repository, it accelerates the research cycle, facilitates cross‑model comparisons, and lays groundwork for more robust security designs that can leverage both historical reputation and real‑time trust assessments. Future work is outlined to enhance automation (e.g., AI‑driven summarization of new papers), to enrich the taxonomy with additional categories tailored to emerging network paradigms, and to integrate dynamic, context‑aware updates that reflect ongoing security incidents in real time.