A Review of Technical Problems when Conducting an Investigation in Cloud Based Environments
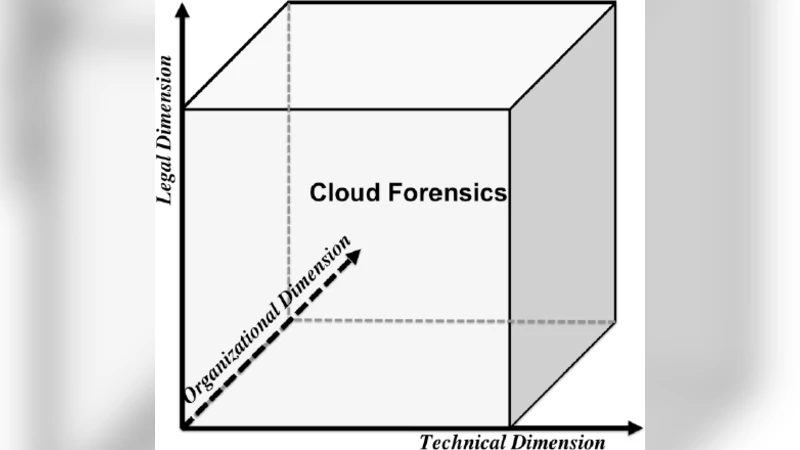
Cloud computing is a relatively new technology which is quickly becoming one of the most important technological advances for computer science. This technology has had a significant growth in recent years. It is now more affordable and cloud platforms are becoming more stable. Businesses are successfully migrating their systems to a cloud infrastructure, obtaining technological and economic benefits. However, others still remain reluctant to do it due to both security concerns and the loss of control over their infrastructures and data that the migration entails. At the same time that new technologies progress, its benefits appeal to criminals too. They can not only steal data from clouds, but they can also hide data in clouds, which has provoked an increased in the number of cybercrimes and their economic impacts. Their victims range from children and adults to companies and even countries. On the other hand, digital forensics have negatively suffered the impact of the boom of cloud computing due to its dynamic nature. The tools and procedures that were successfully proved and used in digital investigations are now becoming irrelevant, making it an urging necessity to develop new forensics capabilities for conducting an investigation in this new environment. As a consequence of these needs a new area has emerged, Cloud Forensics, which is the result of the intersection between cloud computing and digital forensics. Keywords: Cloud forensics, cloud computing, forensics investigation, forensic challenges.
💡 Research Summary
Cloud computing has rapidly moved from a novel concept to a cornerstone of modern IT infrastructure, offering organizations unprecedented scalability, cost efficiency, and flexibility. This widespread adoption, however, brings with it a dual‑edged sword: while businesses reap economic and technological benefits, the same characteristics that make clouds attractive also provide cyber‑criminals with new avenues for theft, data concealment, and large‑scale attacks. Consequently, the field of digital forensics, which traditionally relied on static, locally stored evidence, now faces a profound paradigm shift. The paper “A Review of Technical Problems when Conducting an Investigation in Cloud‑Based Environments” surveys the principal technical challenges that arise when attempting to perform forensic investigations within cloud environments and outlines the emerging discipline of cloud forensics.
1. Service‑Model Specific Constraints
The authors begin by dissecting the three primary cloud service models—Infrastructure as a Service (IaaS), Platform as a Service (PaaS), and Software as a Service (SaaS). In IaaS, investigators can obtain virtual‑machine snapshots and hypervisor logs, yet they lack direct physical‑disk access, making traditional imaging techniques obsolete. PaaS exposes application‑level logs and managed databases but hides the underlying operating system, limiting low‑level evidence such as memory dumps. SaaS provides only the highest‑level user interactions and service‑generated logs, often omitting any insight into the internal processing pipeline. Consequently, the level at which evidence can be collected is tightly coupled to the chosen service model, demanding model‑aware forensic strategies.
2. Dynamic Resource Allocation and Ephemeral Artifacts
Cloud platforms automatically scale resources, spin up or terminate instances, and migrate workloads across data centers. This elasticity dramatically increases evidence volatility. Memory contents, temporary logs, and in‑flight network packets can disappear the moment an instance is terminated or migrated. The paper stresses the necessity of real‑time capture mechanisms—API‑driven snapshot triggers, event‑based log streaming, and automated forensic agents that can be deployed instantly. Without such mechanisms, investigators risk losing critical artefacts before they can be preserved.
3. Legal and Jurisdictional Barriers
Data sovereignty and privacy regulations (e.g., GDPR, CCPA, and various national data‑localization laws) create a complex legal landscape for cross‑border investigations. Evidence stored in a multi‑regional cloud may be subject to multiple, sometimes conflicting, legal regimes. The authors argue that investigators must scrutinize Service Level Agreements (SLAs) and data‑retention policies before an incident occurs, and be prepared to obtain court orders or mutual legal assistance treaties (MLATs) to compel cloud providers to release data. Failure to respect jurisdictional constraints can render collected evidence inadmissible.
4. Heterogeneous Data Formats and Encryption
Cloud storage services employ a variety of data representations: object stores (e.g., Amazon S3), block devices (e.g., EBS), file systems, and streaming logs. Each format carries its own metadata schema and access API, complicating unified parsing and analysis. Moreover, server‑side encryption (SSE) and customer‑managed keys (CMKs) are now standard. Forensic practitioners must therefore negotiate key‑retrieval procedures with providers, or possess pre‑shared keys, to decrypt seized artefacts. The paper highlights the lack of standardized tools capable of handling this diversity, urging the development of modular parsers and decryption modules.
5. Inadequacy of Traditional Forensic Toolsets
Most commercial and open‑source forensic suites (e.g., EnCase, FTK, Autopsy) are designed for static disk imaging, memory acquisition, and network capture in on‑premises environments. They do not natively support cloud‑specific interfaces such as RESTful APIs, event‑driven notifications, or multi‑tenant isolation mechanisms. The authors review emerging cloud‑forensics frameworks—FROST, the Cloud Forensics Toolkit, and others—pointing out that these tools are still in early stages, lacking robust automation, integrity‑verification (hash chaining), and seamless integration with established forensic standards (ISO/IEC 27037, NIST SP 800‑101).
6. Proposed Research Directions
To bridge the identified gaps, the paper proposes several avenues for future work:
- Meta‑Forensic Architectures – Design unified models that can ingest evidence from multi‑cloud and hybrid environments, preserving provenance across disparate platforms.
- AI‑Assisted Log Mining – Apply machine‑learning techniques to sift through massive cloud logs, automatically flagging anomalous events that may correspond to malicious activity.
- Standardized Contractual Clauses – Develop template SLA clauses that obligate providers to retain forensic‑ready logs, support key escrow, and enable rapid evidence extraction under lawful request.
- Automation and Integrity Assurance – Build pipelines that automatically compute cryptographic hashes, generate chain‑of‑trust records, and package evidence in formats accepted by courts worldwide.
Conclusion
The paper concludes that cloud forensics is not merely an extension of traditional digital forensics but a distinct discipline requiring new methodologies, tools, and legal frameworks. The dynamic, distributed, and encrypted nature of cloud services erodes the effectiveness of legacy investigative techniques. Addressing these challenges demands a coordinated effort among researchers, cloud service providers, legal authorities, and organizations that rely on cloud infrastructure. Only through the development of cloud‑specific forensic capabilities, standardized procedures, and proactive contractual safeguards can investigators maintain the ability to collect, preserve, and present reliable evidence in the era of ubiquitous cloud computing.
Comments & Academic Discussion
Loading comments...
Leave a Comment