Android Tapjacking Vulnerability
Android is an open source mobile operating system that is developed mainly by Google. It is used on a significant portion of mobile devices worldwide. In this paper, I will be looking at an attack commonly known as tapjacking. I will be taking the attack apart and walking through each individual step required to implement the attack. I will then explore the various payload options available to an attacker. Lastly, I will touch on the feasibility of the attack as well as mitigation strategies.
💡 Research Summary
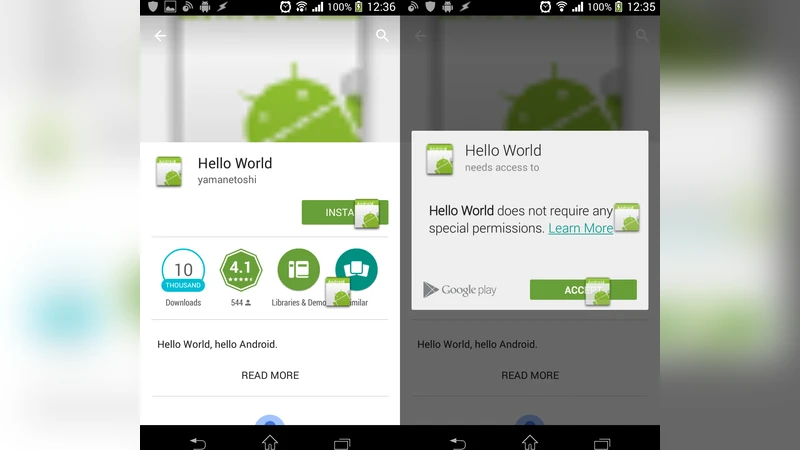
The paper provides a step‑by‑step dissection of the Android tap‑jacking vulnerability, a UI‑layer attack that tricks users into tapping invisible foreground elements while the actual touch events are delivered to a hidden background application. The author begins by selecting a payload; the primary example is an “installer” payload that silently installs a second malicious app via a market:// URL, automating the “Install” and “Accept” button presses in Google Play.
To implement the attack, a malicious app creates a transparent Toast activity that overlays the target UI. The Toast’s position is calibrated in density‑independent pixels (dp) so that the same coordinates work across devices with the same aspect ratio. Images are placed so they do not overlap visible UI elements, and the Toast is set to loop continuously with a white background to obscure the underlying app. The attacker may also add bait images to encourage repeated taps.
Beyond the installer payload, the paper explores URL‑based payloads (http(s):// and tel://) and intent‑based payloads that launch system settings or third‑party apps. URL payloads can trigger web‑view exploits or unwanted phone calls, while intent payloads can toggle Wi‑Fi/Bluetooth, enable installations from unknown sources, or launch specific applications. Each alternative requires additional knowledge of the target app’s package structure and UI layout, making them more complex.
The feasibility assessment rates the proof‑of‑concept as “high impact” but “low overall feasibility.” Successful exploitation demands Android development skills, precise UI measurements, and user cooperation to install the malicious app and follow on‑screen instructions. The attack is also limited to devices with a particular screen aspect ratio, reducing scalability.
Mitigation strategies include setting the declarative filterTouchesWhenObscured attribute to true or overriding onFilterTouchEventForSecurity to programmatically reject touches when the app is not in the foreground. The author notes that many developers have not adopted these measures, and even Google Play remains vulnerable on some devices. User‑level defenses consist of avoiding obscure third‑party apps, monitoring unexpected installations, and adhering to general security hygiene.
In conclusion, while tap‑jacking is technically feasible and can lead to severe privacy breaches—especially with the installer payload that grants permissions such as RECEIVE_BOOT_COMPLETED, INTERNET, and ACCESS_NETWORK_STATE—its practical deployment is hampered by high complexity and low scalability. The paper recommends that developers proactively apply the available Android security flags and that users maintain vigilant security practices to mitigate not only tap‑jacking but broader mobile threats.
Comments & Academic Discussion
Loading comments...
Leave a Comment