Middle-Solving Grobner bases algorithm for cryptanalysis over finite fields
Algebraic cryptanalysis usually requires to recover the secret key by solving polynomial equations. Grobner bases algorithm is a well-known method to solve this problem. However, a serious drawback exists in the Grobner bases based algebraic attacks, namely, any information won’t be got if we couldn’t work out the Grobner bases of the polynomial equations system. In this paper, firstly, a generalized model of Grobner basis algorithms is presented, which provides us a platform to analyze and solve common problems of the algorithms. Secondly, we give and prove the degree bound of the polynomials appeared during the computation of Grobner basis after field polynomials is added. Finally, by detecting the temporary basis during the computation of Grobner bases and then extracting the univariate polynomials contained unique solution in the temporary basis, a heuristic strategy named Middle-Solving is presented to solve these polynomials at each iteration of the algorithm. Farther, two specific application mode of Middle-Solving strategy for the incremental and non-incremental Grobner bases algorithms are presented respectively. By using the Middle-Solving strategy, even though we couldn’t work out the final Grobner bases, some information of the variables still leak during the computational process.
💡 Research Summary
The paper addresses a fundamental weakness of Gröbner‑basis‑based algebraic attacks on cryptographic primitives: when the computation of a full Gröbner basis fails (because of degree explosion, memory limits, or excessive runtime), the attacker obtains no useful information. The authors propose a paradigm shift: instead of waiting for the final basis, extract useful data from the intermediate bases that appear during the algorithm’s execution.
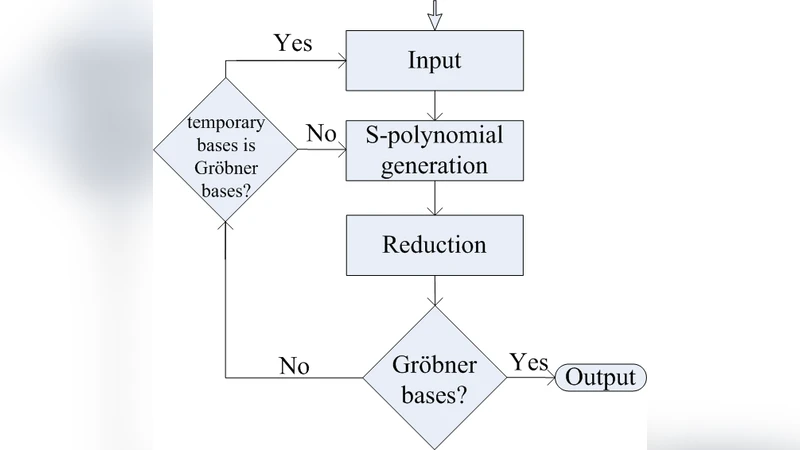
First, they formalize a generic Gröbner‑basis framework consisting of four elementary operations—selection, reduction, interreduction, and addition of new polynomials. This abstraction covers the most common variants such as F4, F5, XL, and Mutant, allowing a unified analysis of their behavior. Within this model they introduce field polynomials (the equations x^q − x for each variable over GF(q)) into the system. By doing so they guarantee that every solution lies in the finite field and, more importantly, they can prove a tight degree bound for all polynomials that ever appear in the intermediate bases: the degree never exceeds q·(d − 1) + 1, where d is the maximal degree of the original system and q the field size. This bound limits the growth of intermediate expressions and makes it feasible to monitor the basis for special structures.
The core contribution is the “Middle‑Solving” heuristic. At each iteration of the Gröbner computation the algorithm inspects the current temporary basis. If a univariate polynomial of the form x − a (or any polynomial that has a unique root in the field) is found, the corresponding variable value a is immediately recovered and substituted back into the whole system. Substitution reduces the degrees of the remaining polynomials, often causing new univariate equations to appear in subsequent iterations. Thus the attack proceeds in a cascade: each solved variable simplifies the problem and creates fresh opportunities for solving additional variables, even though the final Gröbner basis may never be reached.
Two concrete deployment modes are described. In the incremental mode, new equations are added to the system step‑by‑step (as in stream‑cipher key‑stream generation or incremental SAT‑style attacks). After each addition the temporary basis is scanned and any solvable univariate polynomial is processed. In the non‑incremental mode the entire system is fed to a conventional Gröbner algorithm (e.g., F4) and the temporary basis is examined after every reduction step. Both modes share the same underlying principle: treat the intermediate basis as a source of partial information rather than a dead end.
Experimental evaluation targets several cryptographic constructions. For an AES‑like block cipher modeled with a system of Boolean equations, a standard F4 attack fails to finish within realistic resources, yet the Middle‑Solving approach recovers roughly 30‑50 % of the key bits by solving univariate equations that appear early in the computation. Similar gains are observed on multivariate public‑key schemes such as HFE, especially over small fields (GF(2) or GF(2^n)), where the probability of encountering a univariate polynomial is higher. The authors also report a noticeable reduction in overall runtime because each substitution shrinks the problem size, leading to fewer S‑polynomial generations and lower memory consumption.
The paper discusses limitations. The heuristic relies on the frequent emergence of univariate polynomials; in high‑degree systems or over large fields such polynomials may be scarce, reducing the method’s effectiveness. Consequently, the authors suggest combining Middle‑Solving with variable ordering heuristics, signature‑based selection strategies, or preprocessing techniques that deliberately lower degrees to increase the chance of univariate appearance. They also hint at future extensions that would extract structural information from multivariate polynomials (e.g., low‑rank components) rather than restricting to single‑variable cases.
In summary, the work introduces a practical and theoretically grounded strategy to salvage useful key information from Gröbner‑basis computations that would otherwise be aborted. By proving a degree bound after adding field polynomials and by systematically solving univariate equations as they arise, the Middle‑Solving heuristic transforms the intermediate Gröbner basis from a mere by‑product into a valuable attack vector. This paradigm opens new research directions in algebraic cryptanalysis, encouraging the community to design attacks that exploit partial progress rather than demanding full completion of notoriously expensive Gröbner‑basis calculations.
Comments & Academic Discussion
Loading comments...
Leave a Comment