Reverse Engineering of RFID devices
This paper discusses the relevance and potential impact of both RFID and reverse engineering of RFID technology, followed by a discussion of common protocols and internals of RFID technology. The focus of the paper is on providing an overview of the different approaches to reverse engineering RFID technology and possible countermeasures that could limit the potential of such reverse engineering attempts.
💡 Research Summary
The paper provides a comprehensive overview of reverse engineering (RE) techniques applied to Radio‑Frequency Identification (RFID) devices, with a particular focus on 13.56 MHz smart‑card implementations that follow the ISO/IEC 14443 standard. It begins by defining RE and outlining four principal motivations: espionage and cloning, analysis of legacy or poorly documented products, circumvention of copyright through clean‑room design, and verification of security claims. These motivations set the stage for why adversaries—whether nation‑states, corporations, or security researchers—invest effort into dissecting RFID systems.
The technical background explains that a passive RFID tag harvests energy from the alternating electromagnetic field generated by an active reader. The tag’s antenna both receives modulated commands and reflects a back‑scatter signal whose strength depends on the tag’s instantaneous power consumption. This physical coupling makes side‑channel attacks based on power and electromagnetic (EM) emissions particularly relevant.
The core of the paper categorises RE approaches into non‑intrusive and intrusive methods.
Non‑intrusive methods
- Protocol analysis – Capturing and decoding the communication between reader and tag. This requires minimal hardware, is inexpensive, and can reveal command structures, authentication flows, and data formats. While it rarely discloses secret keys directly, it provides a blueprint of the tag’s functional behavior, which can guide further attacks.
- Power/EM analysis – Measuring variations in the back‑scatter field to infer the tag’s internal power consumption. The authors cite Oren and Shamir’s work showing that a tag’s response to a “kill” command differs in power draw depending on whether the last bit of a password is checked, allowing an attacker to distinguish between different internal states. Subsequent research (e.g., Hutter et al.) demonstrates differential power analysis capable of extracting AES keys from 13.56 MHz cards. Because the tag’s power source is the reader’s field, power and EM side‑channels are inseparable in passive RFID.
Intrusive methods
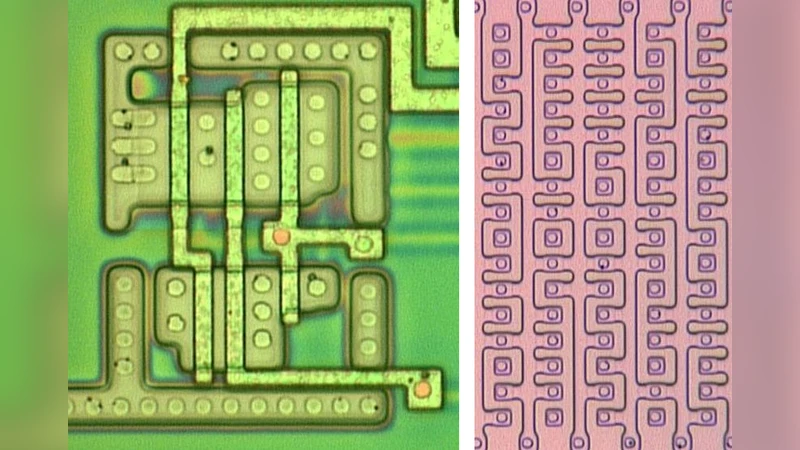
- Optical analysis – Physical removal of the chip package (chemical etching, polishing, or focused ion beam) followed by imaging with optical microscopes, scanning electron microscopes (SEM), transmission electron microscopes (TEM), or scanning capacitance microscopes. The paper details how Karsten Nohl’s team used a standard 500× optical microscope, combined with panoramic stitching, to reconstruct the layout of a MIFARE Classic chip, locate a 56‑bit key register, and identify a flawed random‑number generator. Limitations of optical microscopy (≈200 nm resolution) are noted, but many RFID tags are fabricated with older lithography nodes where this resolution suffices.
- Electronic analysis – Attaching micro‑probes to exposed silicon to monitor internal signals during operation. For multi‑layer modern chips, focused ion beam (FIB) drilling creates access holes, enabling probing of otherwise hidden nets. Techniques such as voltage glitching, clock manipulation, and intentional circuit damage are discussed as ways to bypass built‑in tamper‑resistance and extract secret data.
The paper then surveys counter‑measures. Physical defenses include hardened packaging, anti‑reverse‑engineering coatings, and power‑balancing circuitry that equalises consumption regardless of processed data, thereby blunting power‑analysis attacks. Logical defenses involve randomising timing, inserting dummy operations, and designing cryptographic modules that exhibit constant‑time, constant‑power behavior. The authors argue that while such measures raise the cost and complexity of RE, they are not fool‑proof.
Finally, the authors advocate for transparency and open‑source design, asserting that publicly vetted implementations accelerate vulnerability discovery and remediation, ultimately improving ecosystem security. Nonetheless, they acknowledge that in commercial contexts, “security through obscurity” remains a pragmatic, albeit imperfect, strategy.
In summary, the paper maps the full landscape of RFID reverse engineering—from low‑cost protocol sniffing to high‑end electron microscopy—highlights the trade‑offs between attack complexity, required resources, and potential payoff, and outlines both technical and policy‑level defenses that stakeholders can adopt to mitigate the identified risks.
Comments & Academic Discussion
Loading comments...
Leave a Comment