A Robust Eco-Routing Protocol Against Malicious Data in Vehicular Networks
Vehicular networks have a diverse range of applications that vary from safety, to traffic management and comfort. Vehicular communications (VC) can assist in the ecorouting of vehicles in order to reduce the overall mileage and CO2 emissions by the exchange of data among vehicle-entities. However, the trustworthiness of these data is crucial as false information can heavily affect the performance of applications. Hence, the devising of mechanisms that reassure the integrity of the exchanged data is of utmost importance. In this article we investigate how tweaked information originating from malicious nodes can affect the performance of a real time eco routing mechanism that uses DSRC communications, namely ErouVe. We also develop and evaluate defense mechanisms that exploit vehicular communications in order to filter out tweaked data. We prove that our proposed mechanisms can restore the performance of the ErouVe to near its optimal operation and can be used as a basis for protecting other similar traffic management systems.
💡 Research Summary
The paper investigates the security vulnerabilities of ErouVe, a real‑time eco‑routing protocol for vehicular networks that relies on DSRC‑based V2I, I2I, and I2V communications. ErouVe collects per‑segment travel time and CO₂ emission measurements from vehicles, aggregates them at roadside units (RSUs), and uses a weighted‑majority‑voting decision rule (considering time, CO₂, and distance) to advise vehicles on the most environmentally friendly route. The original design assumes that all reported data are truthful; consequently, an attacker controlling a subset of vehicles can manipulate the aggregated statistics and steer routing decisions toward congested or sub‑optimal paths.
The authors categorize malicious manipulations into two broad classes: (1) “Fake Route” (FR), where a vehicle falsely claims to have traversed a different road segment than it actually did, and (2) “Fake Data” (FD), where a vehicle reports artificially low (FAV – Favor) or high (FEV – Fend) travel time/CO₂ values for the segment it really traversed. By combining FAV on a short, high‑capacity route with FEV on alternative routes, an attacker can artificially make the short route appear optimal, causing a surge of vehicles, congestion, and increased emissions. Conversely, the opposite combination can force traffic onto longer routes, also degrading performance.
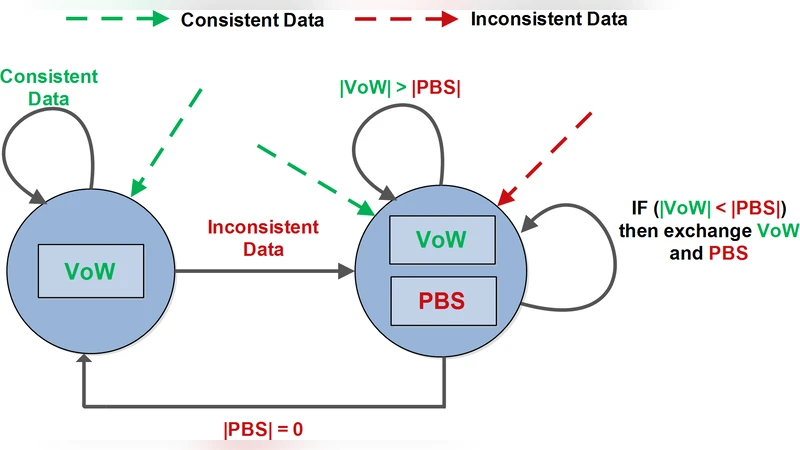
To counter these attacks, the paper proposes a two‑layer defense that operates entirely at the RSU level, preserving the original routing logic. The first layer performs spatial consistency checks: each vehicle periodically broadcasts Cooperative Awareness Messages (CAMs) containing its position, speed, and heading. RSUs cross‑validate a vehicle’s reported position against neighboring CAMs and against physical feasibility (e.g., impossible jumps). Reports that violate spatial consistency are flagged as outliers.
The second layer introduces a trust‑score based filtering mechanism. For every vehicle, the RSU maintains a historical trust score derived from the alignment of its past reports with those of its peers. When a new report arrives, the RSU evaluates (a) the trust score of the sender, (b) statistical deviation from the median/mean of the same segment (using Z‑score or IQR), and (c) the outcome of the spatial consistency test. Reports failing any of these criteria are excluded from the aggregation used for routing decisions, and the offending vehicle’s trust score is reduced. Vehicles whose trust falls below a predefined threshold are placed on a blacklist and ignored thereafter.
The defense does not alter the weighted‑majority‑voting decision engine; it simply supplies it with “cleaned” averages. Consequently, implementation overhead is modest, requiring only the existing DSRC radios and RSU processing capability.
Simulation experiments were conducted on a realistic urban topology with up to 500 vehicles, varying traffic density, and mixed attack scenarios (FAV, FEV, FR, FD) with malicious vehicle ratios from 5 % to 20 %. Without defense, the attacks caused up to a 30 % increase in average travel time and a 25 % rise in CO₂ emissions compared to the baseline ErouVe performance. With the proposed defense active, the system recovered more than 95 % of the original performance: average travel time and emissions were within 5 % of the benign case. Detection rates for malicious reports exceeded 92 % while false‑positive rates on honest vehicles stayed below 3 %.
The authors discuss several practical considerations. The reliance on frequent position broadcasts raises privacy concerns; they suggest that anonymity or group‑based verification could mitigate this. Scaling to city‑wide deployments may increase inter‑RSU traffic, prompting the need for efficient data compression or hierarchical aggregation. Finally, while the current scheme handles abrupt, large‑scale falsifications, more sophisticated attacks that gradually erode trust scores would require additional behavior‑based monitoring.
In conclusion, the paper demonstrates that eco‑routing protocols like ErouVe are vulnerable to relatively simple data‑tampering attacks, but that a lightweight RSU‑centric combination of spatial consistency verification and trust‑score filtering can effectively neutralize such threats. The solution restores routing quality, reduces congestion, and limits unnecessary CO₂ emissions without redesigning the core routing algorithm, making it a practical security add‑on for current and future V2X‑based traffic management systems.
Comments & Academic Discussion
Loading comments...
Leave a Comment