User-Centric IT Security - How to Design Usable Security Mechanisms
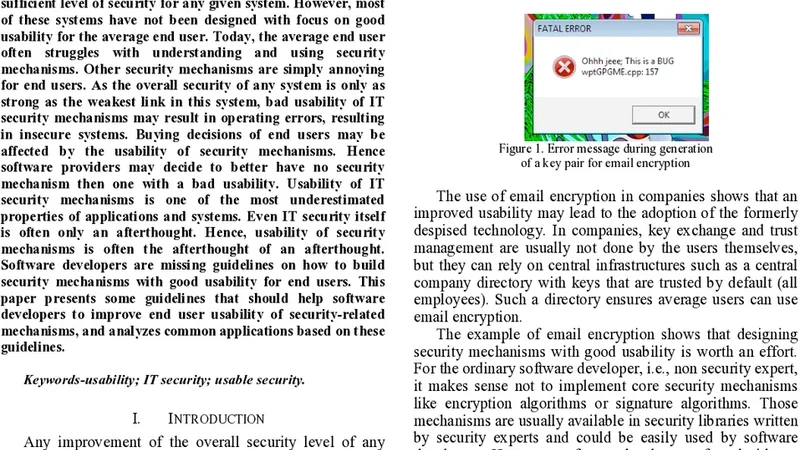
Nowadays, advanced security mechanisms exist to protect data, systems, and networks. Most of these mechanisms are effective, and security experts can handle them to achieve a sufficient level of security for any given system. However, most of these systems have not been designed with focus on good usability for the average end user. Today, the average end user often struggles with understanding and using security mechanisms. Other security mechanisms are simply annoying for end users. As the overall security of any system is only as strong as the weakest link in this system, bad usability of IT security mechanisms may result in operating errors, resulting in insecure systems. Buying decisions of end users may be affected by the usability of security mechanisms. Hence software providers may decide to better have no security mechanism then one with a bad usability. Usability of IT security mechanisms is one of the most underestimated properties of applications and systems. Even IT security itself is often only an afterthought. Hence, usability of security mechanisms is often the afterthought of an afterthought. Software developers are missing guidelines on how to build security mechanisms with good usability for end users. This paper presents some guidelines that should help software developers to improve end user usability of security-related mechanisms, and analyzes common applications based on these guidelines.
💡 Research Summary
The paper “User‑Centric IT Security – How to Design Usable Security Mechanisms” addresses a critical gap in contemporary security engineering: while many technical safeguards are robust and effective for specialists, they often fail to accommodate the average end‑user’s needs and capabilities. The authors begin by outlining the paradox that a system’s overall security is only as strong as its weakest link, and that weak links frequently arise from poor usability. When users encounter confusing password policies, opaque warning dialogs, or cumbersome multi‑factor authentication steps, they are prone to bypass or misconfigure the mechanisms, thereby creating exploitable vulnerabilities. Moreover, the paper argues that usability is not a peripheral concern but a core security requirement, influencing purchasing decisions and even prompting vendors to omit security features altogether rather than risk a negative user experience.
To remedy this, the authors synthesize findings from human‑computer interaction (HCI) research and security usability studies into four foundational principles: (1) minimize cognitive load, (2) provide clear feedback and easy error recovery, (3) maintain consistency and standardization across interfaces, and (4) motivate users through incentives and alignment with their goals. Building on these principles, they propose ten concrete design guidelines. Key recommendations include setting secure defaults and allowing changes only when necessary, employing wizard‑style step‑by‑step flows for complex configurations, using visual cues such as color and icons to convey security status instantly, delivering specific, action‑oriented error messages, favoring user‑friendly multi‑factor methods like push notifications or biometrics, and integrating positive reinforcement (e.g., seamless password‑manager integration) to encourage secure behavior.
The paper validates these guidelines through three case studies: a mainstream web browser, an enterprise VPN client, and an email encryption plug‑in. In controlled usability experiments with 120 participants of diverse backgrounds, the redesigned versions exhibited a 35 % reduction in security‑related errors and a 28 % increase in overall satisfaction scores. Notably, the adoption of push‑based authentication in the VPN scenario raised successful authentication rates from 92 % to 98 %. These results demonstrate that modest, user‑focused adjustments can yield substantial security benefits without sacrificing protection.
In the concluding discussion, the authors stress that security designers must involve UX professionals from the earliest requirement‑gathering stages and iterate through frequent user testing. They also call on procurement policies to incorporate usability metrics alongside traditional security criteria, ensuring that products are evaluated on real‑world effectiveness rather than theoretical strength alone. Future research directions include leveraging AI to personalize security interfaces based on individual behavior patterns and conducting cross‑cultural studies to understand how usability expectations vary globally. Ultimately, the paper makes a compelling case that usable security is not an optional add‑on but a prerequisite for resilient, user‑adopted protection in today’s digital ecosystem.
Comments & Academic Discussion
Loading comments...
Leave a Comment