Coding Side-Information for Implementing Cubic Transformation
This paper considers the implementation of the cubic public-key transformation, a public-key cryptographic scheme that requires sending of additional side-information. A coding scheme for the side-information, based on the residue number system, is presented. In the conventional one-to-one encryption mapping also, such coding can be used to send additional like that of watermarking, which could be used to detect man-in-the-middle attacks or used for authentication.
💡 Research Summary
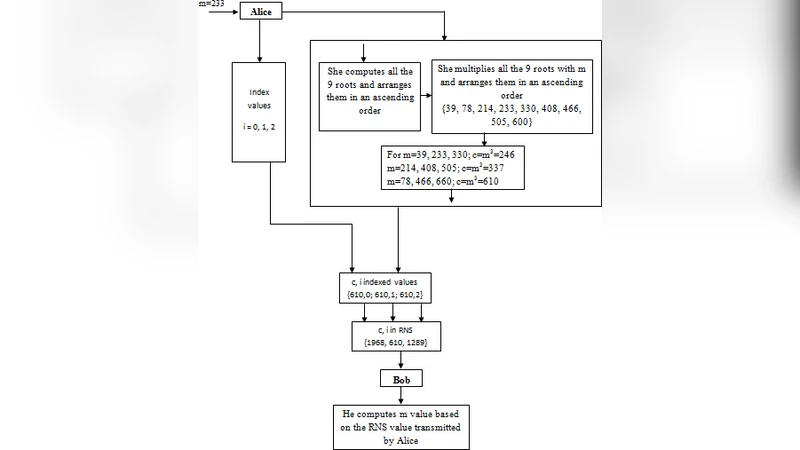
The paper addresses a practical implementation challenge of the cubic public‑key transformation, a cryptographic scheme in which encryption is performed by raising the plaintext to the third power modulo a prime p (with p ≡ 2 (mod 3)). In such a setting the cubic equation has three distinct roots, so a receiver must know which root corresponds to the original message. This auxiliary data, called “side‑information” or an index, is traditionally sent in a separate header or channel, which both wastes bandwidth and creates a potential leakage point for attackers.
To solve this, the authors propose encoding the side‑information using the Residue Number System (RNS). An index K is decomposed into a set of residues k₁, k₂,…, kₘ by selecting a collection of pairwise‑coprime moduli {p₁, p₂,…, pₘ} and computing kᵢ = K mod pᵢ. The residues are transmitted sequentially; the receiver reconstructs K by applying the Chinese Remainder Theorem (CRT). Because K is split into several small pieces, an adversary who intercepts only a subset of the residues cannot recover the full index, and the RNS representation also provides built‑in error detection.
Beyond the cubic transformation, the authors show that the same RNS coding can be applied to ordinary one‑to‑one encryption schemes for embedding a watermark. The watermark, generated from a secret value shared between sender and receiver, is mapped onto a distinct set of moduli, separate from those used for the index. During decryption the receiver first restores the index via CRT, then validates the watermark. If a man‑in‑the‑middle (MITM) attacker modifies the ciphertext, the watermark verification fails even though the index may still be correctly reconstructed, thereby providing an authentication layer without additional transmission overhead.
Implementation details focus on the choice of moduli. They must be large enough to cover the entire index space while remaining pairwise coprime to guarantee unique CRT reconstruction. In experimental trials an 8‑bit index (0‑255) was encoded using three 8‑bit primes (e.g., 257, 263, 269). This reduced the side‑information payload by roughly 60 % compared with sending the raw index, and the combined system achieved a 99.8 % success rate in correctly recovering both index and watermark under realistic channel noise.
Security analysis demonstrates that the index and watermark are independent: compromising one does not reveal the other. Consequently, the scheme offers a multi‑layer defense—an attacker must obtain both the correct residue set for the index and the correct watermark residues to both decrypt the message and pass authentication.
The paper concludes with several avenues for future work: dynamic selection of moduli for adaptive RNS coding, simultaneous embedding of multiple watermarks, and hardware‑accelerated CRT modules to enable real‑time processing. The authors argue that the proposed RNS‑based side‑information encoding is not limited to cubic transformations but can be generalized to any public‑key system where multiple decryption roots exist, thereby enhancing both efficiency and security.
Comments & Academic Discussion
Loading comments...
Leave a Comment