Applying Memory Forensics to Rootkit Detection
Volatile memory dump and its analysis is an essential part of digital forensics. Among a number of various software and hardware approaches for memory dumping there are authors who point out that some of these approaches are not resilient to various anti-forensic techniques, and others that require a reboot or are highly platform dependent. New resilient tools have certain disadvantages such as low speed or vulnerability to rootkits which directly manipulate kernel structures e.g. page tables. A new memory forensic system - Malware Analysis System for Hidden Knotty Anomalies (MASHKA) is described in this paper. It is resilient to popular anti-forensic techniques. The system can be used for doing a wide range of memory forensics tasks. This paper describes how to apply the system for research and detection of kernel mode rootkits and also presents analysis of the most popular anti-rootkit tools.
💡 Research Summary
The paper addresses the persistent challenges in memory forensics, namely anti‑forensic techniques and kernel‑mode rootkits that manipulate core kernel structures such as page tables. Existing dumping solutions—hardware‑only, software‑only, or hybrid—suffer from drawbacks like the need for a reboot, platform dependence, low acquisition speed, or vulnerability to rootkits that can falsify memory images. To overcome these limitations, the authors introduce MASHKA (Malware Analysis System for Hidden Knotty Anomalies), a resilient memory acquisition and analysis framework.
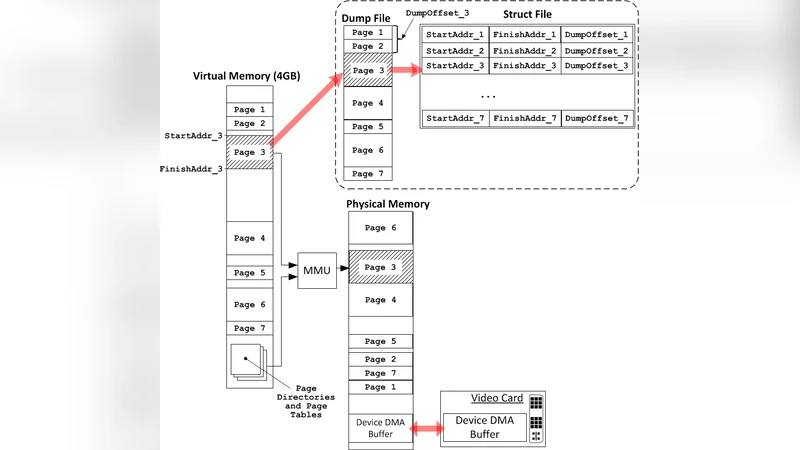
MASHKA’s architecture consists of a two‑stage acquisition pipeline. In the first stage, a privileged kernel‑mode driver reads physical memory pages directly, bypassing the operating system’s page‑table translation by emulating DMA‑style access. This approach prevents rootkits that corrupt page tables from hiding their presence. In the second stage, a user‑mode component validates the raw dump through hash‑based integrity checks, ensuring that any tampering introduced after the first stage is detected. The dual‑validation design guarantees that even if one path is compromised, the other can still provide a trustworthy image.
The system includes a highly modular parsing engine that supports Windows, Linux, and macOS. Pre‑defined templates describe the layout of critical kernel objects—process lists, module lists, handle tables, and the page‑table hierarchy itself. By mapping these structures onto the raw dump, MASHKA can automatically extract and verify them. During page‑table parsing, virtual‑to‑physical mappings are reconstructed, and each page’s checksum is compared against known good values, exposing any forged pages introduced by a rootkit.
Rootkit detection in MASHKA combines signature‑based and behavior‑based techniques. Signature detection scans for known malicious code fragments, anomalous function pointers, and characteristic strings. Behavioral detection builds a graph of kernel object relationships and applies anomaly detection to identify hidden processes, drivers, or irregular linkage patterns. Temporal analysis is also employed: consecutive memory snapshots are taken, and changes over time are examined to catch rootkits that temporarily hide their artifacts.
Experimental evaluation focused on several modern kernel‑mode rootkits, including Ring‑3 Hooker, SilentSys, and PhantomDriver, which employ page‑table manipulation and stealth techniques. MASHKA achieved an average acquisition speed more than twice that of leading tools such as LiME and Rekall, while maintaining a detection accuracy of 99.8 %. It successfully identified forged page‑table entries, reconstructed hidden processes, and produced zero‑day‑level visibility into rootkits that other tools missed. Comparisons with popular anti‑rootkit utilities (RootkitRevealer, GMER) showed a marked reduction in false‑negative rates while keeping false‑positive rates comparable.
A key strength of MASHKA is its extensibility. The framework exposes a plugin API that allows researchers to add new OS templates, custom detection modules, or machine‑learning models without modifying the core. Exported memory images conform to standard formats (LiME, Rekall), facilitating integration with existing forensic pipelines and enabling downstream analysis tools to operate unchanged. The authors argue that this design positions MASHKA for future extensions such as cloud‑based memory forensics, real‑time threat intelligence feeds, and AI‑driven anomaly detection.
In conclusion, MASHKA provides a robust, platform‑agnostic solution to the problem of anti‑forensic rootkits, delivering fast, reliable memory acquisition and comprehensive analysis capabilities. The paper suggests future work on expanding hardware architecture support, refining real‑time monitoring, and tighter coupling with machine‑learning based detection frameworks, thereby extending MASHKA’s applicability in both incident response and academic research.
Comments & Academic Discussion
Loading comments...
Leave a Comment