Ciberseguridad Inteligente
The Internet Economy has a strong dependency on cyberspace. This raises security risk scenarios due to the increasing number of vulnerabilities and the increased frequency and sophistication of cyber attacks, especially with the advent of advanced threats of APT type. This paper presents a model of Intelligent Cybersecurity (ICS) for detect, deny, disrupt, degrade, deceive and destroy enemy capabilities in cyberspace. This is achieved through the conceptual and technical development of a Capacity for Cyber Intelligence (CCI) which aims to interfere destructively C2 capabilities of the adversary, penetrating its decision loops with the speed necessary to displace him to a reactive posture. Finally, unlike the security models raised classically, the concept of ICSI suggests that the advantage in the conflict can be obtained by defense and not always by the attacker. As theoretical support, the “Offensive System Reference Model” (OSRM) is presented, which is used to think cyber conflict at all levels, from a perspective coordinated and synchronized with the rest of the traditional forces under the present set; and a justification of the capacity from the modern perspective C2.
💡 Research Summary
The paper addresses the growing dependence of the modern Internet economy on cyberspace and the consequent rise in security risks, especially from advanced persistent threats (APTs). It proposes an “Intelligent Cybersecurity” (ICS) framework that shifts the traditional defensive paradigm by integrating offensive capabilities, aiming to detect, deny, disrupt, degrade, deceive, and ultimately destroy adversary capabilities in cyberspace.
At the core of the framework is a “Cyber‑Intelligence Capability” (CCI). CCI is defined as an organizational asset that transforms raw data from diverse sources into actionable intelligence through a systematic process of indicator and precursor identification, traceability, and validation. By continuously feeding validated intelligence to decision‑makers, CCI enables rapid penetration of an adversary’s decision loop, forcing the opponent into a reactive posture and achieving a “speed advantage.”
To operationalize CCI, the authors introduce the “Offensive System Reference Model” (MSOR), a four‑phase process that mirrors the classic military OODA (Observe‑Orient‑Decide‑Act) cycle but is tailored for cyber conflict. The phases are:
- Conflict Emergence (PSC) – assesses internal and geopolitical conditions, conducts risk management, and develops supporting services and legal frameworks.
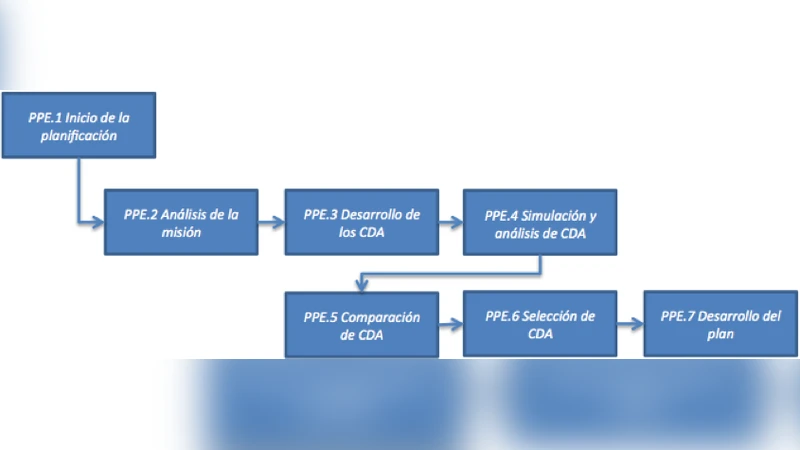
- Strategic Planning (PPE) – formulates national‑level cyber strategies, aligns them with existing legislation, and defines objectives across strategic, operational, and tactical levels.
- Operations Execution (POC) – implements offensive, defensive (both passive and active), and intelligence operations. Active cyber defense is emphasized, allowing immediate counter‑measures, deception, and kinetic‑like effects against adversary infrastructure.
- Result Evaluation (PER) – measures outcomes, extracts lessons learned, and feeds back into the CCI loop for continuous improvement.
The paper categorizes threat actors (nation‑states, trans‑national organized groups, small groups/individuals, and insider threats) and highlights the critical role of the private sector, whose assets often constitute the backbone of national critical infrastructure. It argues that coordinated public‑private collaboration, underpinned by CCI, is essential for effective risk mitigation.
A notable contribution is the formalization of “Active Cyber Defense” and “Cyber Deception” as integral components of the defensive posture. Rather than relying solely on passive controls (firewalls, IDS/IPS), the model advocates for proactive measures that can disrupt, degrade, or destroy adversary capabilities in real time, thereby shifting the initiative to the defender.
The authors also discuss Command and Control (C2) in the cyber domain, emphasizing that accurate, timely information enhances decision‑making quality. Target selection processes are presented as a means to prioritize objectives based on mission goals, resources, and potential collateral effects, acknowledging the political and legal complexities inherent in cyber operations.
While the conceptual model is comprehensive, the paper acknowledges several practical challenges: the lack of detailed technical specifications for implementing MSOR, the legal and normative ambiguities surrounding offensive cyber actions, and the high skill and resource requirements for building a robust CCI, which may be prohibitive for smaller organizations or developing nations.
In conclusion, the study offers a strategic, operational, and tactical blueprint that integrates intelligence, offense, and defense to give defenders the upper hand in cyber conflict. It pushes the discourse beyond the conventional view that attackers inherently hold the advantage, proposing that with a well‑structured CCI and the MSOR framework, defenders can achieve decisive superiority. Future work should focus on concrete implementation pathways, cost‑benefit analyses, and the development of international legal frameworks that accommodate active defensive measures.
Comments & Academic Discussion
Loading comments...
Leave a Comment