Network investigation methodology for BitTorrent Sync: A Peer-to-Peer based file synchronisation service
High availability is no longer just a business continuity concern. Users are increasingly dependant on devices that consume and produce data in ever increasing volumes. A popular solution is to have a central repository which each device accesses after centrally managed authentication. This model of use is facilitated by cloud based file synchronisation services such as Dropbox, OneDrive, Google Drive and Apple iCloud. Cloud architecture allows the provisioning of storage space with “always-on” access. Recent concerns over unauthorised access to third party systems and large scale exposure of private data have made an alternative solution desirable. These events have caused users to assess their own security practices and the level of trust placed in third party storage services. One option is BitTorrent Sync, a cloudless synchronisation utility provides data availability and redundancy. This utility replicates files stored in shares to remote peers with access controlled by keys and permissions. While lacking the economies brought about by scale, complete control over data access has made this a popular solution. The ability to replicate data without oversight introduces risk of abuse by users as well as difficulties for forensic investigators. This paper suggests a methodology for investigation and analysis of the protocol to assist in the control of data flow across security perimeters.
💡 Research Summary
**
The paper “Network investigation methodology for BitTorrent Sync: A Peer‑to‑Peer based file synchronisation service” presents a comprehensive technical analysis of BitTorrent Sync (BTSync) and proposes a systematic methodology for investigators to detect, capture, and interpret BTSync network traffic. The authors begin by contrasting cloud‑based file‑synchronisation services (Dropbox, OneDrive, Google Drive, iCloud) with BTSync’s “cloud‑less” architecture, highlighting the growing demand for user‑controlled data availability and privacy. BTSync replicates whole files between peers using the BitTorrent protocol’s underlying mechanisms (trackers, Peer Exchange, Distributed Hash Table, Local Peer Discovery) but adapts them for secure folder‑level replication rather than mass distribution.
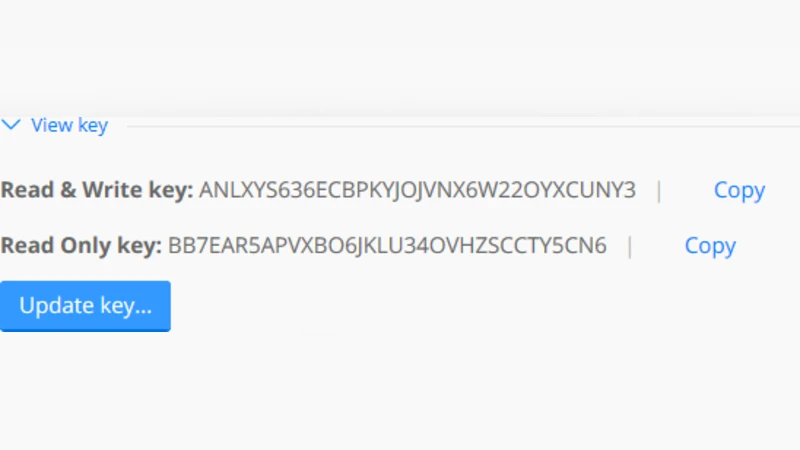
Key technical distinctions are outlined: each shared folder is identified by a unique secret (read‑only, read‑write, or temporary) that governs access; communication is encrypted with RSA‑AES; and metadata is conveyed via Bencoded dictionaries rather than traditional .torrent files. Table 1 in the paper enumerates Bencoding fields such as d, l, e, m, peer, share, and nonce, explaining how they map to human‑readable UTF‑8 key‑value pairs. This deterministic structure enables the creation of signature‑based detection rules for Network Intrusion Detection Systems (NIDS) and firewalls.
The core contribution is a five‑stage investigation workflow:
-
Initial Detection – Scan for the default BTSync port (3838) or any custom port, and monitor UDP traffic to the Kademlia‑based DHT. Active peers are identified by their presence in DHT look‑ups or multicast LAN discovery packets.
-
Session Establishment – Capture the handshake where peers exchange a 16‑byte
nonceand the folder’s secret. By parsing the Bencoded payload, investigators can determine whether the session involves a read‑only or read‑write share. -
Data Transfer Analysis – File blocks are transmitted encrypted; each block is accompanied by a SHA‑1 hash for integrity verification. The authors describe how block size, transfer cadence, and timing can be used to infer the total volume of data exchanged without decrypting the payload.
-
Log and Metadata Harvesting – Tracker responses, PEX messages, and DHT updates are logged to reconstruct peer‑to‑peer interaction histories. This step enables the reconstruction of a file’s propagation path, identification of “super‑seed” peers, and correlation with timestamps for timeline building.
-
Evidence Preservation – Captured packets are stored in PCAP format with accompanying metadata (timestamps, secrets, peer IDs). The paper stresses the importance of maintaining chain‑of‑custody documentation to ensure admissibility in court.
To illustrate practical relevance, the authors discuss several malicious use‑cases: industrial espionage, copyright infringement, distribution of illicit child‑exploitation material, and covert data exfiltration. For each scenario they outline specific investigative focal points—for example, detecting the reuse of a read‑write secret across multiple external IPs may indicate coordinated mass distribution, while a sudden surge in DHT look‑ups for a particular folder hash could signal an emerging data leak.
Two real‑world forensic investigations are presented. In the first case, a corporate confidential document set was found to have been synchronized to an external partner’s machine via BTSync. By correlating DHT query logs, captured handshakes, and the folder’s secret, the investigators pinpointed the exact peer that received the data and established a timeline of the exfiltration. In the second case, a suspect’s personal computer was used to share illegal media through BTSync. The authors employed NIDS signatures derived from the Bencoding patterns to flag the traffic, extracted the folder secret, and subsequently identified all participating peers, providing solid evidence for prosecution.
The paper also acknowledges limitations: encrypted payloads remain opaque without the secret key, and DHT‑based peer discovery can be incomplete in heavily firewalled environments. Future work is suggested in the areas of secret‑management analysis, DHT manipulation detection, and the development of automated tooling to integrate BTSync detection into existing forensic suites.
Overall, the study delivers a detailed protocol dissection, a repeatable network‑forensic methodology, and actionable guidance for law‑enforcement and security professionals confronting the growing adoption of BTSync in both legitimate and illicit contexts.
Comments & Academic Discussion
Loading comments...
Leave a Comment