An Anti-attack Model Based on Complex Network Theory in P2P networks
Complex network theory is a useful way to study many real systems. In this paper, an anti-attack model based on complex network theory is introduced. The mechanism of this model is based on dynamic compensation process and reverse percolation process in P2P networks. The main purpose of the paper is: (i) a dynamic compensation process can turn an attacked P2P network into a power-law (PL) network with exponential cutoff; (ii) a local healing process can restore the maximum degree of peers in an attacked P2P network to a normal level; (iii) a restoring process based on reverse percolation theory connects the fragmentary peers of an attacked P2P network together into a giant connected component. In this way, the model based on complex network theory can be effectively utilized for anti-attack and protection purposes in P2P networks.
💡 Research Summary
**
The paper proposes a two‑stage anti‑attack framework for peer‑to‑peer (P2P) networks that leverages complex‑network theory, specifically the properties of power‑law (PL) graphs and percolation theory. The authors first observe that targeted attacks on P2P systems often remove high‑degree (“hub”) peers, causing a sharp reduction in the maximum degree, fragmentation of the network, and distortion of the original PL degree distribution. Traditional defenses based on trust or anonymity require identity information and impose high computational overhead, making them unsuitable for large, fully distributed P2P overlays.
Stage 1 – Dynamic Compensation (Healing).
The model assumes an attacked network characterized by a PL exponent α and a reduced maximum degree d₀. A stretch factor β = d_max/d₀ is defined, where d_max is the desired post‑healing maximum degree. Each peer i, with current degree d_i, independently decides with probability f = β⁰⁻ᵃ to compensate for lost edges. Compensation consists of creating (β − 1)·d_i new edges, selected preferentially (i.e., the probability of attaching to a node of degree k is proportional to k). This local, decentralized process preserves the PL exponent α while expanding the degree cutoff from d₀ to d_max. Monte‑Carlo simulations on a 50 000‑node mesh show that even when a fraction r of nodes is removed preferentially (r up to 0.3), the size of the largest connected component g(r) remains above 0.97, indicating that connectivity is largely retained.
Stage 2 – Reverse Percolation (Connectivity Restoration).
After the healing step, the network may still consist of many small components. The authors model the post‑attack component‑size distribution M(k) using generating functions G₀(x) and G₁(x). They assume a targeted attack probability q_k = m·k^{‑q}, where q controls the aggressiveness of the attack. Even when the attacked PL network lacks a giant component (the condition 3.4785 c q θ + > β holds), adding a modest number of random edges triggers a percolation transition. By randomly matching “dummy” copies of each component (a construction that yields a random graph with degree distribution N(k) = M(k)), the process mimics classic bond percolation: when the edge‑retention probability p exceeds the critical threshold p_c, the fragmented pieces coalesce into a single giant component. The analysis shows that only a small fraction of additional links is required, regardless of the original attack scale.
Simulation Results.
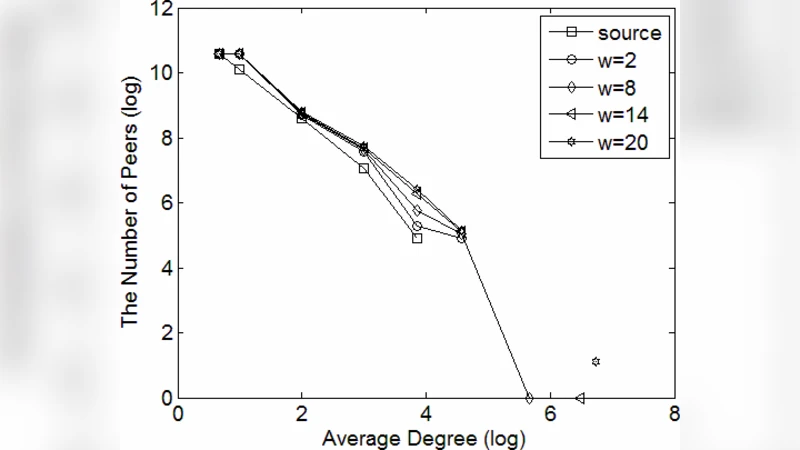
The authors evaluate the healing algorithm for three PL exponents (α = 2.4, 2.8, 3.2) and four stretch factors (β = 2, 8, 14, 20). Degree‑distribution plots demonstrate that for moderate α (2.4) a small β (2) already restores the PL tail, whereas for larger α (3.2) excessive edge addition (β = 20) over‑compensates and distorts the distribution. The optimal β values (β ≈ 14 for α = 2.8, β ≈ 8 for α = 3.2) achieve a balance between restoring the cutoff and preserving the exponent.
Contributions and Limitations.
The paper’s main contributions are: (1) a decentralized, probability‑driven compensation mechanism that keeps the PL exponent unchanged while rebuilding the degree cutoff; (2) an analytical and simulation‑backed demonstration that a reverse percolation step can reconnect fragmented P2P overlays with minimal overhead; (3) a combined framework that does not rely on peer identity, thus preserving privacy and scalability. Limitations include the assumption of uncorrelated degrees, neglect of latency and churn dynamics, and the lack of a cost‑benefit analysis for the extra edges introduced during healing. Future work should address realistic churn models, heterogeneous bandwidth constraints, and adaptive selection of β based on real‑time network metrics.
In summary, the proposed anti‑attack model shows that by exploiting intrinsic structural properties of PL networks—namely, their resilience to preferential attachment and the sharp percolation threshold—P2P systems can autonomously recover from severe targeted attacks with modest additional connections, offering a promising direction for secure, scalable decentralized networking.
Comments & Academic Discussion
Loading comments...
Leave a Comment