Factors Influencing the Adoption of Cloud Incident Handling Strategy: A Preliminary Study in Malaysia
This study seeks to understand the factors influencing the adoption of an incident handling strategy by organisational cloud service users. We propose a conceptual model that draws upon the Situation Awareness (SA) model and Protection Motivation Theory (PMT) to guide this research. 40 organisational cloud service users in Malaysia were surveyed. We also conduct face-to-face interviews with participants from four of the organisations. Findings from the study indicate that four PMT factors (Perceived Vulnerability, Self-Efficacy, Response Efficacy, and Perceived Severity) have a significantly influence on the adoption of cloud incident handling strategy within the organisations. We, therefore, suggest a successful adoption cloud incident handling strategy by organisational cloud service users involves the nexus between these four PMT factors. We also outline future research required to validate the model.
💡 Research Summary
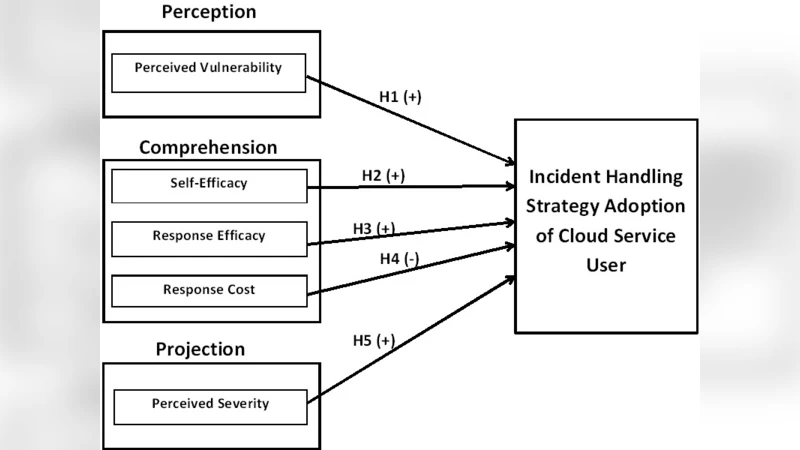
The paper investigates why organizations that use cloud services decide to adopt formal incident‑handling strategies. To explain this decision‑making process, the authors integrate two well‑established theoretical lenses: Situation Awareness (SA) and Protection Motivation Theory (PMT). The SA model contributes a three‑stage cognitive sequence—perception, interpretation, and projection—through which cloud users become aware of threats. PMT adds four motivational constructs: Perceived Vulnerability, Perceived Severity, Self‑Efficacy, and Response Efficacy. By mapping the SA stages onto the PMT variables, the authors propose a unified conceptual model that predicts the intention to adopt a cloud incident‑handling strategy.
Methodologically, the study follows a mixed‑methods design. Quantitatively, a structured questionnaire was administered to 40 organizational cloud users in Malaysia, covering the four PMT constructs and a measure of adoption intention. Responses were captured on a five‑point Likert scale and analyzed using Structural Equation Modeling (SEM). The SEM results show statistically significant positive paths from each of the four PMT factors to adoption intention (Perceived Vulnerability β = 0.31, p < 0.01; Self‑Efficacy β = 0.27, p < 0.05; Response Efficacy β = 0.34, p < 0.01; Perceived Severity β = 0.22, p < 0.05).
Qualitatively, face‑to‑face interviews were conducted with IT managers, security officers, and cloud administrators from four of the surveyed organizations. The interview data were transcribed, coded, and thematically analyzed to triangulate the survey findings. Participants emphasized that Self‑Efficacy is reinforced through regular training and tabletop exercises, while Perceived Vulnerability is heightened when organizations scrutinize service‑level agreements and cloud provider certifications. Response Efficacy was linked to the existence of clear, automated response playbooks and monitoring tools, and Perceived Severity was amplified by recalling high‑profile data‑breach incidents that caused substantial financial and reputational damage.
The convergence of quantitative and qualitative evidence leads the authors to conclude that the four PMT factors jointly drive the adoption of cloud incident‑handling strategies. Moreover, the integration of SA and PMT offers a richer explanatory framework: users first perceive cloud‑related cues, interpret them as threats (Vulnerability and Severity), project the effectiveness of possible responses (Response Efficacy), and finally assess their own capability to execute those responses (Self‑Efficacy).
Limitations include the modest sample size, geographic confinement to Malaysia, and reliance on self‑reported data, which may introduce social desirability bias. The authors also note that the cross‑sectional design cannot capture how motivations evolve over time or during actual incidents.
Future research directions are outlined: (1) expanding the sample to multiple countries and industries to test external validity; (2) incorporating additional organizational variables such as culture, leadership support, and regulatory pressure; (3) conducting longitudinal studies or scenario‑based simulations to observe real‑time decision making; and (4) exploring how emerging technologies—AI‑driven detection, automated remediation, and zero‑trust architectures—interact with the PMT constructs.
From a practical standpoint, the study suggests that cloud‑using organizations should (a) regularly assess and communicate their exposure to cloud‑specific threats to raise Perceived Vulnerability; (b) conduct impact analyses of potential incidents to make Perceived Severity salient; (c) invest in continuous skill development and confidence‑building exercises to boost Self‑Efficacy; and (d) design, test, and automate response procedures that demonstrably reduce risk, thereby strengthening Response Efficacy. By addressing these four levers, organizations can create a more resilient posture and increase the likelihood of successfully adopting comprehensive cloud incident‑handling strategies.