Software as a Service: Analyzing Security Issues
Software-as-a-service (SaaS) is a type of software service delivery model which encompasses a broad range of business opportunities and challenges. Users and service providers are reluctant to integrate their business into SaaS due to its security concerns while at the same time they are attracted by its benefits. This article highlights SaaS utility and applicability in different environments like cloud computing, mobile cloud computing, software defined networking and Internet of things. It then embarks on the analysis of SaaS security challenges spanning across data security, application security and SaaS deployment security. A detailed review of the existing mainstream solutions to tackle the respective security issues mapping into different SaaS security challenges is presented. Finally, possible solutions or techniques which can be applied in tandem are presented for a secure SaaS platform.
💡 Research Summary
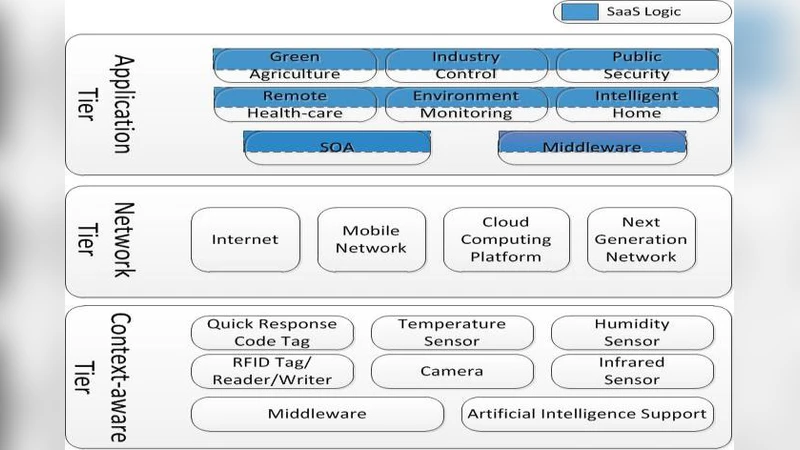
The paper provides a comprehensive examination of security concerns inherent to the Software‑as‑a‑Service (SaaS) delivery model while acknowledging its growing appeal across a variety of emerging technology domains. It first outlines the breadth of SaaS applicability, extending beyond traditional cloud computing to include mobile cloud computing, software‑defined networking (SDN), and the Internet of Things (IoT). In each of these environments, SaaS introduces a highly distributed, multi‑tenant architecture that amplifies the attack surface and creates novel challenges for data confidentiality, integrity, and availability.
Security challenges are organized into three principal categories: data security, application security, and deployment security.
-
Data Security – The authors discuss static and in‑transit encryption, robust key‑management practices, and comprehensive audit logging. They emphasize that key isolation and rotation are critical in multi‑tenant settings, where a compromised key could expose data across multiple customers. The paper maps existing solutions such as cloud‑native Key Management Services (e.g., AWS KMS, Azure Key Vault) and third‑party Hardware Security Modules to these requirements, noting that many deployments still rely on ad‑hoc key handling that undermines overall security posture.
-
Application Security – SaaS applications are typically built around APIs and micro‑services, making them vulnerable to OWASP Top‑10 issues such as injection, broken authentication, and insecure deserialization. The authors evaluate protective measures including API gateways, service‑mesh based zero‑trust enforcement, Runtime Application Self‑Protection (RASP), static and dynamic code analysis, and the integration of security checks into CI/CD pipelines (DevSecOps). They argue that while each tool addresses a specific vector, a cohesive strategy that spans development, testing, and production is essential to prevent exploitation of runtime vulnerabilities.
-
Deployment Security – The paper examines the security of the underlying virtualization and container orchestration layers. Hardening hypervisors, applying Kubernetes security best practices, network segmentation, and DoS mitigation are highlighted. The authors point out the difficulty of maintaining consistent security policies across multi‑cloud and hybrid environments and propose the use of declarative security policies codified through Infrastructure‑as‑Code (IaC) frameworks. Cloud Security Posture Management (CSPM) and Cloud Workload Protection Platforms (CWPP) are identified as key enablers for continuous compliance and workload hardening.
After cataloguing mainstream solutions, the authors identify a critical gap: most existing tools operate in isolation, focusing on a single layer of the stack. This siloed approach limits visibility and hampers coordinated incident response. Consequently, the paper advocates for an integrated, multi‑layered security framework that unifies data protection, application safeguards, and deployment hardening under a single governance model.
In the forward‑looking section, the authors explore emerging techniques that could be combined to reinforce SaaS security. Blockchain‑based immutable logs are suggested for tamper‑evident data provenance. Homomorphic encryption and differential privacy are discussed as ways to process encrypted data without exposing raw values, thereby preserving confidentiality even during analytics. Additionally, AI/ML‑driven anomaly detection and behavior‑based authentication are proposed to provide real‑time threat identification and adaptive access control.
Overall, the paper concludes that a layered defense strategy—integrating proven cloud‑native security services with cutting‑edge cryptographic and AI technologies—offers the most promising path toward a trustworthy SaaS ecosystem. By addressing the interdependencies among data, application, and deployment security, service providers and customers can mitigate risk, comply with regulatory requirements, and fully realize the business benefits of SaaS.
Comments & Academic Discussion
Loading comments...
Leave a Comment