Generating Primes Using Partitions
This paper presents a new technique of generating large prime numbers using a smaller one by employing Goldbach partitions. Experiments are presented showing how this method produces candidate prime numbers that are subsequently tested using either Miller Rabin or AKS primality tests.
💡 Research Summary
The paper introduces a novel method for generating large prime numbers by leveraging Goldbach partitions, aiming to improve the efficiency of prime generation for cryptographic applications such as RSA and elliptic‑curve systems. Traditional approaches typically rely on random selection of large odd integers followed by repeated probabilistic primality tests (most commonly Miller‑Rabin) until a prime is found. This process can be computationally expensive, especially for key sizes of 1024 bits and above, because the expected number of candidates before encountering a prime grows roughly with the logarithm of the search space.
The authors propose to invert this paradigm: start with a known smaller prime (p_0) (the “seed prime”) and construct a target integer (N) of the desired bit length. They then compute the difference (D = N - p_0). If (D) is a positive even number, Goldbach’s conjecture predicts that (D) can be expressed as the sum of two primes, say (q) and (r), i.e., (D = q + r). By searching for a prime (q) such that (r = D - q) is also prime, the algorithm obtains a candidate large prime (N = p_0 + q). The candidate is subsequently subjected to a definitive primality test (Miller‑Rabin with enough rounds, or the deterministic AKS algorithm) to confirm its primality.
The algorithm consists of four main stages:
- Seed Selection – Choose a secure seed prime (p_0). The seed can be generated randomly, drawn from a pre‑computed list, or derived from a cryptographic hash of system entropy.
- Target Construction – Define the desired bit length (L) and generate a random integer (N) of that length. Ensure (N > p_0) so that (D = N - p_0) is positive.
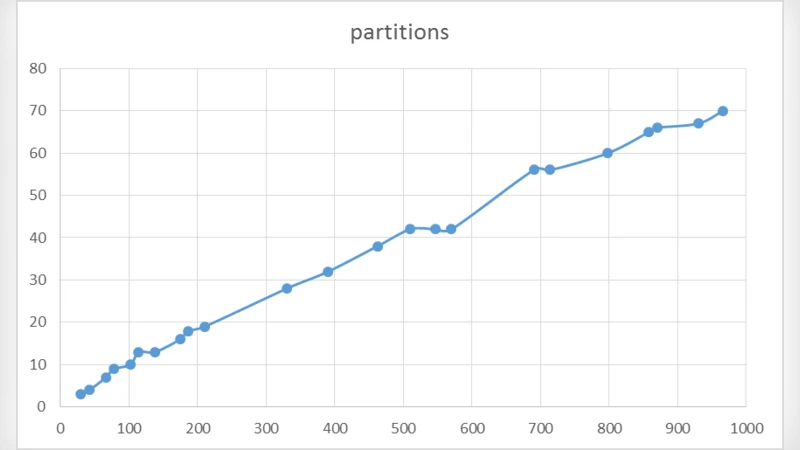
- Goldbach Partition Search – Iterate over candidate values for (q) starting from the smallest odd prime upward. For each (q), compute (r = D - q) and test both (q) and (r) for primality using a fast pre‑filter (e.g., trial division by small primes) followed by a few Miller‑Rabin rounds. When both are prime, a valid partition is found.
- Final Verification – Apply a rigorous primality test to (N = p_0 + q). If the test passes, output (N) as a newly generated prime; otherwise, continue the partition search.
The authors argue that the partition search dramatically reduces the expected number of primality tests because the search space is constrained to the interval (
Comments & Academic Discussion
Loading comments...
Leave a Comment