Machine-Readable Privacy Certificates for Services
Privacy-aware processing of personal data on the web of services requires managing a number of issues arising both from the technical and the legal domain. Several approaches have been proposed to matching privacy requirements (on the clients side) and privacy guarantees (on the service provider side). Still, the assurance of effective data protection (when possible) relies on substantial human effort and exposes organizations to significant (non-)compliance risks. In this paper we put forward the idea that a privacy certification scheme producing and managing machine-readable artifacts in the form of privacy certificates can play an important role towards the solution of this problem. Digital privacy certificates represent the reasons why a privacy property holds for a service and describe the privacy measures supporting it. Also, privacy certificates can be used to automatically select services whose certificates match the client policies (privacy requirements). Our proposal relies on an evolution of the conceptual model developed in the Assert4Soa project and on a certificate format specifically tailored to represent privacy properties. To validate our approach, we present a worked-out instance showing how privacy property Retention-based unlinkability can be certified for a banking financial service.
💡 Research Summary
The paper addresses the growing difficulty of ensuring privacy protection in service‑oriented environments, where technical and legal requirements often diverge. Existing privacy policy languages allow users to express their data‑handling preferences, but service providers typically publish self‑descriptions in natural language that cannot be processed automatically. Early certification schemes such as EuroPriSe and Trust‑E adopt an all‑or‑nothing compliance model and rely on human‑readable documents, limiting fine‑grained matching between client requirements and provider guarantees.
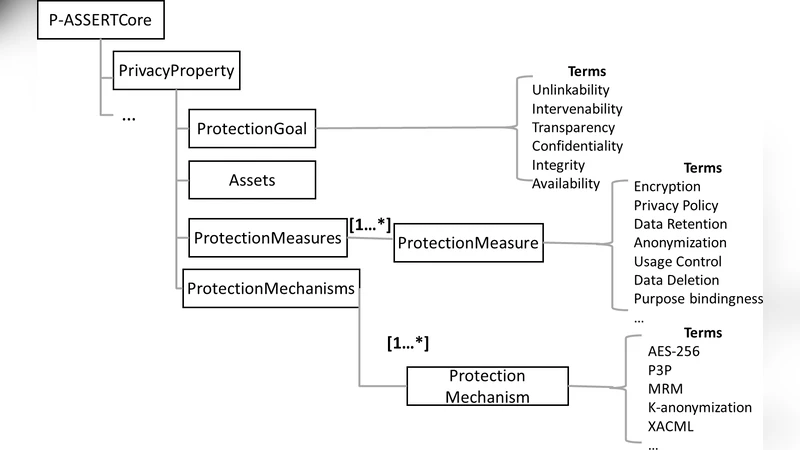
To overcome these limitations, the authors extend the Assert4Soa security‑certification framework and propose a dedicated privacy‑certificate format called p‑Assert. A p‑Assert is a signed XML document composed of two main sections: Core and Evidence. The Core section contains structured metadata about the certified service (Target of Certification, Target of Evaluation), a hierarchical description of the privacy property, and three layers of abstraction—Protection Goal, Protection Measures, and Protection Mechanisms. Protection goals follow the “privacy‑by‑design” principles of Transparency, Unlinkability, Intervenability, and Confidentiality. Each goal is linked to concrete measures (e.g., limited retention period, anonymisation) and to specific technical mechanisms (e.g., k‑anonymity with a defined k value). The Evidence section records the third‑party assessment performed by a certification authority, including formal models (such as Symbolic Transition Systems), test suites, execution results, and methodological details. By separating the evaluated portion of the system (TOE) from the overall service description, the format supports compositional services and enables automated reasoning.
The authors validate the approach with a concrete use case: an IFX‑based banking deposit/withdrawal service that processes scanned cheques. A client may specify a retention period for the stored cheque image; the service must delete the image after the period expires. The certification authority evaluates the retention‑management logic, runs deletion tests, and records the outcomes in the Evidence part. The resulting p‑Assert certifies the property “Retention‑based Unlinkability,” meaning that personal data cannot be linked across domains after the defined retention period. Clients can now automatically discover services whose certificates satisfy policies such as “retention ≤ 30 days” without manual inspection.
Beyond the case study, the paper discusses broader benefits: increased transparency for users, a trusted third‑party “stamp of approval” for providers, and the possibility of automated service discovery, comparison, and composition based on privacy guarantees. It also outlines future work, including standardisation of protection goals and measures, development of certificate management infrastructures, and alignment with evolving legal frameworks. In sum, the work presents a machine‑readable, third‑party‑validated privacy certification scheme that bridges the gap between user privacy requirements and provider assurances, paving the way for more trustworthy, privacy‑aware service ecosystems.
Comments & Academic Discussion
Loading comments...
Leave a Comment