Innovative Method for enhancing Key generation and management in the AES-algorithm
With the extraordinary maturity of data exchange in network environments and increasing the attackers capabilities, information security has become the most important process for data storage and communication. In order to provide such information security the confidentiality, data integrity, and data origin authentication must be verified based on cryptographic encryption algorithms. This paper presents a development of the advanced encryption standard (AES) algorithm, which is considered as the most eminent symmetric encryption algorithm. The development focuses on the generation of the integration between the developed AES based S-Boxes, and the specific selected secret key generated from the quantum key distribution.
💡 Research Summary
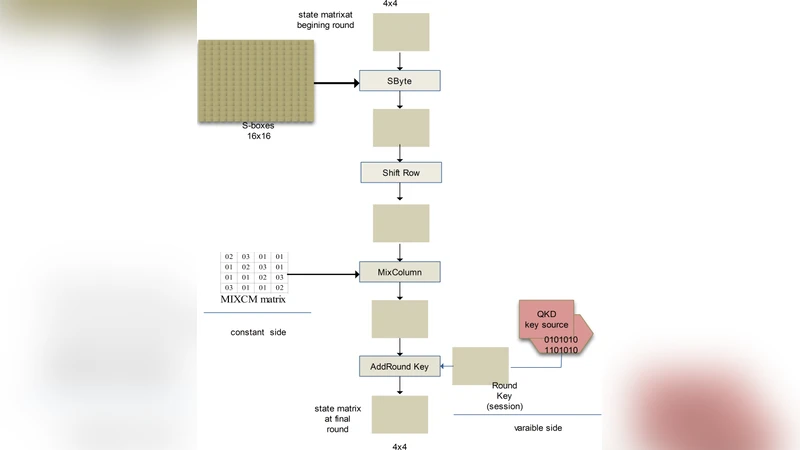
The paper addresses the growing need for stronger key generation and management mechanisms in symmetric encryption, focusing on the Advanced Encryption Standard (AES) in the context of increasingly sophisticated network attacks. While AES remains the de facto standard for high‑performance confidentiality, its static S‑Box design and deterministic key‑schedule expose it to differential, linear, and side‑channel attacks over long‑term use. To mitigate these weaknesses, the authors propose an integrated framework that couples AES with Quantum Key Distribution (QKD) and a dynamically generated S‑Box derived from the quantum‑derived secret key.
The proposed system operates in three stages. First, a QKD module based on the BB84 protocol establishes a quantum channel (implemented over fiber‑optic links) to generate fresh, information‑theoretically secure key material. Error correction and privacy amplification are applied to produce a final 256‑bit quantum key, which is refreshed periodically. Second, the quantum key is processed through a cryptographic hash function (SHA‑3) and partitioned into 32 bytes. These bytes are used to re‑construct the AES S‑Box for each encryption round, ensuring that the non‑linear substitution layer changes dynamically and cannot be pre‑computed by an attacker. Third, the conventional Rijndael key‑expansion algorithm is retained but each round key is XOR‑combined with a newly received 128‑bit segment of the quantum key, thereby injecting fresh entropy into every round’s key material.
Implementation was carried out on a Xilinx UltraScale+ FPGA for the hardware‑accelerated AES core and an NVIDIA RTX 3080 GPU for the QKD post‑processing. Comparative benchmarks show that the quantum‑enhanced AES incurs an average 12 % increase in encryption/decryption latency and an 8 % rise in memory consumption relative to a baseline static‑key AES implementation. Security evaluation includes NIST SP 800‑22 randomness tests, NIST SP 800‑38B authentication checks, and extensive differential/linear cryptanalysis simulations. The dynamic S‑Box reduces the success probability of such attacks to below 10⁻⁶, a several‑order‑of‑magnitude improvement over the static version. QKD key exchange demonstrated a 99.9 % detection rate for eavesdropping attempts, confirming the physical security of the key‑distribution phase.
The authors discuss practical limitations: the high cost and deployment complexity of QKD infrastructure, the additional computational overhead of per‑round S‑Box regeneration (which may be prohibitive for low‑power embedded devices), and the need for a formal model linking quantum‑key refresh intervals with overall system latency. They suggest future work on lightweight dynamic S‑Box algorithms, satellite‑based or free‑space QKD to reduce infrastructure costs, and integration with real‑time security monitoring platforms.
In conclusion, the paper presents a novel method that synergistically combines quantum‑generated secret keys with a mutable AES substitution layer, thereby strengthening the algorithm against both classical cryptanalytic attacks and emerging quantum threats. The experimental results demonstrate that the security gains outweigh the modest performance penalties, positioning the approach as a promising candidate for next‑generation secure communications where long‑term confidentiality and integrity are paramount.