A Review of Man-in-the-Middle Attacks
This paper presents a survey of man-in-the-middle (MIM) attacks in communication networks and methods of protection against them. In real time communication, the attack can in many situations be discovered by the use of timing information. The most common attacks occur due to Address Resolution Protocol (ARP) cache poisoning, DNS spoofing, session hijacking, and SSL hijacking.
💡 Research Summary
The paper provides a comprehensive survey of man‑in‑the‑middle (MITM) attacks that target modern communication networks and examines the state‑of‑the‑art defensive techniques. It begins by defining MITM attacks, describing how an adversary positions itself between two legitimate parties to intercept, modify, or drop traffic, and outlines the historical evolution of these threats from early LAN‑based exploits to sophisticated multi‑layer attacks seen in cloud and IoT environments.
Four primary attack vectors are examined in depth. The first, ARP cache poisoning, exploits the lack of authentication in the Address Resolution Protocol. By broadcasting forged ARP replies, an attacker corrupts the IP‑to‑MAC mapping tables of hosts on a local Ethernet segment, causing traffic to be redirected through the attacker’s machine. The paper reviews detection methods such as monitoring abnormal ARP traffic volume, sudden MAC address changes, and inconsistencies between DHCP lease information and ARP tables. Defensive measures discussed include static ARP entries, Dynamic ARP Inspection (DAI) on managed switches, port‑security features that limit the number of MAC addresses per port, and the use of IPv6 Secure Neighbor Discovery (SEND) to mitigate analogous NDP attacks.
The second vector, DNS spoofing and cache poisoning, targets the Domain Name System, a critical component for translating human‑readable names into IP addresses. Attackers can inject malicious responses into recursive resolvers or manipulate the cache of authoritative servers, thereby steering users to malicious sites. The survey highlights the role of DNSSEC in providing cryptographic signatures for DNS records, the adoption of encrypted transport protocols such as DNS‑over‑HTTPS (DoH) and DNS‑over‑TLS (DoT), and operational best practices like limiting TTL values, rate‑limiting suspicious query patterns, and employing split‑horizon DNS architectures to reduce exposure.
The third vector, session hijacking, focuses on the theft of session identifiers after a user has successfully authenticated. The paper categorizes attacks into cookie theft via cross‑site scripting (XSS), network sniffing of unencrypted traffic, and session fixation where an attacker forces a victim to use a known session ID. Mitigation strategies include setting the Secure, HttpOnly, and SameSite attributes on cookies, rotating session IDs immediately after login, enforcing short session lifetimes, and mandating TLS for all application‑level traffic to protect cookies from eavesdropping.
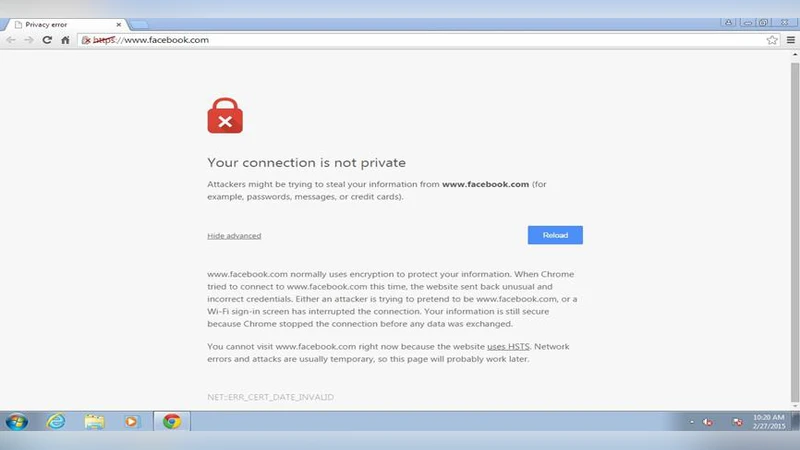
The fourth vector, SSL/TLS hijacking, examines how adversaries can interfere with the TLS handshake. Techniques such as certificate spoofing, rogue Certificate Authority (CA) issuance, and SSL stripping (downgrading HTTPS to HTTP) are described. Countermeasures discussed are certificate pinning, HTTP Strict Transport Security (HSTS) policies, the deployment of Certificate Transparency logs for real‑time detection of unauthorized certificates, and the exclusive use of modern TLS versions (1.3) with strong cipher suites.
A notable contribution of the paper is the discussion of timing‑based detection. By measuring round‑trip time (RTT) variations, packet reordering, and retransmission patterns, it is possible to spot the subtle latency introduced when an attacker processes and forwards packets. The authors propose a hybrid detection framework that combines statistical anomaly detection with machine‑learning classifiers trained on baseline latency profiles. They also advocate for multi‑path routing and traffic sharding to reduce the impact of a single compromised node.
The survey emphasizes a layered defense strategy. It argues that firewalls and traditional IDS/IPS solutions alone cannot protect against encrypted or internal‑network attacks. Instead, security controls must be integrated across the OSI layers: physical (802.1X port authentication), link (MACsec), network (IPsec tunnels), transport (TLS/DTLS), and application (OAuth 2.0, OpenID Connect). The paper stresses the importance of continuous patch management, configuration audits, and user awareness training, especially to mitigate insider threats and social‑engineering vectors that facilitate MITM attacks.
In conclusion, the paper synthesizes current knowledge on MITM threats, provides a taxonomy of attack techniques, evaluates detection and mitigation mechanisms, and outlines future research directions. These include AI‑driven real‑time anomaly detection, post‑quantum cryptographic protocols for TLS, and scalable MITM‑resilient architectures for emerging environments such as edge computing, 5G, and massive IoT deployments.
Comments & Academic Discussion
Loading comments...
Leave a Comment