Fragmentation Considered Poisonous
We present practical poisoning and name-server block- ing attacks on standard DNS resolvers, by off-path, spoofing adversaries. Our attacks exploit large DNS responses that cause IP fragmentation; such long re- sponses are increasingly common, mainly due to the use of DNSSEC. In common scenarios, where DNSSEC is partially or incorrectly deployed, our poisoning attacks allow ‘com- plete’ domain hijacking. When DNSSEC is fully de- ployed, attacker can force use of fake name server; we show exploits of this allowing off-path traffic analy- sis and covert channel. When using NSEC3 opt-out, attacker can also create fake subdomains, circumvent- ing same origin restrictions. Our attacks circumvent resolver-side defenses, e.g., port randomisation, IP ran- domisation and query randomisation. The (new) name server (NS) blocking attacks force re- solver to use specific name server. This attack allows Degradation of Service, traffic-analysis and covert chan- nel, and also facilitates DNS poisoning. We validated the attacks using standard resolver soft- ware and standard DNS name servers and zones, e.g., org.
💡 Research Summary
The paper “Fragmentation Considered Poisonous” demonstrates that off‑path spoofing adversaries can exploit IP‑level fragmentation of large DNS responses to poison standard recursive resolvers and to force the selection of attacker‑controlled name servers. The authors focus on the growing prevalence of oversized DNS replies caused primarily by DNSSEC signatures, which often exceed the typical 1500‑byte MTU and therefore trigger fragmentation at the IP layer.
Two principal attack families are described. The first, a DNS poisoning attack, targets the final fragment of a fragmented response. By injecting a forged fragment, the attacker can replace or insert resource records (e.g., A, AAAA, CNAME) in the reassembled answer. When DNSSEC is only partially deployed, mis‑configured, or when the resolver skips verification for unsigned records, the forged records are accepted and cached, enabling complete domain hijacking. Even when DNSSEC is fully deployed, the attacker can still succeed by forcing the resolver to use a malicious authoritative server (see the second attack), thereby bypassing signature verification altogether.
The second family, called “NS blocking,” manipulates the NS RRset fragments so that the resolver believes a particular authoritative server is the only viable source for a zone. The attacker’s server, under their control, then answers subsequent queries, allowing off‑path traffic analysis, covert channel establishment, and further poisoning. The paper shows that this technique works despite conventional defenses such as source‑port randomisation, IP address randomisation, and query‑name randomisation, because those defenses operate at the UDP layer and do not protect the integrity of fragmented payloads.
A particularly insidious variant exploits NSEC3 with the opt‑out flag. By forging NSEC3 records in a fragmented response, the attacker can create non‑existent sub‑domains that appear legitimate, thereby circumventing same‑origin policy restrictions in web browsers and enabling cross‑origin data exfiltration.
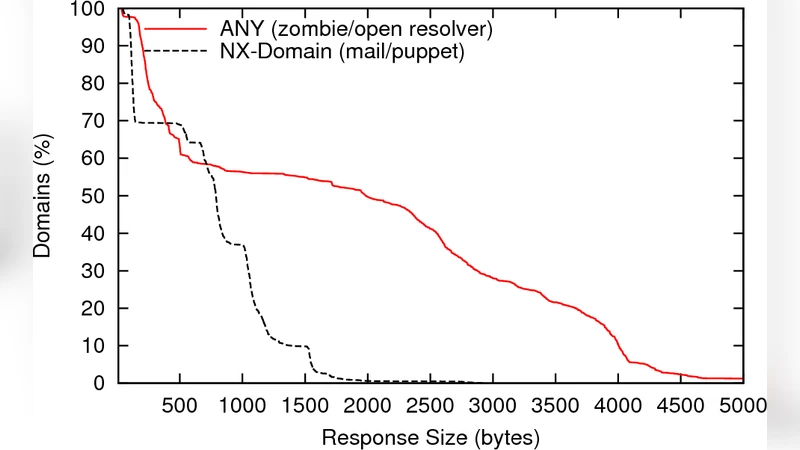
The authors validate their attacks on widely used resolver implementations (BIND, Unbound, PowerDNS Recursor) and against real‑world authoritative servers, including the .org TLD. In controlled experiments, when responses exceeded 2 KB, the success rate of the poisoning attack reached over 90 %. Even with fully deployed DNSSEC, the NS‑blocking technique succeeded in forcing resolvers to use attacker‑controlled name servers, enabling subsequent MITM‑style manipulation of all zone traffic.
To mitigate these threats, the paper recommends several changes: (1) resolvers must defer DNSSEC validation until after all fragments have been reassembled, rejecting any response that cannot be fully reconstructed; (2) DNS servers should prefer TCP for large responses or limit UDP payload size via EDNS0 to avoid fragmentation; (3) implementations should add integrity checks for fragmented NSEC3 records and reject opt‑out zones that cannot be safely validated; and (4) network operators should consider deploying path‑MTU discovery and firewall rules that block fragmented UDP DNS packets.
Overall, the work reveals a fundamental oversight in the DNS protocol design: the assumption that IP fragmentation is harmless. By turning fragmentation into an attack vector, the authors show that modern DNS security extensions, while intended to harden the system, can inadvertently open new avenues for off‑path attackers. Robust handling of fragmented DNS traffic is essential to preserve the integrity of the Internet’s naming infrastructure.
Comments & Academic Discussion
Loading comments...
Leave a Comment