Feature-Aware Verification
A software product line is a set of software products that are distinguished in terms of features (i.e., end-user–visible units of behavior). Feature interactions —situations in which the combination of features leads to emergent and possibly critical behavior— are a major source of failures in software product lines. We explore how feature-aware verification can improve the automatic detection of feature interactions in software product lines. Feature-aware verification uses product-line verification techniques and supports the specification of feature properties along with the features in separate and composable units. It integrates the technique of variability encoding to verify a product line without generating and checking a possibly exponential number of feature combinations. We developed the tool suite SPLverifier for feature-aware verification, which is based on standard model-checking technology. We applied it to an e-mail system that incorporates domain knowledge of AT&T. We found that feature interactions can be detected automatically based on specifications that have only feature-local knowledge, and that variability encoding significantly improves the verification performance when proving the absence of interactions.
💡 Research Summary
The paper introduces “feature‑aware verification,” a novel approach for automatically detecting feature interactions in software product lines (SPLs). In an SPL, a product is assembled from a set of features—end‑user visible units of behavior—by composing feature modules. Interactions arise when the combination of features yields emergent behavior that is not present in any single feature, often leading to critical failures. Traditional techniques either require global specifications that know about all other features, or they generate every possible product configuration and verify each one separately, which quickly becomes infeasible due to combinatorial explosion.
Feature‑aware verification tackles both problems by (1) providing a lightweight, composable specification language for individual features, and (2) employing variability encoding to verify the entire product line in a single model‑checking run. The specification language is automaton‑based: each feature can declare “introductions” (auxiliary functions or data structures), “shadows” (additional fields added to existing structures), and “intercepts” that hook before or after specific function calls. Within these intercepts, a feature can record local state and, if a safety property is violated, invoke a special “fail” command that marks the execution as erroneous. Crucially, a feature’s specification only references the code it directly extends or uses; it does not need to be aware of any other feature’s implementation or specification.
Variability encoding lifts all feature implementations and their specifications into a single “product simulator.” Each feature is guarded by a Boolean configuration variable (e.g., #if FEATURE_X) and the feature model’s constraints are encoded as propositional formulas over these variables. The resulting program contains every possible product as a conditional execution path. By feeding this encoded program to an off‑the‑shelf model checker (such as NuSMV or SPIN), the verifier can explore all configurations simultaneously. The authors prove that this encoding is sound and complete: a property holds for every valid product if and only if it holds for the encoded model.
The authors implemented the approach in the SPLverifier tool chain, which automatically (i) parses feature modules written in C, (ii) generates the variability‑encoded program, (iii) injects the automaton specifications, and (iv) invokes a chosen model checker. To evaluate the method, they used a realistic case study: an AT&T email client product line consisting of four features—EmailClient (base), Encrypt, Decrypt, and Forward. The interaction of interest occurs when Encrypt and Forward are both selected: an encrypted email received by a host that forwards it to a third host may be sent in clear text if the third host’s public key is unknown, violating the Encrypt feature’s safety rule (“encrypted mail must never be sent unencrypted”).
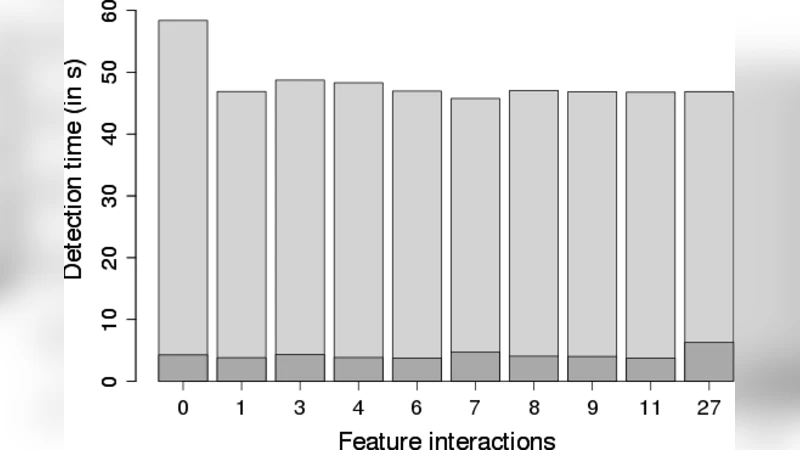
Experiments compared two verification strategies: (a) brute‑force generation and checking of each individual product, and (b) a single run on the variability‑encoded model. With four features there are 2⁴ = 16 possible configurations. The brute‑force approach required generating and model‑checking each product separately, taking roughly 30 minutes in total. The variability‑encoded approach required only one model‑checking run, completing in about 1–2 minutes—a speed‑up of more than an order of magnitude. Moreover, the approach successfully detected the unsafe interaction using only the local specification of Encrypt, without any knowledge of Forward’s implementation.
The paper answers two research questions. First, it demonstrates that feature‑local specifications are sufficient for automatic interaction detection, confirming Hall’s conjecture that global knowledge is not mandatory. Second, it shows that variability encoding dramatically improves verification performance, especially when the verification task is to prove the absence of unsafe interactions or when the product line contains few violating configurations. The authors also present a simple analytical model predicting when variability encoding yields benefits, based on the ratio of interacting to non‑interacting configurations.
In summary, the contribution consists of (1) a composable, automaton‑based specification language for features, (2) a formally proven variability‑encoding technique that enables single‑run verification of entire product lines, (3) the SPLverifier tool chain that integrates these ideas with existing model‑checking technology, and (4) an empirical validation on a realistic email client product line showing both complete detection of known interactions and substantial performance gains. This work advances the state of the art in SPL verification by reconciling modular feature development with scalable, automated safety analysis.
Comments & Academic Discussion
Loading comments...
Leave a Comment