Information-theoretically Secure Regenerating Codes for Distributed Storage
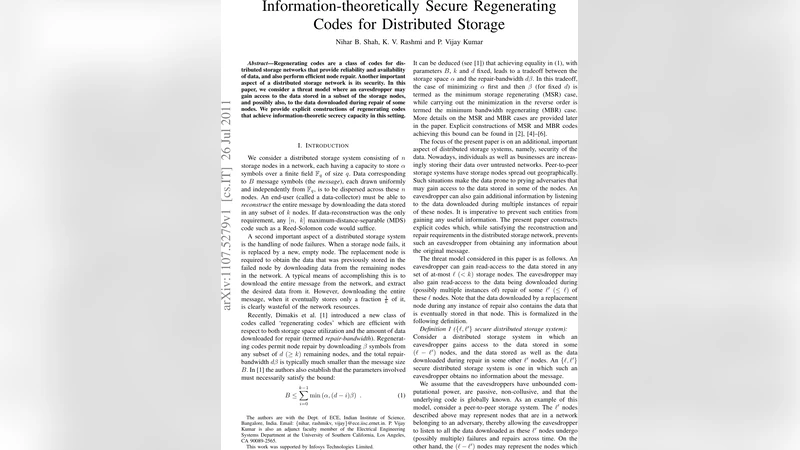
Regenerating codes are a class of codes for distributed storage networks that provide reliability and availability of data, and also perform efficient node repair. Another important aspect of a distributed storage network is its security. In this paper, we consider a threat model where an eavesdropper may gain access to the data stored in a subset of the storage nodes, and possibly also, to the data downloaded during repair of some nodes. We provide explicit constructions of regenerating codes that achieve information-theoretic secrecy capacity in this setting.
💡 Research Summary
The paper addresses the problem of providing information‑theoretic secrecy in distributed storage systems that employ regenerating codes for efficient node repair. In the considered threat model, an eavesdropper can read the data stored in up to ℓ (< k) storage nodes and, in addition, may observe the data downloaded during the repair of up to ℓ′ (≤ ℓ) of those nodes. This {ℓ, ℓ′} model captures realistic attacks on peer‑to‑peer storage where some compromised nodes are repeatedly repaired while others are only temporarily exposed.
The authors first recall the fundamental storage‑repair trade‑off derived by Dimakis et al.: for a system with n nodes, each storing α symbols, and a newcomer contacting any d nodes and downloading β symbols from each (total repair bandwidth dβ), the file size B must satisfy
B ≤ ∑{i=0}^{k‑1} min(α,(d‑i)β).
When secrecy constraints are imposed, Pawar et al. showed that the maximum securely storable file size B(s) obeys
B(s) ≤ ∑{i=ℓ}^{k‑1} min(α,(d‑i)β).
Intuitively, the ℓ compromised nodes contribute zero information, so only the remaining (k‑ℓ) nodes can be used for reconstruction.
The main contribution of the paper is to achieve this bound for both the Minimum‑Bandwidth Regenerating (MBR) point and the Minimum‑Storage Regenerating (MSR) point, for all system parameters
Comments & Academic Discussion
Loading comments...
Leave a Comment