Stegobot: construction of an unobservable communication network leveraging social behavior
We propose the construction of an unobservable communications network using social networks. The communication endpoints are vertices on a social network. Probabilistically unobservable communication channels are built by leveraging image steganography and the social image sharing behavior of users. All communication takes place along the edges of a social network overlay connecting friends. We show that such a network can provide decent bandwidth even with a far from optimal routing mechanism such as restricted flooding. We show that such a network is indeed usable by constructing a botnet on top of it, called Stegobot. It is designed to spread via social malware attacks and steal information from its victims. Unlike conventional botnets, Stegobot traffic does not introduce new communication endpoints between bots. We analyzed a real-world dataset of image sharing between members of an online social network. Analysis of Stegobot’s network throughput indicates that stealthy as it is, it is also functionally powerful – capable of channeling fair quantities of sensitive data from its victims to the botmaster at tens of megabytes every month.
💡 Research Summary
The paper introduces Stegobot, a novel botnet architecture that achieves covert communication by exploiting the natural image‑sharing behavior of online social networks (OSNs). Unlike traditional botnets that rely on dedicated command‑and‑control (C&C) servers or peer‑to‑peer overlays, Stegobot embeds commands and exfiltrated data inside JPEG images using advanced steganography (the YASS scheme). These stego‑images are then uploaded and downloaded through the OSN’s normal friend‑to‑friend interactions, so that the only communication links that exist are the existing social edges between users. Consequently, no new IP addresses, ports, or protocols are introduced, making the traffic indistinguishable from legitimate OSN activity.
The threat model assumes a global passive adversary that can monitor all network traffic but cannot see inside the encrypted or steganographic payloads. Infection is achieved via social‑malware attacks: an attacker sends a malicious attachment that appears to come from a trusted contact; once a single victim is compromised, the malware automatically propagates to the victim’s contacts by embedding the payload in future email or OSN attachments. The authors argue that because OSN graphs are scale‑free (power‑law degree distribution with exponent ≈2), the botnet remains robust even if a substantial fraction of nodes are cleaned.
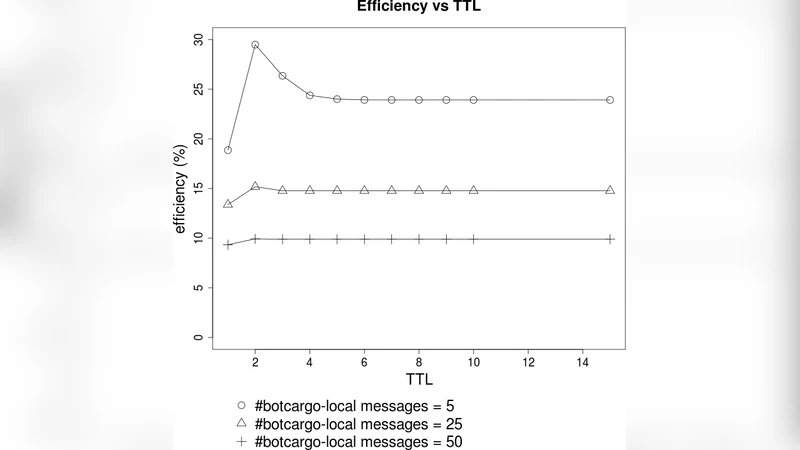
Technical contributions include: (1) a detailed analysis of JPEG steganography capacity, showing that YASS can reliably embed ≈0.05 bits per non‑zero AC DCT coefficient while remaining undetectable at that rate; (2) an empirical study of Facebook’s image processing pipeline, which effectively applies JPEG compression with a quality factor around Q≈75. By resizing images to 720×720 and re‑encoding them before embedding, the authors achieve a low bit‑error‑rate (BER) after upload‑download cycles. (3) a simple routing protocol called “restricted flooding” where each bot forwards stego‑images to all of its friends, and the botmaster collects data by periodically downloading images posted by its own friends. Bandwidth throttling is used to balance locally generated payloads versus forwarded payloads, reducing duplicate transmissions.
Experimental evaluation uses a real‑world dataset of 116 images and a snapshot of a Facebook‑like social graph. Results demonstrate that, despite the simplicity of restricted flooding, the network can deliver tens of megabytes of exfiltrated data per month to the botmaster—comparable to many conventional botnets—while maintaining a channel efficiency of roughly 30 % (percentage of forwarded payloads that successfully reach the botmaster). Duplicate message counts are modest, and overall botnet bandwidth scales with the number of active edges in the social graph.
From a security perspective, Stegobot’s design eliminates the classic C&C footprint, thwarting detection techniques based on unusual traffic patterns, DNS queries, or anomalous server connections. The reliance on steganography further complicates deep‑packet inspection, as state‑of‑the‑art detectors exhibit high false‑positive rates at the low embedding rates used. However, the approach is not without limitations: it depends on the OSN’s image handling policies (e.g., automatic downloading, compression parameters). Any change in the platform’s image processing pipeline could degrade or destroy the covert channel. Moreover, the initial infection still requires successful social‑phishing, so traditional email security measures remain relevant.
In conclusion, the paper demonstrates that a botnet can be built entirely on top of existing social interactions, achieving both stealth and functional throughput. The authors suggest future work on more sophisticated routing (e.g., adaptive path selection), extending the concept to other media (videos, audio), and developing adaptive steganographic schemes that dynamically adjust embedding rates to evade evolving detection algorithms. This work opens a new research direction at the intersection of social network analysis, information hiding, and malware design.
Comments & Academic Discussion
Loading comments...
Leave a Comment