Elliptic Curve Based Zero Knowledge Proofs and Their Applicability on Resource Constrained Devices
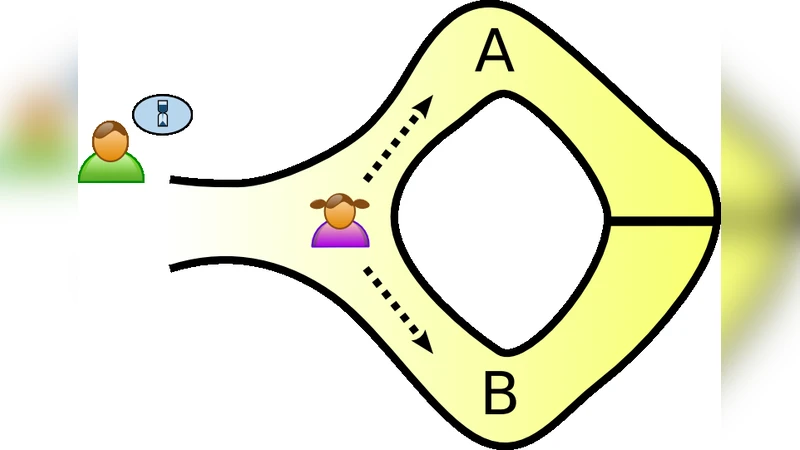
Elliptic Curve Cryptography (ECC) is an attractive alternative to conventional public key cryptography, such as RSA. ECC is an ideal candidate for implementation on constrained devices where the major computational resources i.e. speed, memory are limited and low-power wireless communication protocols are employed. That is because it attains the same security levels with traditional cryptosystems using smaller parameter sizes. Moreover, in several application areas such as person identification and eVoting, it is frequently required of entities to prove knowledge of some fact without revealing this knowledge. Such proofs of knowledge are called Zero Knowledge Interactive Proofs (ZKIP) and involve interactions between two communicating parties, the Prover and the Verifier. In a ZKIP, the Prover demonstrates the possesion of some information (e.g. authentication information) to the Verifier without disclosing it. In this paper, we focus on the application of ZKIP protocols on resource constrained devices. We study well-established ZKIP protocols based on the discrete logarithm problem and we transform them under the ECC setting. Then, we implement the proposed protocols on Wiselib, a generic and open source algorithmic library. Finally, we present a thorough evaluation of the protocols on two popular hardware platforms equipped with low end microcontrollers (Jennic JN5139, TI MSP430) and 802.15.4 RF transceivers, in terms of code size, execution time, message size and energy requirements. To the best of our knowledge, this is the first attempt of implementing and evaluating ZKIP protocols with emphasis on low-end devices. This work’s results can be used from developers who wish to achieve certain levels of security and privacy in their applications.
💡 Research Summary
The paper addresses the challenge of deploying zero‑knowledge interactive proofs (ZKIPs) on highly constrained devices typical of the Internet of Things (IoT). While elliptic‑curve cryptography (ECC) is already recognized as a space‑ and computation‑efficient alternative to RSA, the authors observe that most existing ZKP constructions assume ample processing power and memory, making them unsuitable for low‑end microcontrollers and low‑power wireless radios. To bridge this gap, the authors take three well‑known discrete‑logarithm‑based ZKP protocols—the classic “coin‑flip” proof, Schnorr’s protocol, and a non‑interactive variant derived from Schnorr—and systematically translate each into the elliptic‑curve setting (ECDLP). This translation involves replacing modular exponentiation with scalar multiplication on an elliptic curve, adapting the group operations, and ensuring that the security properties (completeness, soundness, and zero‑knowledge) remain intact. The hash‑based challenge generation used in Schnorr’s protocol is retained, providing a provably random verifier challenge without extra communication.
Implementation is carried out on Wiselib, an open‑source, template‑based C++ library designed for portability across heterogeneous sensor platforms. The authors target two widely used low‑power hardware platforms: the Jennic JN5139 (32 MHz, 128 KB flash, 16 KB RAM) and the Texas Instruments MSP430 (16 MHz, 48 KB flash, 10 KB RAM), both equipped with IEEE 802.15.4 radios. The resulting code footprint for each protocol is roughly 8 KB, comfortably fitting within the limited flash of the devices. Message sizes range from 30 to 45 bytes, well below the 127‑byte payload limit of 802.15.4 frames, ensuring that the protocols can be transmitted without fragmentation.
Performance measurements show that a single round of the coin‑flip protocol executes in about 20 ms, while Schnorr’s one‑round protocol completes in roughly 10 ms; the non‑interactive variant requires only a single transmission and verification step, further reducing latency. Energy consumption per execution is measured between 0.5 mJ and 1.2 mJ, indicating that hundreds of authentications could be performed on a typical battery‑powered sensor node before the battery is exhausted. These figures demonstrate that the cryptographic overhead introduced by ZKIPs is modest enough to be practical in real‑world IoT deployments.
Beyond the raw performance data, the paper discusses three concrete application scenarios where privacy‑preserving authentication is critical: (1) smart‑home access control, where a user can prove possession of a credential without revealing the credential itself; (2) e‑voting, where voters can demonstrate eligibility and cast a vote without exposing their identity; and (3) attribute‑based credential systems, where devices can prove they satisfy certain policies (e.g., “temperature sensor in zone A”) without disclosing the exact sensor ID. In each case, the presented ECC‑based ZKIPs enable the required privacy guarantees while respecting the tight resource budgets of the devices involved.
The authors conclude that this work constitutes the first comprehensive implementation and empirical evaluation of ZKIP protocols on low‑end hardware, and they release the Wiselib modules as open source to encourage further adoption. Future research directions include extending the library to support multi‑party proofs, integrating post‑quantum secure primitives, and exploring hardware acceleration of elliptic‑curve operations to further lower latency and energy consumption. Overall, the paper convincingly shows that zero‑knowledge proofs, once thought too heavyweight for sensor‑level devices, can be efficiently realized using elliptic‑curve cryptography and careful protocol engineering.
Comments & Academic Discussion
Loading comments...
Leave a Comment