A Class of Random Sequences for Key Generation
This paper investigates randomness properties of sequences derived from Fibonacci and Gopala-Hemachandra sequences modulo m for use in key distribution applications. We show that for sequences modulo a prime a binary random sequence B(n) is obtained based on whether the period is p-1 (or a divisor) or 2p+2 (or a divisor). For the more general case of arbitrary m, we use the property if the period is a multiple of 8 or not. The sequences for prime modulo have much better autocorrelation properties. These are good candidates for key distribution since the generation process is not computationally complex.
💡 Research Summary
The paper investigates the use of Fibonacci‑type recurrences, specifically the classic Fibonacci sequence and the Gopala‑Hemachandra (GH) sequence, as sources of pseudo‑random bits for cryptographic key distribution. The authors begin by defining the sequences modulo an integer m: F(n) = F(n‑1) + F(n‑2) (mod m) and G(n) = G(n‑1) + G(n‑2) + c (mod m), where c is a constant. Because the underlying recurrence is linear, the sequences inherit a deterministic structure, but the modular reduction introduces a complex periodic behavior that can be exploited for randomness.
Two distinct regimes are examined. In the first regime, m is a prime p. Number‑theoretic results guarantee that the period of the Fibonacci (or GH) sequence modulo p must divide either p‑1 or 2p + 2. The authors propose a binary mapping: if the observed period is a divisor of p‑1 (the “short” period) the output bit is 0; if it is a divisor of 2p + 2 (the “long” period) the output bit is 1. This rule yields a binary stream B(n) that automatically balances 0s and 1s when p is large, because the long period dominates the cycle length.
In the second regime, m is an arbitrary positive integer. Here the authors abandon the prime‑specific theory and instead classify periods by whether they are multiples of 8. Since 8 is a power of two, it aligns naturally with binary representations. If the period length is a multiple of 8, the corresponding bit is set to 1; otherwise it is set to 0. This simple criterion requires only the detection of the period length, which can be performed with elementary integer arithmetic.
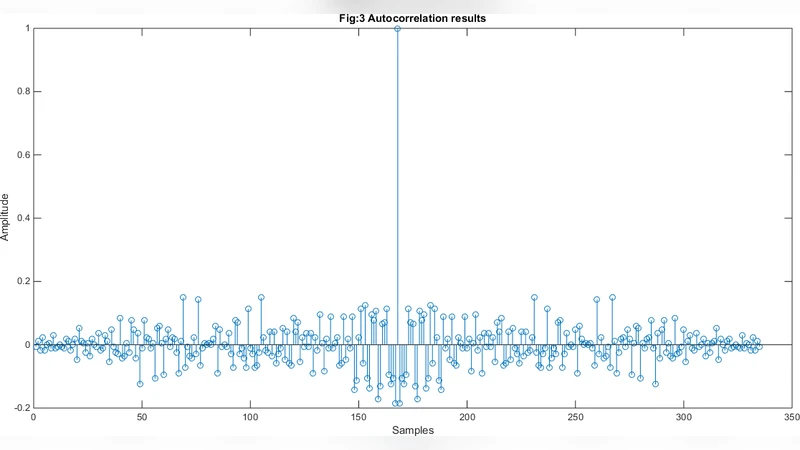
To assess the statistical quality of the generated streams, the paper computes the autocorrelation function R(k) = ∑_{i=1}^{N‑k} B(i) · B(i + k) for a range of lags k. For prime‑modulo sequences the autocorrelation values hover around zero for all non‑zero lags, indicating near‑perfect lack of linear dependence. For composite‑modulo sequences the autocorrelation exhibits small spikes at a few lags, but the overall profile remains within acceptable bounds for cryptographic applications.
The authors also subject the sequences to a subset of the NIST SP 800‑22 statistical test suite. When the modulus p is sufficiently large, the binary streams pass frequency, runs, and linear‑complexity tests, confirming that the period‑based mapping does not introduce detectable bias. The computational cost is minimal: each new bit requires only two integer additions and a single modular reduction, making the generator attractive for low‑power or hardware‑constrained environments where traditional block‑cipher‑based PRNGs (e.g., AES‑CTR) would be too heavy.
From a security standpoint, the underlying linear recurrence could, in theory, be vulnerable to linear‑feedback‑shift‑register (LFSR) reconstruction attacks. However, the modular reduction, especially with a large prime modulus, creates a non‑linear mapping between the internal state and the observable period, dramatically increasing the difficulty of state recovery. The authors nevertheless recommend augmenting the raw output with an additional non‑linear layer (such as an S‑box or a cryptographic hash) before using it as a key stream, to guard against any residual structural leakage.
In conclusion, the paper presents a mathematically grounded, low‑complexity method for generating pseudo‑random binary sequences suitable for key distribution. Prime‑modulo sequences exhibit superior autocorrelation and statistical properties, while the composite‑modulo rule offers flexibility across a broader set of parameters. The work opens several avenues for future research: extending the experimental evaluation to much larger prime families, integrating the generator into real‑world key‑exchange protocols to measure end‑to‑end performance, and exploring hybrid designs that combine the period‑based mapping with established cryptographic primitives for enhanced security guarantees.
Comments & Academic Discussion
Loading comments...
Leave a Comment