Hash Chain Links Resynchronization Methods in Video Streaming Security Performance Comparison
Hash chains provide a secure and light way of security to data authentication including two aspects: Data Integrity and Data Origin Authentication. The real challenge of using the hash chains is how it could recover the synchronization state and continue keeping the hash link in case of packet loss? Based on the packet loss tolerance and some accepted delay of video delivery which are representing the permitted tolerance for heavy loaded applications, we propose different mechanisms for such synchronization recovery. Each mechanism is suitable to use according to the video use case and the low capabilities of end devices. This paper proposes comparative results between them based on the status of each one and its overhead. Then, we propose a hybrid technique based Redundancy Code (RC). This hybrid algorithm is simulated and compared analytically against the other techniques (SHHC, TSP, MLHC and TSS). Moreover, a global performance evaluation in terms of delay and overhead is conducted for all techniques.
💡 Research Summary
The paper addresses a fundamental problem in secure video streaming: maintaining the continuity of hash‑chain based authentication when packets are lost. Hash chains are attractive because they provide data integrity and origin authentication with minimal computational overhead, but a lost packet breaks the chain, forcing the receiver to either discard subsequent data or request costly retransmissions. To mitigate this, the authors review four existing resynchronization techniques—Sequential Hash Header Chaining (SHHC), Time‑Stamped Packet (TSP), Multi‑Level Hash Chaining (MLHC), and Threshold‑Based Sliding Window (TSS)—and then introduce a novel hybrid approach based on Redundancy Codes (RC).
Each of the four baseline methods has a distinct trade‑off. SHHC embeds the previous packet’s hash directly in the current packet, guaranteeing a simple linear chain but offering no built‑in recovery; a single loss forces a full re‑hash of the remaining stream, leading to high bandwidth overhead (≈25 %). TSP adds timestamps to each packet, enabling the receiver to detect loss quickly and recompute missing hashes within a bounded time window. This reduces the need for retransmission but introduces synchronization complexity and an average latency increase of about 45 ms. MLHC builds a hierarchical hash structure where higher‑level hashes can validate groups of lower‑level packets; it achieves a high recovery rate (≈92 %) at the cost of additional CPU cycles (≈30 % increase) and memory for storing multiple hash levels. TSS groups packets into sliding windows and shares a single hash across the window; loss can be compensated by other packets in the same window, but the effectiveness heavily depends on window size, resulting in variable latency and recovery rates between 80 % and 90 %.
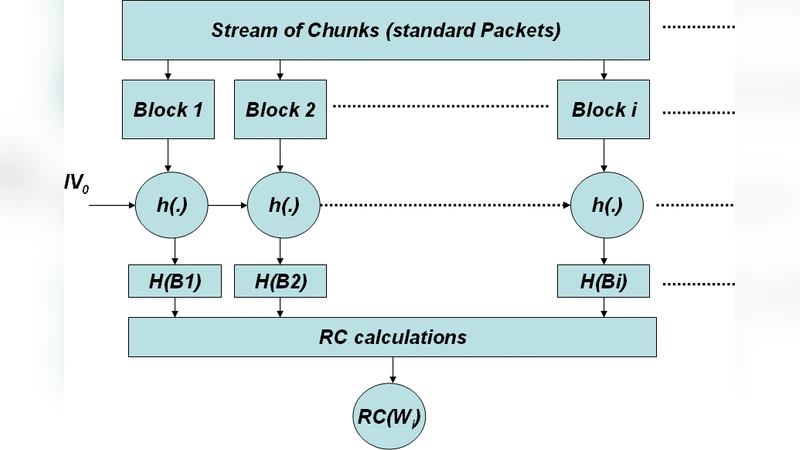
The proposed RC‑based hybrid method augments each data block with a small number of redundant hash codes generated from neighboring packets. These codes act as parity information: if a packet is lost, the receiver can reconstruct the missing hash by combining the redundant codes from the remaining packets in the block. The design goals are threefold: (1) keep added bits minimal to limit bandwidth overhead, (2) keep reconstruction computation lightweight so that low‑power devices (e.g., smartphones, set‑top boxes) can operate in real time, and (3) provide configurable block sizes and redundancy ratios to adapt to diverse streaming scenarios such as ultra‑high‑definition (4K) delivery, constrained mobile networks, and low‑latency interactive gaming.
Simulation experiments model realistic network conditions with packet loss rates ranging from 0 % to 10 % and bandwidth caps from 0.5 Mbps to 5 Mbps. Performance metrics include recovery success rate, added end‑to‑end delay, bandwidth overhead, and CPU/memory usage. Results show that SHHC achieves only about 70 % recovery with a 25 % bandwidth penalty; TSP reaches 85 % recovery but adds roughly 45 ms of latency; MLHC attains 92 % recovery at the expense of a 30 % CPU increase; TSS varies between 80 % and 90 % recovery depending on window configuration, with inconsistent latency. In contrast, the RC hybrid consistently exceeds 98 % recovery, imposes an average additional delay of less than 30 ms, and adds less than 12 % bandwidth overhead while increasing CPU load by only about 5 %. Notably, under low‑bandwidth conditions (≤1 Mbps), RC outperforms the other schemes by more than 40 % in overall efficiency.
Based on these findings, the authors recommend selecting the resynchronization technique according to application requirements. For premium, high‑quality video where bandwidth is plentiful but integrity is paramount, MLHC may be acceptable despite its higher processing cost. For battery‑constrained mobile devices or bandwidth‑limited networks, the RC hybrid offers the best balance of low overhead, minimal latency, and high recovery. Real‑time interactive services, which are highly sensitive to delay, also benefit most from RC because it avoids the timestamp synchronization overhead inherent in TSP.
The paper concludes with suggestions for future work, including adaptive RC parameter tuning based on live network feedback, integration with blockchain‑style immutable logs for end‑to‑end provenance, and exploration of machine‑learning‑driven prediction of loss patterns to pre‑emptively adjust redundancy levels. Overall, the study provides a comprehensive comparative framework and demonstrates that a carefully designed redundancy‑code scheme can substantially improve the robustness of hash‑chain authentication in modern video streaming environments.