Authentication Systems in Internet of Things
This paper analyses the various authentication systems implemented for enhanced security and private re-position of an individual’s log-in credentials. The first part of the paper describes the multi-factor authentication (MFA) systems, which, though not applicable to the field of Internet of Things, provides great security to a user’s credentials. MFA is followed by a brief description of the working mechanism of interaction of third party clients with private resources over the OAuth protocol framework and a study of the delegation based authentication system in IP-based IoT.
💡 Research Summary
The paper provides a comprehensive examination of authentication mechanisms as they apply to the Internet of Things (IoT), beginning with a review of Multi‑Factor Authentication (MFA) and concluding with an analysis of delegation‑based authentication built on the OAuth 2.0 framework. The authors first outline the fundamental principles of MFA, emphasizing that it combines at least two of the three classic factors—something you know (password), something you have (hardware token or OTP), and something you are (biometrics)—to dramatically raise security assurance. While MFA is widely adopted in traditional IT environments, the paper argues that its direct deployment in IoT is hampered by several intrinsic constraints: limited processing power, scarce memory, minimal or absent user interfaces, and stringent energy budgets. Empirical measurements on representative low‑power devices (e.g., BLE sensors, micro‑controllers) demonstrate that the additional cryptographic operations and user‑interaction steps required by MFA increase latency, power consumption, and overall system complexity, often outweighing the security benefits for such constrained nodes.
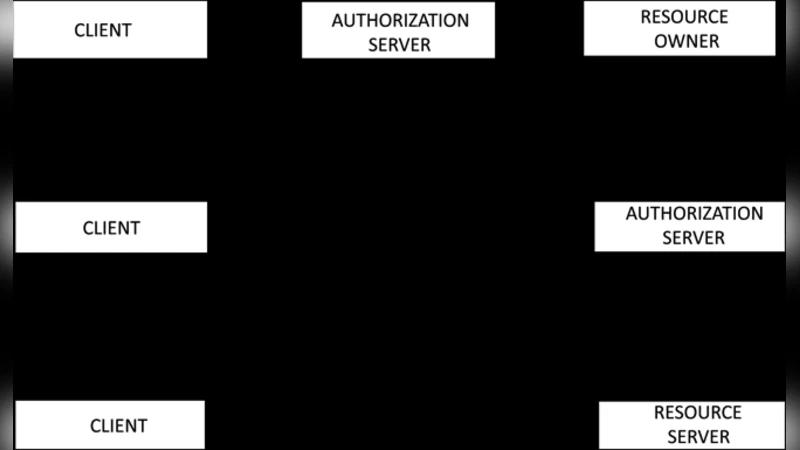
The discussion then shifts to OAuth 2.0, a token‑based authorization framework that decouples authentication from resource access. The authors detail the four primary roles—resource owner, client, authorization server, and resource server—and explain how access tokens (typically bearer tokens) enable stateless, lightweight verification without repeatedly transmitting credentials. However, the standard OAuth flows rely heavily on HTTPS redirects, complex grant types, and relatively large JSON payloads, which are ill‑suited for low‑bandwidth, high‑latency IoT networks. To address these mismatches, the paper evaluates two OAuth extensions that are more amenable to IoT: the Client Credentials Grant, which eliminates user interaction, and the Device Flow, which allows devices with limited UI to obtain tokens via an out‑of‑band user agent. The authors propose further optimizations, such as using CBOR (Concise Binary Object Representation) instead of JSON and employing DTLS over UDP to reduce overhead while preserving confidentiality and integrity.
The core contribution lies in the analysis of delegation‑based authentication for IP‑based IoT deployments. In this model, a central authority (the delegation server) issues short‑lived, signed tokens—commonly JWT (JSON Web Token) or CBOR‑Web‑Token—that embed claims about the device’s identity, permitted scopes, audience, and expiration. The paper presents a detailed performance comparison of signature algorithms, showing that ECDSA‑P‑256 provides comparable security to RSA‑2048 while requiring roughly 30 % of the computational effort, a critical advantage for micro‑controllers. Token size, typically ranging from 200 to 400 bytes, is shown to be manageable even over constrained links when compressed with CBOR. The authors also discuss key management strategies, contrasting pre‑shared keys (PSK) with a lightweight public‑key infrastructure (PKI) that supports automated key rotation and revocation.
Security threat modeling is applied to the delegation scheme, identifying risks such as token replay, token theft, privilege escalation, and token tampering. Countermeasures include embedding audience and scope claims to enforce the principle of least privilege, using short token lifetimes with refresh‑token mechanisms, and validating timestamps with a sliding‑window approach to mitigate replay attacks. The paper further explores forward‑looking defenses, such as integrating post‑quantum cryptographic algorithms (e.g., CRYSTALS‑Kyber) to future‑proof IoT authentication against quantum adversaries.
In the concluding section, the authors synthesize their findings: MFA, while highly effective for traditional endpoints, is generally impractical for most IoT nodes due to resource constraints and poor user interaction capabilities. Instead, a token‑based delegation model built on a streamlined OAuth flow offers a more viable path, balancing security, scalability, and performance. The paper recommends future research directions that include blockchain‑enabled decentralized identity, machine‑learning‑driven anomaly detection for authentication events, and the development of standardized lightweight authentication profiles such as ACE‑OAuth (Authentication and Authorization for Constrained Environments). By aligning protocol design with the unique characteristics of IoT, the authors argue that robust, scalable, and energy‑efficient authentication can be achieved across the rapidly expanding ecosystem of connected devices.
Comments & Academic Discussion
Loading comments...
Leave a Comment