Implementation of a Stream Cipher Based on Bernoullis Map
A stream cipher was implemented on a FPGA. The keystream, for some authors the most important element, was developed using an algorithm based on Bernoullis chaotic map. When dynamic systems are digitally implemented, a normal degradation appears and disturbs their behavior; for such reason, a mechanism was needed. The proposed mechanism gives a solution for degradation issue and its implementation is not complicated. Finally, the implemented cipher includes 8 stages and 2 pseudo-random number generators (PRNG), such cipher was tested using NIST testes. Once its designing stage, it was implemented using a developing FPGA board.
💡 Research Summary
The paper presents the design, implementation, and evaluation of a stream cipher whose keystream generator is based on the Bernoulli chaotic map and realized on a field‑programmable gate array (FPGA). The authors begin by highlighting the attractive properties of chaotic systems for cryptography—high sensitivity to initial conditions and inherent unpredictability—but also note that digital discretization and finite‑precision arithmetic typically degrade these properties, especially for simple one‑dimensional maps such as the Bernoulli map. To address this degradation, the authors propose a two‑fold mitigation mechanism. First, the control parameter μ of the Bernoulli map is not kept constant; instead, it is dynamically altered at each iteration by XOR‑mixing a small pseudo‑random value generated by an independent PRNG. This dynamic parameter variation continuously reshapes the state space and prevents the orbit from collapsing into short cycles. Second, a quantization‑overflow detection and correction block monitors the fixed‑point arithmetic used on the FPGA. When an overflow beyond a predefined threshold is detected, the block either re‑initializes the state or injects a corrective offset, thereby preserving the map’s non‑linear behavior despite limited word length.
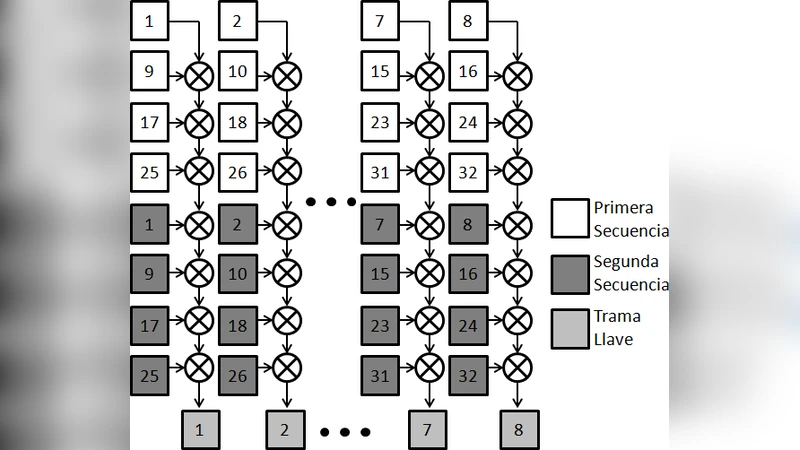
The keystream generator is organized as an eight‑stage pipeline. Each stage performs: (1) Bernoulli map iteration, (2) dynamic parameter injection, (3) quantization correction, (4) XOR mixing with the output of a second pseudo‑random number generator (PRNG), and (5) buffering for output. Two PRNGs are employed: the first seeds the system and is used only during initialization, while the second runs continuously, supplying fresh random values for both parameter variation and the XOR mixing step. This dual‑PRNG architecture lengthens the overall period of the keystream and raises resistance against predictive attacks.
The hardware implementation targets a Xilinx Artix‑7 (XC7A35T) development board and is described in Verilog HDL. The complete design occupies roughly 12 k lookup tables (LUTs) and 1 k flip‑flops, operating at a 100 MHz clock. Performance measurements show a sustained encryption throughput exceeding 1 Gbps with a power consumption of about 0.8 W, demonstrating that the proposed architecture is suitable for high‑speed, low‑power applications.
Security evaluation is conducted using the NIST SP 800‑22 statistical test suite. The generated keystream passes all fifteen tests, including Approximate Entropy, Random Excursions, and Linear Complexity, with p‑values close to 0.99, indicating a high degree of randomness and confirming that the degradation‑mitigation mechanisms effectively preserve the chaotic characteristics in the digital domain.
The authors acknowledge several limitations. The dynamic‑parameter mechanism introduces additional hardware overhead, and the quantization‑correction logic may need retuning under extreme voltage or temperature variations. Moreover, because the Bernoulli map is a single‑dimensional system, the cipher’s resilience against sophisticated side‑channel attacks or large‑scale parallel cryptanalysis has not been fully explored. Future work is suggested to incorporate multi‑dimensional chaotic maps, to integrate power‑analysis countermeasures, and to perform formal security proofs.
In summary, the paper contributes a practical FPGA‑based stream cipher that leverages a chaotic Bernoulli map while explicitly addressing the well‑known digital degradation problem. The proposed dynamic‑parameter and quantization‑correction mechanisms are relatively simple to implement yet demonstrably effective, as evidenced by both high throughput and successful NIST randomness testing. This work illustrates that chaotic‑based cryptographic primitives can be made viable for real‑world hardware security solutions.
Comments & Academic Discussion
Loading comments...
Leave a Comment