Managing key multicasting through orthogonal systems
In this paper we propose a new protocol to manage multicast key distribution. The protocol is based on the use of orthogonal systems in vector spaces. The main advantage in comparison to other existing multicast key management protocols is that the length and the number of the messages which have to be sent are considerably smaller. This makes the protocol especially attractive when the number of legitimate receivers is large.
💡 Research Summary
The paper introduces a novel multicast key management protocol that leverages orthogonal systems in vector spaces to dramatically reduce communication overhead and computational cost. In the initialization phase a finite field K and an m‑dimensional K‑vector space V (with m ≥ n, where n is the number of users) are chosen. A non‑degenerate symmetric bilinear form ⟨·,·⟩ is defined, and a set B = {e₁,…,eₙ} of mutually orthogonal vectors with non‑zero self‑inner products is generated and kept secret by the server. Each user i receives a random non‑zero scalar xᵢ∈K and the private vector vᵢ = xᵢeᵢ; the collection B′ = {v₁,…,vₙ} is also secret.
When a new session key s∈K must be distributed, the server computes
c = s·( Σ_{v∈B′₁} v + y·Σ_{v∈B′₂} v ),
where B′₁ contains vectors of currently authorized users, B′₂ contains vectors of “placeholder” slots, and y∈K is a fresh random scalar. The server broadcasts the single value c to the whole group. Each user i computes h = ⟨c, vᵢ⟩ = s·⟨vᵢ, vᵢ⟩ and recovers the secret by s = h·⟨vᵢ, vᵢ⟩⁻¹. Thus a single multicast message suffices for all members.
Join and leave operations are handled similarly. On a join, the server assigns the newcomer a previously unused vector from B′₂₁, selects a new session key s′ and a new random y′, and broadcasts the updated c′. On a leave, the departing user’s vector is removed from B′₁, a fresh vector from B′₂₂ replaces it, and a new c′ is sent. Consequently, each rekeying requires only one broadcast per group, regardless of group size.
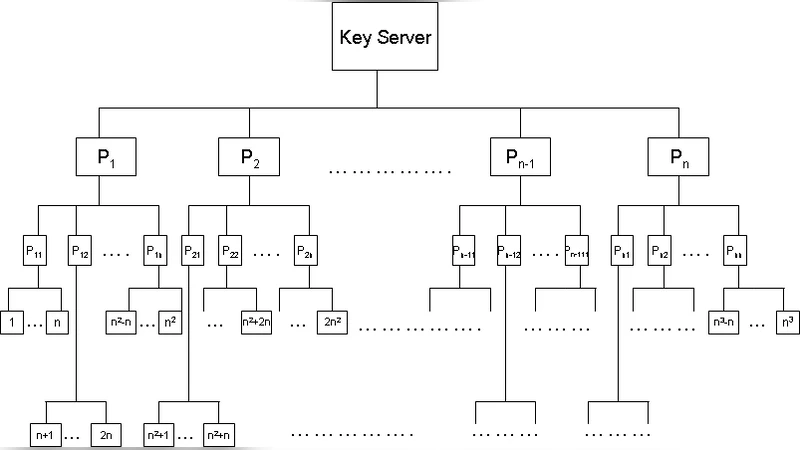
The authors also describe how multiple groups can be managed by allocating distinct orthogonal bases to each group, and they illustrate a hierarchical tree deployment where intermediate nodes store shared vectors. In a tree of depth 4 and branching factor n, the protocol can support n³ leaf users while keeping rekey messages as short as n·k bits (k being the bit‑length of the scalar). For n = 100, three short messages suffice to handle a million users, and the server’s computation time does not depend on the total number of users.
Security analysis rests on counting arguments: for a vector space V = 𝔽_q^m with m > 2n, the number of n‑tuples of mutually orthogonal vectors with non‑zero self‑inner product is at least (1 + o(1))·q^{3/2 n}·(2n)!⁻¹. This makes exhaustive search for the secret basis infeasible. The paper also argues that collusion attacks are mitigated because even if k users collude, the remaining dimension m − k > 2(n − k) still guarantees a large pool of orthogonal vectors. However, if the secret basis B or any vector of B′ becomes known, an attacker can solve for the scalars xᵢ and the session key directly, so the secrecy of the basis is critical.
Practical considerations include choosing a large enough field (e.g., GF(2^{128})) and a dimension m (e.g., 256) to balance security and storage. Each user stores a single m‑dimensional vector and performs one inner product per rekey, which is computationally cheap. The protocol’s simplicity eliminates the logarithmic message growth of tree‑based schemes and the heavy integer or polynomial arithmetic of Secure‑Lock‑type schemes.
Nevertheless, the paper lacks concrete performance measurements, detailed guidelines for initializing and refreshing the secret basis, and an analysis of the impact of frequent dynamic membership changes on the management of B′₂₁ and B′₂₂. Future work should address these implementation issues, provide empirical benchmarks, and explore integration with existing multicast transport protocols. Overall, the orthogonal‑system approach offers a promising direction for scalable, low‑overhead multicast key distribution.
Comments & Academic Discussion
Loading comments...
Leave a Comment