A Tutorial on Network Security: Attacks and Controls
With the phenomenal growth in the Internet, network security has become an integral part of computer and information security. In order to come up with measures that make networks more secure, it is important to learn about the vulnerabilities that could exist in a computer network and then have an understanding of the typical attacks that have been carried out in such networks. The first half of this paper will expose the readers to the classical network attacks that have exploited the typical vulnerabilities of computer networks in the past and solutions that have been adopted since then to prevent or reduce the chances of some of these attacks. The second half of the paper will expose the readers to the different network security controls including the network architecture, protocols, standards and software/ hardware tools that have been adopted in modern day computer networks.
💡 Research Summary
The paper “A Tutorial on Network Security: Attacks and Controls” offers a comprehensive, two‑part overview of the evolution of network security, beginning with classic vulnerabilities and attacks and concluding with modern defensive architectures, protocols, standards, and tools.
Part 1 – Classical Network Attacks
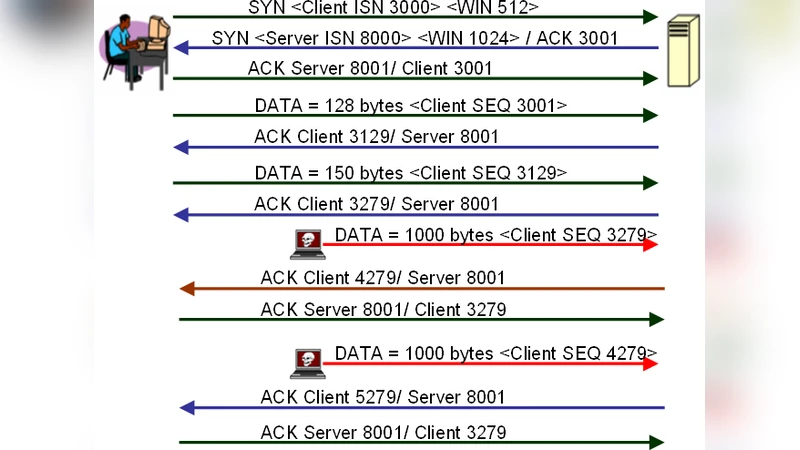
The authors first catalog the most common attack vectors that have historically exploited weaknesses in the OSI model. At the physical layer, they discuss cable tapping and electromagnetic eavesdropping. The data‑link layer is dominated by ARP spoofing, MAC flooding, and VLAN hopping. Network‑layer threats include IP address spoofing, routing protocol manipulation (e.g., BGP hijacking, OSPF falsification), and ICMP‑based attacks. The transport layer section covers TCP session hijacking, SYN‑flooding, and UDP‑based amplification attacks, while the application layer examines HTTP parameter tampering, DNS cache poisoning, SQL injection, and cross‑site scripting. For each attack, the paper identifies the underlying vulnerability (such as default passwords, unpatched firmware, lack of packet filtering), the typical tools used (Wireshark, Nmap, Metasploit, Scapy), and the impact on confidentiality, integrity, or availability.
Early Countermeasures
The tutorial then surveys the first generation of defenses that were introduced in response to these threats. Packet‑filtering firewalls and stateful inspection firewalls are explained in terms of ACL design and connection‑state tracking. Intrusion Detection and Prevention Systems (IDS/IPS) are broken down into signature‑based and anomaly‑based approaches, with emphasis on network‑based IDS for sniffing detection and host‑based IDS for file‑integrity monitoring. Virtual Private Networks (VPNs) using IPsec, PPTP, and L2TP are presented as tunnel‑based confidentiality solutions, while SSL/TLS is introduced as a transport‑layer encryption mechanism. The authors also cover link‑layer hardening techniques such as port security, DHCP snooping, and Dynamic ARP Inspection, which mitigate many layer‑2 attacks.
Part 2 – Modern Network Security Controls
The second half of the paper shifts focus to contemporary security controls that reflect today’s highly virtualized, cloud‑centric networks. The authors advocate a Defense‑in‑Depth strategy combined with a Zero‑Trust model, arguing that trust should never be assumed based on network location. Network segmentation is achieved through VLANs, sub‑nets, and software‑defined networking (SDN) policies that allow dynamic, centrally managed flow control. Network Functions Virtualization (NFV) enables flexible deployment of firewalls, IDS/IPS, and load balancers as virtual appliances.
Transport‑Layer Advances
TLS 1.3 is highlighted for its reduced handshake round‑trips and mandatory forward secrecy, which dramatically lowers the risk of man‑in‑the‑middle attacks. The paper also discusses QUIC, a UDP‑based protocol that integrates TLS‑like encryption at the application layer, providing resistance to traditional TCP‑based attacks. DNS security is addressed through DNSSEC, DNS‑over‑HTTPS (DoH), and DNS‑over‑TLS (DoT), which protect against cache poisoning and eavesdropping.
Standards and Governance
The tutorial references key IETF RFCs (e.g., RFC 4301 for IPsec, RFC 7525 for TLS security recommendations) and ISO/IEC 27033 series as the normative basis for designing secure networks. It outlines a risk‑assessment workflow, policy development, and the three‑pillars of authentication, authorization, and auditing (AAA).
Hardware and Cloud‑Based Enhancements
Hardware Security Modules (HSMs) and Trusted Platform Modules (TPMs) are described as essential for secure key storage and boot‑time integrity verification. Modern network devices equipped with cryptographic accelerators (NPUs, ASICs) enable line‑rate encryption without prohibitive CPU overhead. In cloud environments, the paper recommends leveraging native security services such as AWS GuardDuty, Azure Sentinel, and Google Chronicle for threat intelligence, automated incident response, and continuous compliance monitoring.
Trade‑offs and Implementation Guidance
Finally, the authors discuss the practical trade‑offs between security, performance, cost, and operational complexity. Full‑packet encryption provides strong confidentiality but can increase latency and require hardware upgrades. Advanced firewalls and IDS/IPS improve detection accuracy but add management overhead and potential false‑positive fatigue. The paper concludes that organizations must align their security controls with business risk tolerance, regulatory requirements, and available resources, adopting a layered, adaptable approach that can evolve as new threats emerge.
Comments & Academic Discussion
Loading comments...
Leave a Comment