Hasq Hash Chains
This paper describes a particular hash-based records linking chain scheme. This scheme is simple conceptually and easy to implement in software. It allows for a simple and secure way to transfer ownership of digital objects between peers.
💡 Research Summary
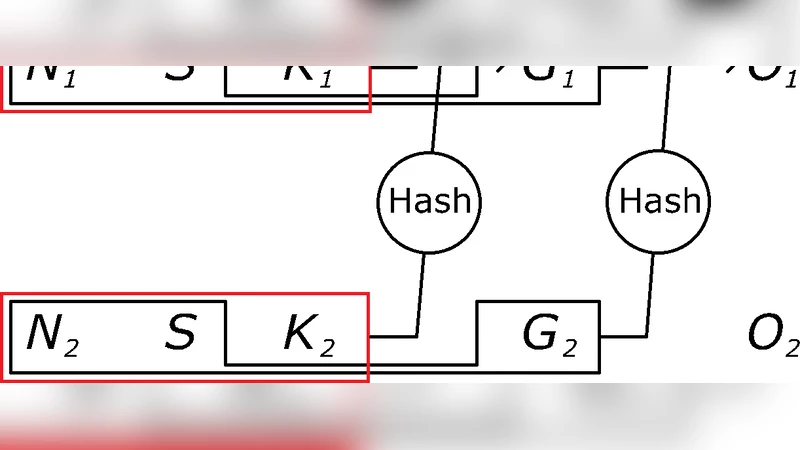
The paper introduces Hasq Hash Chains, a lightweight, hash‑based linking scheme designed to transfer ownership of digital objects between peers without the heavy overhead of traditional blockchains. Each record in the chain consists of five fields: H (the hash of the previous record), S (the current owner’s identifier, typically a hash of a public key), K (a unique key for the record), N (a sequential number), and G (the hash of the current record). The G value is computed as SHA‑256(H || S || K || N || D), where D is the hash of the underlying digital asset. By chaining each record to the hash of its predecessor, any attempt to modify a record would require recomputing the entire chain, providing strong integrity guarantees.
Ownership transfer is achieved by appending a new record: the sender’s secret key signs a transaction, the receiver’s public‑key hash becomes the new S, and the new record’s H field is set to the G value of the previous record. No consensus protocol is required; peers simply verify that the new G matches the recomputed hash and that the S field corresponds to the intended recipient. This simplicity yields very low computational cost—only a single SHA‑256 operation per record—and minimal storage, making the system suitable for environments with constrained resources.
The authors discuss security considerations. Because the scheme relies on the collision resistance of SHA‑256, the probability of a successful hash collision is negligible. However, the absence of a centralized validator opens the possibility of malicious peers broadcasting counterfeit chains. To mitigate this, the paper recommends pre‑sharing a trusted genesis record and performing multi‑path verification to ensure that all participants converge on the same root. Additionally, simultaneous record creation can cause forks; the authors propose simple fork‑resolution rules such as “longest chain wins” or “most recent chain wins,” optionally supplemented by lightweight voting if needed.
Performance experiments implemented in Python demonstrate the ability to generate and verify thousands of records per second, with storage requirements an order of magnitude lower than typical blockchain solutions. The system can be extended with optional metadata—timestamps, digital signatures, or additional payloads—at the cost of increased bandwidth and storage, allowing developers to balance transparency against efficiency.
Potential applications highlighted include IoT device authentication, digital content licensing, and electronic certificate issuance, where high integrity is required but full blockchain infrastructure is impractical. The paper concludes that Hasq Hash Chains provide a practical, secure, and scalable foundation for peer‑to‑peer digital ownership transfer, and suggests future work on standardizing the protocol, integrating post‑quantum hash functions, and exploring hybrid models that combine Hasq’s lightweight linking with selective consensus mechanisms for added robustness.
Comments & Academic Discussion
Loading comments...
Leave a Comment