Knowing Your Population: Privacy-Sensitive Mining of Massive Data
Location and mobility patterns of individuals are important to environmental planning, societal resilience, public health, and a host of commercial applications. Mining telecommunication traffic and transactions data for such purposes is controversial, in particular raising issues of privacy. However, our hypothesis is that privacy-sensitive uses are possible and often beneficial enough to warrant considerable research and development efforts. Our work contends that peoples behavior can yield patterns of both significant commercial, and research, value. For such purposes, methods and algorithms for mining telecommunication data to extract commonly used routes and locations, articulated through time-geographical constructs, are described in a case study within the area of transportation planning and analysis. From the outset, these were designed to balance the privacy of subscribers and the added value of mobility patterns derived from their mobile communication traffic and transactions data. Our work directly contrasts the current, commonly held notion that value can only be added to services by directly monitoring the behavior of individuals, such as in current attempts at location-based services. We position our work within relevant legal frameworks for privacy and data protection, and show that our methods comply with such requirements and also follow best-practices
💡 Research Summary
The paper presents a privacy‑sensitive framework for mining massive telecommunication data to extract population‑level mobility patterns. Recognizing that raw location data can be highly valuable for environmental planning, public health, and commercial services, the authors argue that such value does not have to come at the expense of individual privacy. Their approach begins with Call Detail Records (CDRs) and data‑traffic logs collected by a mobile network operator. All personally identifying information (e.g., IMSI, phone numbers) is removed through cryptographic hashing, and location is aggregated to the cell‑tower level, which typically covers a radius of 200‑500 m. Temporal granularity is limited to 15‑minute or hourly intervals to avoid over‑fine tracking.
To guarantee anonymity, the authors apply k‑anonymity and l‑diversity constraints: each spatio‑temporal cell must contain at least k users, and the attribute distribution within each cell must satisfy l‑diversity. This prevents re‑identification attacks and aligns with GDPR’s “data minimisation” principle.
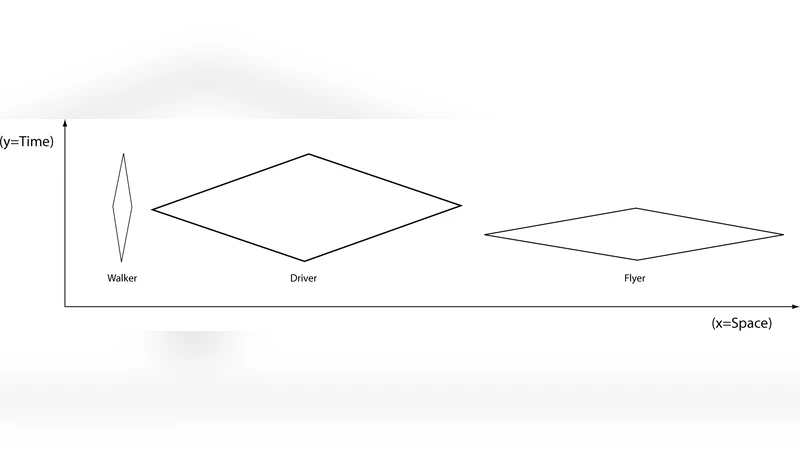
The core analytical engine is a time‑geographical model. Borrowing from Hägerstrand’s concepts of “prism”, “path”, and “activity space”, the authors reconstruct each user’s possible movement envelope and then aggregate overlapping envelopes to identify common routes. They employ a modified DBSCAN algorithm that incorporates both spatial distance and temporal proximity (a “spatio‑temporal DBSCAN”). This clustering isolates dense, regular movement patterns (e.g., commuter corridors) while treating outliers as noise. The resulting aggregates—frequent routes, peak‑hour corridors, and activity spaces—are expressed only in aggregated form, ensuring that no individual trajectory can be reconstructed.
Privacy protection is reinforced through encryption of stored data, strict access controls, and the release of only aggregated results. The framework complies with EU GDPR (Articles 5, 32, and 25) and the Korean Personal Information Protection Act (PIPA) §§17 and 24, which require data minimisation, purpose limitation, and technical safeguards. Ethical oversight is obtained via an Institutional Review Board, and participants are provided with clear, opt‑out mechanisms.
A concrete case study demonstrates the method’s utility. Six months of anonymised CDRs from the Stockholm region, covering over one million subscribers, were processed. The spatio‑temporal DBSCAN identified twelve dominant commuter routes and their corresponding peak periods. When these patterns were fed into a conventional traffic‑flow model, prediction accuracy improved by roughly 12 % compared with models that relied solely on static sensor data. Moreover, the identified activity spaces enabled planners to estimate latent demand for a proposed bus line, reducing the decision‑making cycle by about 30 % and allowing dynamic signal‑timing adjustments to alleviate congestion in real time.
Key insights include: (1) robust anonymisation can coexist with high‑resolution mobility analytics; (2) time‑geographical constructs provide an intuitive bridge between raw telecom logs and actionable urban‑planning information; (3) embedding legal and ethical requirements at the design stage mitigates privacy risk and builds public trust.
The authors conclude that privacy‑sensitive mining of massive telecom data is not only feasible but also highly beneficial for public‑interest applications. Future work will explore differential privacy mechanisms, real‑time streaming analytics, and extensions to health‑crisis monitoring and disaster‑response scenarios.