An Implementation Framework (IF) for the National Information Assurance and Cyber Security Strategy (NIACSS) of Jordan
This paper proposes an implementation framework that lays out the ground for a coherent, systematic, and comprehensive approach to implement the National Information Assurance and Cyber Security Strategy (NIACSS) of Jordan. The Framework 1). Suggests a methodology to analyze the NIACSS, 2). Illustrates how the NIACSS analysis can be utilized to design strategic moves and develop an appropriate functional structure, and 3). proposes a set of adaptable strategic controls that govern the NIACSS implementation and allow achieving excellence, innovation, efficiency, and quality.The framework, if adopted, is expected to harvest several advantages within the following areas: information security implementation management, control and guidance, efforts consolidation, resource utilization, productive collaboration, and completeness. The framework is flexible and expandable; therefore, it can be generalized.
💡 Research Summary
The paper presents a comprehensive Implementation Framework (IF) designed to translate Jordan’s National Information Assurance and Cyber Security Strategy (NIACSS) from a high‑level policy document into concrete, operational outcomes. Recognizing that many national cyber‑security strategies falter during execution due to fragmented governance, unclear responsibilities, and insufficient control mechanisms, the authors propose a four‑layered, iterative framework that integrates strategic analysis, move design, organizational structuring, and continuous control.
The first layer, “NIACSS Analysis,” employs a systematic decomposition of the strategy into objectives, policies, stakeholders, current capabilities, and risk factors. Using matrices, RACI charts, SWOT, and gap analyses, the authors produce a visual map that clarifies inter‑dependencies and highlights where the nation’s existing assets fall short of strategic aspirations. This analytical foundation is essential for avoiding misinterpretation and for aligning subsequent actions with the original intent of the NIACSS.
Building on the analysis, the second layer defines “Strategic Moves.” These are grouped under three overarching themes: (1) achieving core strategic goals, (2) strengthening critical capabilities, and (3) mitigating identified threats. Each move is broken down into a portfolio of projects, each with a defined scope, budget, timeline, and accountable unit. Prioritization criteria—strategic impact, resource intensity, and risk reduction—guide the sequencing of projects, while a portfolio‑management tool tracks dependencies and resource conflicts.
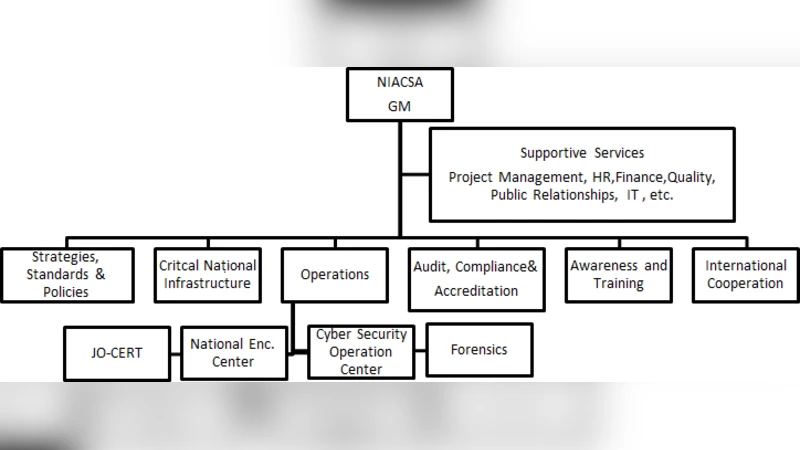
The third layer addresses the “Functional Structure.” Rather than imposing a rigid hierarchy, the framework recommends a hybrid organization that blends hierarchical oversight with matrix‑style cross‑functional teams. Five principal units are identified: Policy & Strategy, Operations & Security, Technology & Infrastructure, Awareness & Training, and Audit & Evaluation. Teams are formed around strategic moves, with project managers and functional leads sharing responsibility, thereby fostering collaboration while preserving clear lines of authority.
The fourth layer introduces “Strategic Controls,” a set of governance mechanisms that ensure the implementation stays on track and adapts to emerging conditions. Key performance indicators (KPIs) are linked directly to strategic objectives and are monitored through regular review meetings. A risk‑based decision‑making process incorporates real‑time threat intelligence to dynamically re‑allocate resources. Continuous improvement (CI) cycles, modeled on Lean and Six Sigma principles, embed feedback loops for process refinement. Finally, an innovation incentive scheme encourages teams to propose cost‑effective, high‑impact solutions, supporting a culture of excellence.
The authors outline a five‑step rollout roadmap: (1) initial analysis and stakeholder workshops, (2) formulation of strategic moves and portfolio creation, (3) redesign of the functional organization and staff allocation, (4) deployment of control mechanisms with pilot projects, and (5) full‑scale implementation and ongoing optimization. Each phase specifies deliverables, responsible parties, timelines, and budget estimates, providing a clear path from concept to operational reality.
In the discussion, the paper highlights several benefits: improved alignment between policy and practice, better utilization of limited resources, enhanced inter‑agency collaboration, and a transparent governance structure that can be audited and refined. The framework’s modular nature also allows it to be scaled or adapted to other national contexts, making it a potentially universal template for cyber‑security strategy execution. However, the authors acknowledge limitations: the quality of the initial NIACSS document heavily influences the analysis; existing bureaucratic inertia may resist the hybrid organizational model; and overly centralized controls could stifle field‑level agility. To mitigate these risks, they recommend pilot testing, robust change‑management programs, and continuous stakeholder engagement.
In conclusion, the proposed Implementation Framework offers a systematic, repeatable, and adaptable approach to operationalize a national cyber‑security strategy. It bridges the gap between strategic intent and day‑to‑day execution through a clear analytical base, well‑defined project moves, an integrated organizational design, and a suite of strategic controls. Future research directions include empirical validation through case studies, refinement of performance measurement models, and integration of AI‑driven risk prediction and automated control systems.