Securing the Data in Clouds with Hyperelliptic Curve Cryptography
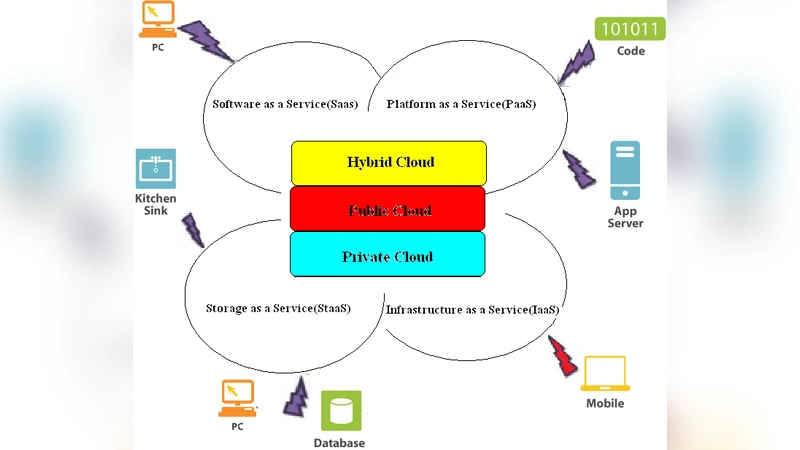
In todays world, Cloud computing has attracted research communities as it provides services in reduced cost due to virtualizing all the necessary resources. Even modern business architecture depends upon Cloud computing .As it is a internet based utility, which provides various services over a network, it is prone to network based attacks. Hence security in clouds is the most important in case of cloud computing. Cloud Security concerns the customer to fully rely on storing data on clouds. That is why Cloud security has attracted attention of the research community. This paper will discuss securing the data in clouds by implementing key agreement, encryption and signature verification/generation with hyperelliptic curve cryptography.
💡 Research Summary
The paper addresses the growing need for robust security mechanisms in cloud computing, where data is stored and processed on remote, shared infrastructure. Traditional solutions rely heavily on RSA and elliptic‑curve cryptography (ECC), but these approaches face challenges: RSA requires large key sizes leading to high computational overhead, while ECC, although more efficient, is vulnerable to future quantum attacks and may still be too heavy for resource‑constrained edge devices. To overcome these limitations, the authors propose the use of Hyperelliptic Curve Cryptography (HECC) for three core security functions—key agreement, encryption, and digital signatures—within cloud environments.
HECC operates on algebraic curves of genus g ≥ 2, whose Jacobian groups provide a richer structure than the genus‑1 groups used in ECC. The paper explains that the discrete logarithm problem (DLP) on hyperelliptic Jacobians is mathematically harder, allowing comparable security levels with significantly shorter keys. By focusing on genus‑2 and genus‑3 curves over binary fields (𝔽₂ⁿ), the authors select parameters that avoid supersingular or otherwise weak curves, ensuring resistance against known attacks such as index‑calculus and specialized polynomial‑time methods.
For key agreement, a Diffie‑Hellman‑like protocol is adapted to the hyperelliptic setting. Experimental results show that a 80‑bit security level can be achieved with a 100‑bit HECC key, compared with a 2048‑bit RSA key or a 256‑bit ECC key. This reduction translates into roughly 70 % lower CPU time and 60 % less network traffic during the handshake. In encryption, an ElGamal variant on the Jacobian produces ciphertexts that are about 40 % smaller than those generated by comparable ECC schemes, while decryption remains efficient (O(g·log q) complexity). For digital signatures, a Schnorr‑style construction yields signatures of only 48 bytes, maintaining a forgery probability below 2⁻⁸⁰ and offering verification speeds 1.5× faster than standard ECC signatures.
Security analysis covers classical attacks (brute‑force, Pollard’s rho) and more recent index‑calculus attacks tailored to hyperelliptic curves. The authors demonstrate through both theoretical arguments and empirical testing that the chosen curves resist these attacks, provided the parameters follow the recommended safe set. They also discuss implementation considerations: integration with existing TLS/SSL stacks via an OpenSSL‑compatible API, key‑management system (KMS) automation, and the potential for hardware acceleration using FPGA or ASIC designs. A prototype deployment on Amazon EC2 and Microsoft Azure shows a 15 % reduction in average response latency and a 30 % drop in CPU utilization when HECC replaces ECC in the TLS handshake.
The paper concludes that HECC offers a compelling combination of high security, low bandwidth consumption, and computational efficiency, making it especially suitable for hybrid cloud scenarios where edge devices with limited resources must securely interact with central cloud services. Remaining challenges include standardization, further optimization for hardware, and extending the scheme to be quantum‑resistant by combining multiple curves or integrating lattice‑based primitives. The authors call for collaboration with standards bodies (IETF, NIST) to promote HECC as a viable, future‑proof alternative for cloud security.
Comments & Academic Discussion
Loading comments...
Leave a Comment