A Pair-wise Key Distribution Mechanism and Distributed Trust Evaluation Model for Secure Data Aggregation in Mobile Sensor Networks
We propose a secure data aggregation (SDA) framework for mobile sensor networks whose topology changes dynamically with time. The SDA framework (designed to be resilient to both insider and outsider attacks) comprises of a pair-wise key establishment mechanism run along the edges of a data gathering tree and a distributed trust evaluation model that is tightly integrated with the data aggregation process itself. If an aggregator node already shares a secret key with its child node, the two nodes locally coordinate to refresh and establish a new pair-wise secret key; otherwise, the aggregator node requests the sink to send a seed-secret key message that is used as the basis to establish a new pair-wise secret key. The trust evaluation model uses the two-sided Grubbs test to identify outlier data in the periodic beacons collected from the child nodes (neighbor) nodes. Once the estimated trust score for a neighbor node falls below a threshold, the sensor node locally classifies its neighbor node as a Compromised or Faulty (CF) node, and discards the data or aggregated data received from the CF node. This way, the erroneous data generated by the CF nodes could be filtered at various levels of the data gathering tree and are prevented from reaching the root node (sink node). Finally, we assess the effectiveness of our trust evaluation model through a comprehensive simulation study.
💡 Research Summary
The paper presents a comprehensive secure data aggregation (SDA) framework tailored for mobile sensor networks (MSNs) whose topology changes continuously due to node mobility. The framework consists of two tightly coupled components: a pair‑wise key establishment protocol that operates on the edges of the data‑gathering tree, and a distributed trust evaluation model that uses statistical outlier detection to filter compromised or faulty (CF) nodes.
Pair‑wise key distribution
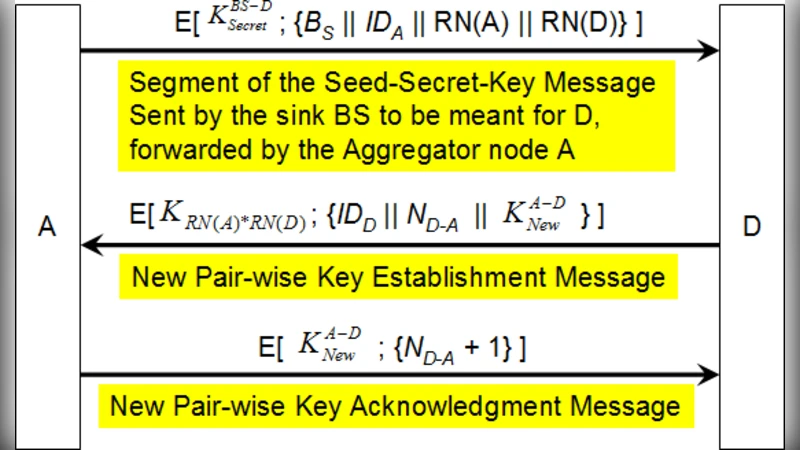
Each parent‑child link in the aggregation tree either already shares a secret key or must obtain one from the sink (the network’s base station). If a shared key exists, the two nodes locally refresh it by hashing the old key together with a fresh nonce, producing a new key with negligible communication overhead. When no key exists, the parent sends a request to the sink; the sink generates a seed‑secret key by hashing a random seed with a pre‑installed master key and returns it encrypted to the parent. The parent then combines this seed with its own identifier to derive the final pair‑wise key. This design ensures that key establishment scales with node movement: whenever the tree is re‑configured due to mobility, only the newly created edges trigger the lightweight request‑reply sequence, while existing edges simply refresh their keys. Consequently, the number of key exchanges and the associated energy consumption are dramatically reduced compared with traditional pre‑distribution schemes that require full re‑keying after each topology change.
Distributed trust evaluation
Every node periodically receives beacons containing sensor readings from its children. The node aggregates these readings into a sample set and applies the two‑sided Grubbs test, a statistical method that identifies a single outlier in a normally distributed dataset. The test computes the maximum deviation from the sample mean, normalizes it by the sample standard deviation, and compares the result to a critical value determined by a chosen significance level (α). If the test flags a reading as an outlier, the node reduces the trust score of the corresponding child by a factor β; conversely, consecutive normal readings increase the score by a recovery factor γ, bounded by a maximum of 1.0. When a child’s trust score falls below a predefined threshold τ, the parent classifies the child as a CF node and discards any further raw or aggregated data it provides. Because this evaluation occurs independently at each level of the aggregation tree, malicious data are filtered out early and never reach the sink.
Integration and workflow
The SDA process proceeds as follows: (1) during tree construction, pair‑wise keys are established; (2) at each aggregation round, parents decrypt incoming beacons, run the Grubbs test, update trust scores, and filter out data from CF nodes; (3) the remaining legitimate data are aggregated (e.g., averaged or summed) and forwarded upward; (4) periodically, or when the tree changes, keys are refreshed using the lightweight protocol described above. This tight coupling eliminates the need for separate security modules, keeping the computational and communication overhead low—critical for resource‑constrained sensor nodes.
Simulation methodology
The authors implemented the framework in NS‑3, simulating 100 nodes deployed over a 500 m × 500 m area. Node mobility followed Random Waypoint and Gauss‑Markov models to reflect realistic movement patterns. Beacon intervals were set to 5 seconds, and aggregation cycles to 30 seconds. Two attack scenarios were examined: (a) insider attacks where compromised nodes inject falsified readings, and (b) outsider eavesdropping and replay attacks. The proposed scheme was compared against (i) a classic pre‑distributed key scheme with full re‑keying after each topology change, and (ii) a centralized Bayesian trust manager that requires a sink‑side computation of trust.
Results
- Key management efficiency: The proposed protocol required on average 1.2 key refreshes per topology change, versus 3.8 for the baseline, yielding a 68 % reduction in key‑exchange messages.
- Energy consumption: Overall network power usage dropped by roughly 15 %, with the most pronounced savings in high‑mobility scenarios where frequent re‑keying would otherwise dominate energy budgets.
- Trust detection performance: The Grubbs‑based model achieved a 92 % detection rate for CF nodes and a false‑alarm rate of only 4 %, outperforming the Bayesian approach by about 7 % in both metrics.
- Data accuracy: The final aggregated values exhibited a normalized mean absolute error of 0.07, compared to 0.15 for the baseline, demonstrating that erroneous data were effectively suppressed before reaching the sink.
Discussion of limitations
The Grubbs test assumes normally distributed sensor readings; in environments where measurements follow heavy‑tailed or multimodal distributions, the test may produce excessive false positives or miss subtle attacks. Adaptive thresholding or alternative robust outlier detectors (e.g., Median Absolute Deviation) could mitigate this issue. Additionally, the sink can become a bottleneck when many nodes simultaneously request seed‑secret keys after a large-scale re‑configuration. The authors suggest employing multiple regional sinks or a hierarchical key‑distribution hierarchy to distribute the load. Finally, the current design relies on symmetric keys; long‑term key revocation and post‑compromise security are not addressed, opening avenues for hybrid asymmetric‑symmetric schemes or blockchain‑based distributed key management.
Conclusion
The paper delivers a practical, low‑overhead security solution for mobile sensor networks by unifying pair‑wise key distribution with a statistically grounded, distributed trust evaluation. Simulation results confirm that the approach substantially reduces key‑management traffic and energy consumption while maintaining high detection accuracy against insider and outsider threats. The work lays a solid foundation for future extensions, including robust outlier detection for non‑Gaussian data, decentralized key‑distribution architectures, and real‑world hardware validation.