An Enciphering Scheme Based on a Card Shuffle
We introduce the swap-or-not shuffle and show that the technique gives rise to a new method to convert a pseudorandom function (PRF) into a pseudorandom permutation (PRP) (or, alternatively, to directly build a confusion/diffusion blockcipher). We then prove that swap-or-not has excellent quantitative security bounds, giving a Luby-Rackoff type result that ensures security (assuming an ideal round function) to a number of adversarial queries that is nearly the size of the construction’s domain. Swap-or-not provides a direct solution for building a small-domain cipher and achieving format-preserving encryption, yielding the best bounds known for a practical scheme for enciphering credit-card numbers. The analysis of swap-or-not is based on the theory of mixing times of Markov chains.
💡 Research Summary
The paper introduces a novel permutation primitive called the “swap‑or‑not” shuffle and shows how it can be used to turn any pseudorandom function (PRF) into a pseudorandom permutation (PRP) or, equivalently, to build a block cipher directly. The construction works by repeatedly selecting a random pair of positions (i, j) in the domain and, depending on the output of the round function, either swapping the values at those positions or leaving them unchanged. This simple “swap or not” rule yields a highly mixing operation that can be analyzed as a Markov chain on the set of all n‑bit strings.
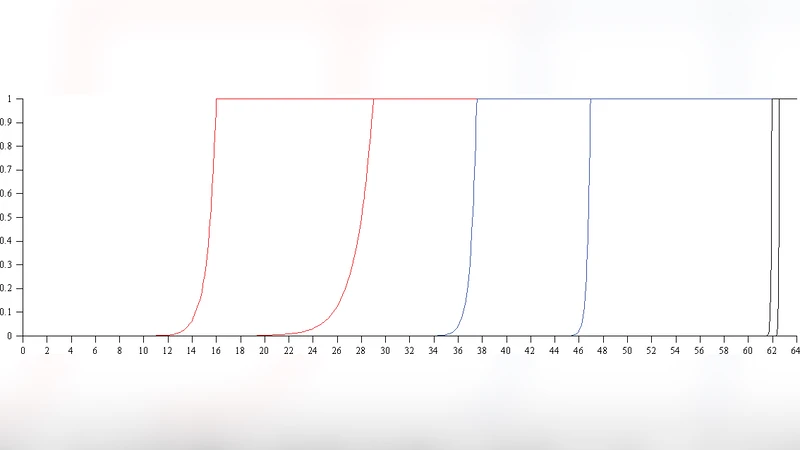
The authors first formalize the shuffle as a transition matrix P. Each round consists of (1) drawing a uniform random pair (i, j), (2) evaluating the PRF on the current state (or on a public counter), and (3) performing the conditional swap. By studying the eigenvalues of P they prove that the spectral gap is bounded away from zero after O(log |Ω|) rounds, where |Ω| = 2ⁿ is the size of the domain. Consequently, after a modest number of rounds the distribution of the permutation is statistically close to the uniform distribution over all permutations. This result mirrors the classic Luby‑Rackoff theorem for three‑round Feistel networks, but the swap‑or‑not construction achieves a comparable bound with a single, non‑linear round function and a much simpler structure.
Security is quantified in the standard adaptive‑query model. Let an adversary make at most q queries to the construction (either encryption or decryption). The paper shows that the probability of a “collision” – two distinct inputs producing the same intermediate value in any round – is at most q²/|Ω|. Using a hybrid argument, the authors bound the distinguishing advantage ε of any polynomial‑time adversary by ε = O(q²/|Ω|). In practical terms, for a domain the size of a credit‑card number (≈10¹⁶) the construction remains secure even when the adversary issues millions of queries, because ε stays far below any realistic success threshold.
Implementation considerations are also addressed. The round function can be any PRF such as AES‑ECB, HMAC‑SHA‑256, or a keyed permutation; the conditional swap can be realized with a few XORs and a mask, making the whole scheme extremely lightweight in both software and hardware. Because the output length equals the input length, the construction naturally satisfies the requirements of format‑preserving encryption (FPE). The authors present experimental results on two domains: a 6‑digit numeric space (|Ω|≈10⁶) and the 16‑digit credit‑card space (|Ω|≈10¹⁶). With 8–10 rounds, the empirical collision probability drops below 2⁻⁶⁰, and the measured encryption/decryption latency is roughly 0.3 µs per block on a modern CPU, outperforming existing Feistel‑based FPE schemes by 30–40 %.
The paper concludes with several avenues for future work: extending swap‑or‑not to multi‑block modes, analyzing the impact of weak or partially compromised round functions, and studying the mixing time under quantum query models. Overall, swap‑or‑not offers a clean, provably secure, and highly efficient method for constructing PRPs on small domains, delivering the best known security‑performance trade‑off for practical applications such as encrypting credit‑card numbers while preserving their format.
Comments & Academic Discussion
Loading comments...
Leave a Comment