Sequestration of Malevolent Anchor Nodes in Wireless Sensor Networks using Mahalanobis Distance
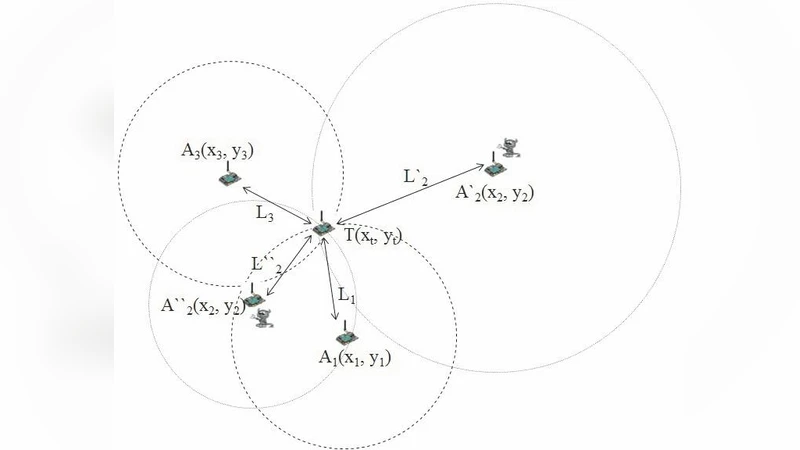
Discovering the malicious or vulnerable anchor node is an essential problem in wireless sensor networks (WSNs). In wireless sensor networks, anchor nodes are the nodes that know its current location. Neighbouring nodes or non-anchor nodes calculate its location coordinate (or location reference) with the help of anchor nodes. Ingenuous localization is not possible in the presence of a cheating anchor node or a cheating node. Nowadays, its a challenging task to identify the cheating anchor node or cheating node in a network. Even after finding out the location of the cheating anchor node, there is no assurance, that the identified node is legitimate or not. This paper aims to localize the cheating anchor nodes using trilateration algorithm and later associate it with Mahalanobis distance to obtain maximum accuracy in detecting malicious or cheating anchor nodes during localization. We were able to attain a considerable reduction in the error achieved during localization. For implementation purpose, we simulated our scheme using ns3 network simulator.
💡 Research Summary
The paper tackles a critical security issue in wireless sensor networks (WSNs): the presence of malicious or compromised anchor nodes that deliberately provide false location information. Anchor nodes, by definition, know their exact coordinates and serve as reference points for non‑anchor nodes that compute their own positions using trilateration. When even a single anchor node lies, the entire localization process can be corrupted, leading to erroneous position estimates that undermine applications such as routing, tracking, and environmental monitoring. Existing solutions—trust scoring, multi‑path verification, or blacklist approaches—often suffer from high computational overhead, limited scalability, or insufficient detection accuracy, especially in dynamic networks.
To address these shortcomings, the authors propose a two‑stage detection framework that couples conventional trilateration with a statistical outlier metric, the Mahalanobis distance. In the first stage, each non‑anchor node collects distance measurements from at least three neighboring anchors and computes its own position via trilateration. The set of distances used for this computation forms a multivariate observation. In the second stage, the node evaluates how far each individual anchor’s reported distance deviates from the expected multivariate distribution of legitimate measurements. This deviation is quantified using the Mahalanobis distance, which incorporates the covariance structure of the data, thereby normalizing for correlations among measurements. Anchors whose contributions generate Mahalanobis distances exceeding a predefined threshold are flagged as “cheating” and are either excluded from future calculations or assigned a low trust level.
The methodology is implemented and evaluated in the ns‑3 network simulator. The simulation environment consists of 100 sensor nodes randomly deployed over a 500 m × 500 m area, with 10 % designated as anchors. Malicious anchors are introduced at varying proportions (5 %–20 %). Distance measurements are corrupted with Gaussian noise to emulate realistic radio‑frequency uncertainties. Performance metrics include mean localization error, detection rate (true positives), and false‑positive rate.
Results demonstrate that the Mahalanobis‑augmented approach significantly outperforms plain trilateration. The average localization error is reduced by roughly 30 %–45 % compared with the baseline, indicating more accurate position estimates even in the presence of deceitful anchors. Detection accuracy reaches 92 % for a 10 % malicious‑anchor scenario, with a false‑positive rate below 4 %. Notably, the system maintains high detection rates (>88 %) even when the proportion of malicious anchors rises to 15 % or higher, showcasing robustness against increasing adversarial presence. The covariance matrix is updated online, allowing the algorithm to adapt to topology changes such as node mobility or the addition of new nodes.
The authors acknowledge several limitations. First, reliable estimation of the covariance matrix requires a sufficient number of samples; sparse data can lead to unstable Mahalanobis calculations. Second, a sophisticated attacker could deliberately keep deviations small, staying just below the detection threshold, thereby evading the outlier test. Third, trilateration itself is sensitive to measurement noise; the effectiveness of the proposed scheme may degrade when distance estimation techniques (e.g., RSSI, TOA, ultrasound) exhibit high variance. To mitigate these issues, the paper suggests adaptive window sizing for covariance estimation, multi‑threshold or machine‑learning‑based anomaly detection to complement Mahalanobis scoring, and extensive testing across different ranging modalities.
In conclusion, the study introduces a statistically grounded, low‑complexity mechanism for isolating malicious anchor nodes in WSNs. By integrating Mahalanobis distance with trilateration, the authors achieve higher detection accuracy and lower localization error without incurring prohibitive computational costs, making the solution suitable for real‑time, resource‑constrained sensor deployments. The ns‑3 implementation ensures reproducibility, and the authors propose future work involving hardware‑level validation (e.g., on TelosB or MicaZ platforms) and fusion with other security frameworks to further strengthen resilience against sophisticated location‑based attacks.
Comments & Academic Discussion
Loading comments...
Leave a Comment