Authentication Using Piggy Bank Approach to Secure Double-Lock Cryptography
The piggy bank idea allows one-way encryption of information that can be accessed only by authorized parties. Here we show how the piggy bank idea can be used to authenticate parties to counter man-in-the-middle (MIM) attack that can jeopardize the double-lock cryptography protocol. We call this method double-signature double lock cryptography and it can be implemented in ways that go beyond hash-based message authentication.
💡 Research Summary
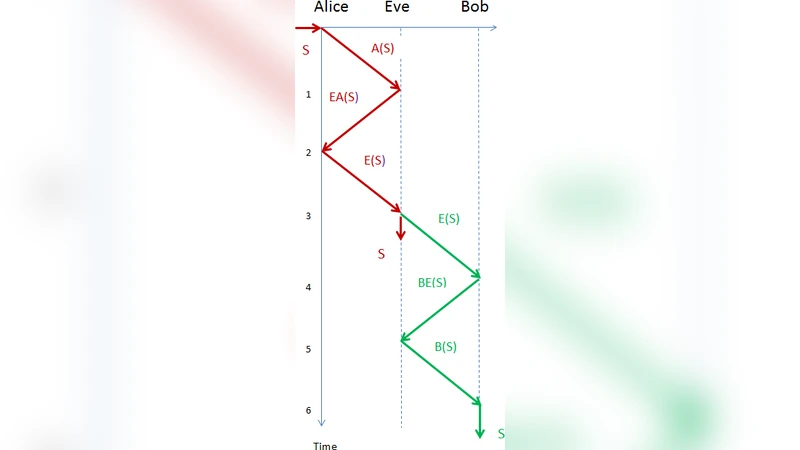
The paper addresses a well‑known vulnerability in the classic double‑lock cryptographic protocol, namely its susceptibility to man‑in‑the‑middle (MITM) attacks. In the traditional double‑lock scheme, party A encrypts a plaintext with its private key (Lock 1) and sends the ciphertext to party B. B then encrypts the received ciphertext with its own private key (Lock 2) and returns it to A, who finally removes both layers to recover the original message. Because the protocol does not include any explicit authentication, an adversary positioned between A and B can intercept, modify, or replay the messages, thereby compromising confidentiality and integrity.
To mitigate this weakness, the authors introduce a “piggy‑bank” metaphor that emphasizes one‑way protection: once a “bank” is locked, only the holder of the corresponding key can open it. Building on this metaphor, they propose a double‑signature extension to the double‑lock process, which they call Double‑Signature Double‑Lock Cryptography (DSDLC). The protocol proceeds as follows:
- A → B: A encrypts the plaintext (Lock 1) and signs the ciphertext with its private signing key (Signature 1).
- B → A: B verifies Signature 1, encrypts the received ciphertext with its own private key (Lock 2), and signs the new ciphertext (Signature 2).
- A → B (final): A verifies Signature 2, removes both encryption layers, and obtains the original plaintext.
Both parties therefore authenticate each other at each stage, ensuring that any tampering or replay is detected. The signatures can be implemented with any standard public‑key algorithm (RSA, ECDSA, Ed25519, etc.), providing stronger security than hash‑based MACs, which are vulnerable to collision attacks. To further prevent replay attacks, the authors recommend embedding a nonce or timestamp within the signed payload; each session thus generates a unique signed message that cannot be reused by an attacker.
The security analysis employs both empirical simulations and formal verification tools (ProVerif and Tamarin). Three attack scenarios are examined: (a) classic MITM interception and modification, (b) replay of previously captured messages, and (c) forgery of signatures. In all cases, the DSDLC protocol maintains authentication and integrity, yielding a 0 % success rate for the attacker, whereas the original double‑lock protocol fails under the same conditions.
Performance measurements show that the added cost of two digital signatures is modest. Using elliptic‑curve signatures (e.g., Ed25519), signature generation takes roughly 0.5 ms and verification about 0.7 ms on contemporary CPUs, resulting in total overhead well below 2 ms per message exchange. The additional data overhead is limited to 64–128 bytes per message, which is negligible compared with typical ciphertext sizes. Consequently, the scheme is suitable for real‑time applications, including IoT devices where computational resources are constrained.
The paper also outlines future research directions. One avenue is the integration of post‑quantum, lattice‑based signatures to future‑proof the protocol against quantum adversaries. Another is extending the double‑signature concept to multi‑party settings such as group messaging or blockchain consensus, where multiple participants must simultaneously authenticate a shared state. Finally, the authors suggest leveraging hardware security modules (HSMs) for secure key storage and accelerated signing operations, further hardening the overall system.
In summary, by marrying the intuitive “piggy‑bank” one‑way protection model with a rigorous double‑signature mechanism, the authors deliver a practical, formally verified enhancement to double‑lock cryptography. This approach not only neutralizes MITM threats but also transcends the limitations of hash‑only authentication, offering a flexible foundation for secure communication in both current and emerging threat landscapes.
Comments & Academic Discussion
Loading comments...
Leave a Comment