An exhaustive survey of trust models in p2p network
Most of the peers accessing the services are under the assumption that the service accessed in a P2P network is utmost secured. By means of prevailing hard security mechanisms, security goals like authentication, authorization, privacy, non repudiation of services and other hard security issues are resolved. But these mechanisms fail to provide soft security. An exhaustive survey of existing trust and reputation models in P2P network regarding service provisioning is presented and challenges are listed.p2p Trust issues like trust bootstrapping, trust evidence procurement, trust assessment, trust interaction outcome evaluation and other trust based classification of peers behaviour into trusted, inconsistent, un trusted, malicious, betraying, redemptive are discussed.
💡 Research Summary
The paper addresses a critical gap in peer‑to‑peer (P2P) service environments: while traditional “hard” security mechanisms—authentication, authorization, privacy protection, and non‑repudiation—effectively mitigate many technical threats, they do not provide the “soft” security needed to assess and manage trust among participating peers. To fill this void, the authors present an exhaustive survey of existing trust and reputation models that have been proposed for service provisioning in P2P networks, and they systematically categorize the entire trust lifecycle.
The survey begins with trust bootstrapping, reviewing how initial trust values are assigned to previously unknown peers. Approaches include centralized authority‑based schemes, social‑network‑derived recommendations, random initialization, and Bayesian prior models. Each method is evaluated in terms of initialization accuracy, scalability, and susceptibility to single‑point‑of‑failure attacks.
Next, the paper examines trust evidence procurement. It distinguishes between direct evidence (transaction logs, observed behavior) and indirect evidence (recommendations, referrals, external sensor data). The authors discuss weighting strategies that consider source reliability, recency, and context, and they analyze conflict resolution techniques such as Dempster‑Shafer theory for merging contradictory reports.
The core of the survey is trust assessment. A wide spectrum of techniques is compared: probabilistic models (Bayesian inference, Markov chains), fuzzy logic systems, neural networks (including recurrent and long‑short‑term memory architectures), clustering‑based methods, and the more recent graph‑neural‑network (GNN) approaches that capture complex peer‑to‑peer relationships. For each technique the authors discuss handling of uncertainty, data requirements, computational overhead, and suitability for real‑time updates. Multi‑dimensional trust—covering quality of service, reliability, and security—is also addressed, as is the extension of models across multiple service domains (file sharing, streaming, distributed computation).
The fourth component, trust interaction outcome evaluation, focuses on how post‑interaction metrics (QoS, latency, success rate, cost) are integrated to update a peer’s trust score. The survey contrasts simple weighted averages, multi‑criteria decision‑making (MCDM) frameworks, and reinforcement‑learning‑based reward functions that enable adaptive trust updates.
A novel contribution of the paper is the behavioral classification taxonomy. Beyond the traditional binary division of “trusted” vs. “untrusted,” the authors define six categories: trusted, inconsistent, untrusted, malicious, betraying, and redemptive. For each class they outline detection mechanisms (anomaly detection, pattern analysis) and response strategies (isolation, reputation penalties, trust‑recovery protocols).
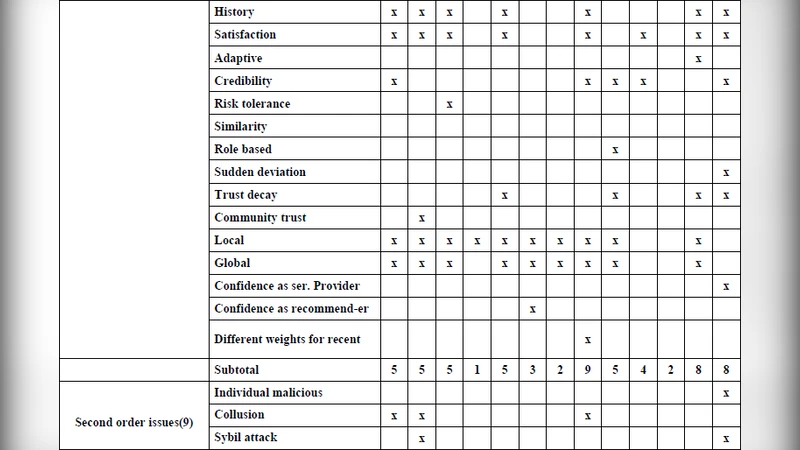
Finally, the authors identify several open challenges that limit current trust models: (1) insufficient real‑time adaptability to dynamic network conditions; (2) vulnerability to coordinated attacks such as Sybil, Eclipse, and collusion; (3) tension between privacy preservation and the need for transparent trust evidence; (4) scalability of trust propagation and malicious‑peer detection in large‑scale networks; and (5) the lack of immutable, verifiable trust records. To address these issues, the paper proposes a forward‑looking research agenda that combines continuous online learning, privacy‑preserving federated learning, and blockchain‑based immutable ledgers with smart‑contract‑driven trust updates.
In conclusion, the survey demonstrates that effective trust management in P2P networks must transcend static, single‑dimensional scoring systems. It must incorporate dynamic, multi‑dimensional assessment, robust evidence aggregation, privacy‑aware data handling, and tamper‑proof record keeping. The authors argue that future work should aim at building a scalable, privacy‑friendly, blockchain‑anchored trust infrastructure capable of supporting the heterogeneous and ever‑evolving landscape of P2P services.
Comments & Academic Discussion
Loading comments...
Leave a Comment