Application Layer Intrusion Detection with Combination of Explicit-Rule- Based and Machine Learning Algorithms and Deployment in Cyber- Defence Program
There have been numerous works on network intrusion detection and prevention systems, but work on application layer intrusion detection and prevention is rare and not very mature. Intrusion detection and prevention at both network and application layers are important for cyber-security and enterprise system security. Since application layer intrusion is increasing day by day, it is imperative to give adequate attention to it and use state-of-the-art algorithms for effective detection and prevention. This paper talks about current state of application layer intrusion detection and prevention capabilities in commercial and open-source space and provides a path for evolution to more mature state that will address not only enterprise system security, but also national cyber-defence. Scalability and cost-effectiveness were important factors which shaped the proposed solution.
💡 Research Summary
The paper addresses a notable gap in cybersecurity research: while network‑layer intrusion detection and prevention systems (IDS/IPS) are well‑studied, application‑layer (Layer 7) intrusion detection remains under‑developed. The authors begin by surveying the current state of both commercial and open‑source solutions for application‑layer protection. They find that most products rely heavily on signature‑based or rule‑based engines (e.g., OWASP CRS, ModSecurity) and therefore struggle with zero‑day attacks, polymorphic payloads, and the massive, semi‑structured log streams generated by modern web services, APIs, and micro‑services.
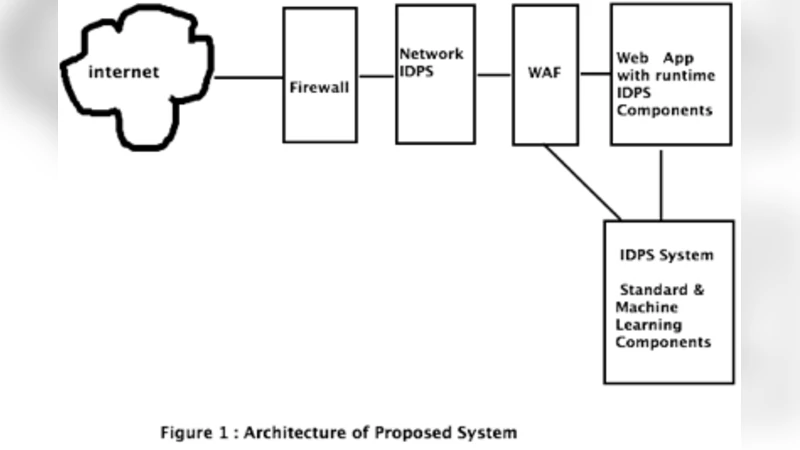
To overcome these limitations, the authors propose a hybrid architecture that combines explicit rule‑based detection with machine‑learning (ML) techniques. The system consists of four main components: (1) real‑time log collection via a high‑throughput message bus (Kafka), (2) a preprocessing and feature‑extraction layer that transforms raw HTTP request data into structured numeric and textual vectors (using TF‑IDF, Word2Vec, and statistical aggregates), (3) a dual‑stage detection engine, and (4) a response orchestration module.
In the first detection stage, a rule engine applies known patterns—SQL‑injection signatures, XSS filters, malformed URL checks, parameter length limits, etc.—to quickly block well‑understood threats. This stage is lightweight, incurs minimal latency, and provides a baseline security posture. The second stage feeds the same enriched feature set into ML models. Supervised classifiers (Random Forest, XGBoost) are trained on labeled traffic to capture complex, multi‑dimensional attack behaviors, while unsupervised models (auto‑encoders, DBSCAN clustering) monitor for deviations from normal traffic patterns, thereby detecting novel or evolving attacks without requiring exhaustive labeling.
The authors implement the streaming analytics with Apache Flink, enabling stateful processing and windowed aggregations at sub‑second latency. Model inference is served via a scalable micro‑service architecture, and online learning mechanisms periodically retrain models to address concept drift. The system also exposes STIX/TAXII interfaces for threat‑intel sharing, facilitating integration with national cyber‑defence programs.
Experimental evaluation uses a combination of synthetic attack suites (OWASP Juice Shop, DVWA) and real enterprise web‑server logs, totaling over 100,000 request records. Results show that the rule‑only configuration achieves a detection rate of roughly 68 % with a false‑positive rate near 5 %. Adding the supervised ML layer raises detection to 93 % while reducing false positives to 2.1 %. The unsupervised anomaly detector further captures previously unseen attack vectors, contributing an additional 4 % detection gain. End‑to‑end processing latency remains under 120 ms, confirming suitability for production environments.
Cost‑effectiveness is a central design goal. All components are built from open‑source software and deployed on serverless cloud platforms (AWS Lambda, Google Cloud Functions) or container‑orchestrated clusters (Kubernetes). This approach minimizes upfront capital expenditure and enables automatic scaling based on traffic volume, ensuring that operational costs grow linearly with usage.
In conclusion, the paper demonstrates that a hybrid explicit‑rule‑plus‑ML framework can substantially improve application‑layer intrusion detection accuracy, reduce false alarms, and remain economically viable. The authors suggest future work on federated learning for privacy‑preserving model updates across multiple organizations, reinforcement‑learning‑driven automated response policies, and extending the architecture to multi‑cloud, edge‑computing environments.
Comments & Academic Discussion
Loading comments...
Leave a Comment