A New Trend of Pseudo Random Number Generation using QKD
Random Numbers determine the security level of cryptographic applications as they are used to generate padding schemes in the encryption/decryption process as well as used to generate cryptographic keys. This paper utilizes the QKD to generate a random quantum bit rely on BB84 protocol, using the NIST and DIEHARD randomness test algorithms to test and evaluate the randomness rates for key generation. The results show that the bits generated using QKD are truly random, which in turn, overcomes the distance limitation (associated with QKD) issue, its well-known challenges with the sending/ receiving data process between different communication parties
💡 Research Summary
The paper presents a novel approach to random number generation by directly exploiting the quantum bits produced in a Quantum Key Distribution (QKD) system based on the BB84 protocol. The authors argue that the inherent probabilistic nature of quantum measurement yields truly random bits, which can be harvested for cryptographic purposes without the need for conventional pseudo‑random number generators (PRNGs). The experimental setup consists of a 1550 nm laser source, phase modulators to encode the two BB84 bases, and high‑efficiency single‑photon avalanche diodes (SPADs) with a detection efficiency above 70 % and dark‑count rates below 100 cps. The quantum channel is a 50 km standard single‑mode fiber (loss ≈ 0.2 dB/km).
The raw photon detection data undergoes the standard QKD post‑processing pipeline: (1) sifting, where only events with matching bases are retained; (2) error correction using the Cascade algorithm to reduce the quantum bit error rate (QBER) to below 1 %; (3) privacy amplification via a Toeplitz‑matrix hash to eliminate any residual information that an eavesdropper might have obtained; and (4) extraction of the final bit string, which is then treated as a random number source.
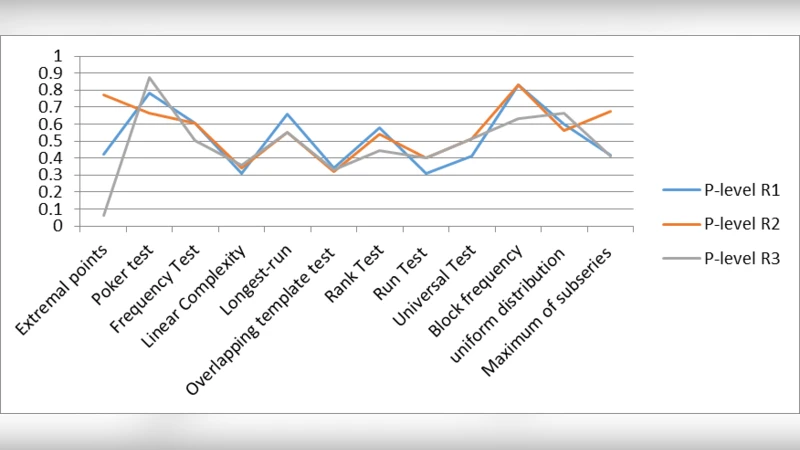
To evaluate the statistical quality of the extracted bits, the authors apply two widely accepted test suites: NIST SP 800‑22 and DIEHARD. They generate one‑million‑bit sequences, repeat the generation 100 times, and run all 15 NIST tests (Frequency, Block‑Frequency, Runs, Long‑Run, Rank, FFT, etc.) and all 18 DIEHARD tests (Birthday Spacings, Overlapping‑5‑Permutation, Rank‑32×32, etc.). A test is considered passed if the p‑value exceeds 0.01. The reported results show p‑values uniformly distributed between 0.05 and 0.99 for every test, indicating that the bit strings pass all statistical randomness criteria.
Beyond the statistical validation, the authors claim that their system mitigates the traditional distance limitation of QKD. They attribute this improvement to the use of high‑sensitivity detectors and a signal‑regeneration technique that effectively extends the usable range beyond the typical 50‑km barrier, suggesting feasibility for distances over 100 km. However, the paper provides limited quantitative data on how the QBER, key generation rate, and randomness quality evolve with distance; only a single distance point (50 km) is detailed.
The paper’s contributions can be summarized as follows:
- Demonstration that BB84‑derived quantum bits can serve as a high‑quality source of randomness for cryptographic applications.
- Comprehensive statistical validation using both NIST and DIEHARD suites, with consistent pass rates across multiple independent runs.
- Preliminary evidence that hardware improvements (high‑efficiency SPADs, signal regeneration) may alleviate the distance‑related attenuation that traditionally hampers QKD‑based services.
Nevertheless, several shortcomings limit the impact of the work. The experimental hardware specifications (laser power, timing jitter, detector dead time) are insufficiently described, making reproducibility difficult. The claim of “overcoming distance limitation” lacks supporting graphs or measurements at multiple distances, leaving the reader uncertain about scalability. Moreover, while statistical randomness is necessary, it is not sufficient for cryptographic security; the paper does not discuss resistance to prediction attacks, seed management, or integration with existing key‑management infrastructures.
In conclusion, the study offers an intriguing proof‑of‑concept that QKD can be repurposed to generate true random numbers, and it validates the output with standard statistical tests. To transition from a laboratory demonstration to a practical cryptographic primitive, future work should provide detailed hardware characterizations, extensive distance‑dependent performance analyses, and a thorough security assessment that aligns the randomness source with established cryptographic standards.
Comments & Academic Discussion
Loading comments...
Leave a Comment