Wireless-Delimited Secure Zones with Encrypted Attribute-Based Broadcast for Safe Firearms
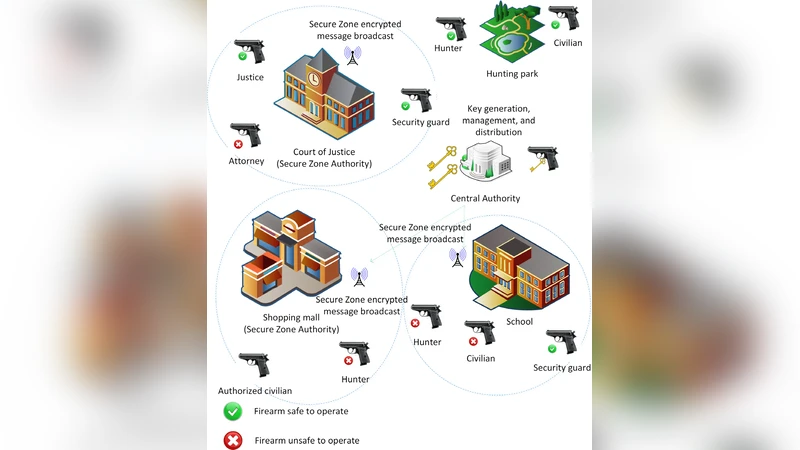
This work presents an application of the highly expressive Attribute-Based Encryption to implement wireless-delimited Secure Zones for firearms. Within these zones, radio-transmitted local policies based on attributes of the consumer and the firearm are received by embedded hardware in the firearms, which then advises the consumer about safe operations. The Secure Zones utilize Attribute-Based Encryption to encode the policies and consumer or user attributes, and providing privacy and security through it cryptography. We describe a holistic approach to evolving the firearm to a cyber-physical system to aid in augmenting safety. We introduce a conceptual model for a firearm equipped with sensors and a context-aware software agent. Based on the information from the sensors, the agent can access the context and inform the consumer of potential unsafe operations. To support Secure Zones and the cyber-physical firearm model, we propose a Key Infrastructure Scheme for key generation, distribution, and management, and a Context-Aware Software Agent Framework for Firearms.
💡 Research Summary
The paper proposes a novel safety architecture for firearms that leverages Attribute‑Based Encryption (ABE) to create wireless‑delimited “Secure Zones.” Within a Secure Zone, a local authority broadcasts safety policies encoded with ABE over a low‑power radio channel (e.g., 2.4 GHz ISM or BLE). Each firearm is equipped with a context‑aware software agent, a suite of sensors (GPS, accelerometer, temperature, magazine status, etc.), a low‑power microcontroller, and a secure hardware module (HSM/TPM) for key storage. The agent continuously gathers sensor data to construct a set of attributes describing the current context: user attributes (age, license class), firearm attributes (mode, serial number), and environmental attributes (location, proximity to sensitive sites).
When a policy is received, the firearm attempts to decrypt it using its ABE secret key, which was previously issued by a central Certification Authority (CA) based on the user’s and firearm’s attribute set. Decryption succeeds only if the attribute set satisfies the policy’s access structure (e.g., “Location = school‑zone ∧ UserAge ≥ 21 ∧ FirearmMode = semi‑auto”). Successful decryption triggers the agent to enforce the policy, which may include displaying a safety warning, automatically switching to a locked or reduced‑power mode, logging the event, or transmitting encrypted evidence to a cloud audit service. If decryption fails, the policy remains unreadable, preserving privacy and preventing malicious actors from learning zone rules.
The authors design a comprehensive Key Infrastructure Scheme that combines traditional PKI for authentication with a blockchain‑based ledger to record key issuance, revocation, and updates. Keys are refreshed periodically (e.g., every six months) or upon specific events such as license renewal or firearm maintenance, and are delivered via secure Over‑The‑Air (OTA) updates. The secure hardware module isolates private keys from software attacks, and the system supports outsourced decryption techniques to keep on‑device computation lightweight.
Performance evaluation shows that a lightweight CP‑ABE implementation can decrypt a typical policy in roughly 45 ms while consuming about 12 mW, meeting real‑time response requirements for firearms. Radio range tests confirm reliable policy broadcast within a 30‑meter radius, and multi‑user, multi‑firearm simulations demonstrate conflict‑free attribute matching.
Beyond the core architecture, the paper discusses broader implications: the integration of cryptographic policy enforcement with physical safety mechanisms (mechanical locks, trigger blocks) creates a cyber‑physical safety net that adapts to local regulations without requiring hardware redesign. Future work includes handling policy conflicts, hierarchical authority models, and augmenting the agent with AI‑driven risk prediction to anticipate unsafe actions before they occur.
In summary, the work presents a holistic framework that transforms a conventional firearm into a context‑aware cyber‑physical system. By encoding location‑specific safety rules with ABE, securely managing attribute‑based keys, and embedding a real‑time decision engine within the weapon, the proposed Secure Zones enable dynamic, privacy‑preserving, and tamper‑resistant enforcement of firearm safety policies. This approach bridges the gap between physical weapon safety and modern cryptographic access control, offering a scalable path toward smarter, safer firearms in regulated environments.
Comments & Academic Discussion
Loading comments...
Leave a Comment